Suppressing Epidemics with a Limited Amount of Immunization Units
The way diseases spread through schools, epidemics through countries, and viruses through the Internet is crucial in determining their risk. Although each of these threats has its own characteristics, its underlying network determines the spreading. To restrain the spreading, a widely used approach is the fragmentation of these networks through immunization, so that epidemics cannot spread. Here we develop an immunization approach based on optimizing the susceptible size, which outperforms the best known strategy based on immunizing the highest-betweenness links or nodes. We find that the network’s vulnerability can be significantly reduced, demonstrating this on three different real networks: the global flight network, a school friendship network, and the internet. In all cases, we find that not only is the average infection probability significantly suppressed, but also for the most relevant case of a small and limited number of immunization units the infection probability can be reduced by up to 55%.
💡 Research Summary
The paper addresses the fundamental problem of how to most efficiently allocate a limited number of immunization resources (vaccines, screenings, patches, etc.) in order to suppress epidemic spreading on complex networks. While previous work has largely focused on targeted immunization based on adaptive betweenness centrality—removing at each step the node or edge that lies on the greatest number of shortest paths—the authors argue that this approach optimizes only the percolation threshold and ignores the full course of an outbreak.
To overcome this limitation, the authors introduce a global performance metric called the “susceptible size” R, defined as the cumulative sum of the sizes of the largest connected component of the non‑immunized sub‑network over all possible numbers q of immunized elements (from 0 up to N). R therefore represents an upper bound on the number of individuals that could become infected if an outbreak starts at any point in the remaining network. Minimizing R ensures that the network stays fragmented throughout the entire immunization process, not just at a single critical point.
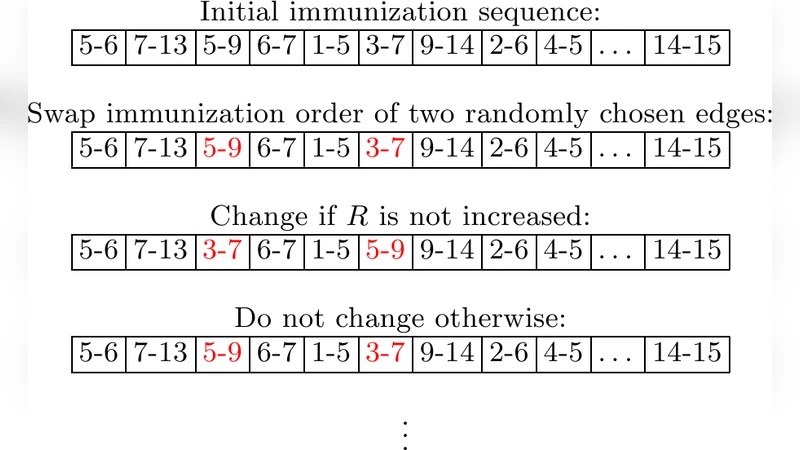
The proposed optimization proceeds in two stages. First, an initial immunization sequence is generated using the standard adaptive betweenness algorithm (HBA). Second, the sequence is refined by stochastic swaps: two randomly chosen nodes or edges exchange their positions in the order, and the new sequence is accepted only if it does not increase R. Repeating this local search thousands of times yields a substantially improved ordering. To further escape local minima, a population‑based meta‑heuristic is employed: a pool of 1 000 candidate sequences evolves by repeatedly applying the swap operation and replacing the worst‑performing member with a better one. The final sequence with the smallest R is taken as the optimal immunization strategy.
Although the method requires repeated betweenness calculations and R evaluations—making it computationally heavier than plain HBA—it scales acceptably for networks up to N≈8 000 and M≈16 000, completing in a few hours on a standard workstation.
The authors evaluate the approach on three real‑world networks and two synthetic models. The real networks are: (i) the global airline network (N = 3 666, M = 27 235), where node immunization corresponds to screening all passengers at an airport and edge immunization to checking specific flights; (ii) a US school friendship network (N = 1 461, M = 3 875), where node immunization means vaccinating or isolating students and edge immunization means preventing direct contacts; (iii) an Internet point‑of‑presence (PoP) network (N = 1 098, M = 6 089), where node immunization is router hardening and edge immunization is traffic filtering. Synthetic tests use Erdős‑Rényi graphs (N = 8 000, M = 16 000) and scale‑free graphs (N = 4 000, degree exponent γ = 2.5).
Across all datasets, the optimized strategy consistently outperforms the baseline HBA. For the airline network, average infection probability drops by about 15 % when fewer than 20 % of flights are immunized, with a peak reduction of 55 % at around 12 % immunized edges. Similar gains are observed for the school network (≈7 % average, 45 % peak) and the Internet (≈15 % average, 24 % peak). The reduction in susceptible size R translates into concrete “savings” of immunization units: the optimized method needs 9 %–21 % fewer resources to keep the maximal outbreak size below a given threshold. In synthetic networks, the improvement is even more pronounced: R is reduced by roughly 30 % on Erdős‑Rényi graphs, and the largest component that could be infected shrinks by up to a factor of five for small immunization budgets.
The study demonstrates that optimizing the entire immunization sequence with respect to a global fragmentation metric yields substantially better protection than focusing solely on betweenness. The method works for both node‑ and edge‑based immunization, though edge immunization generally provides larger gains because it directly targets the pathways of transmission.
Limitations include the requirement of full knowledge of the network topology and the assumption of static connections; real‑world contact patterns often evolve over time, and data may be incomplete. Future work could explore approximate algorithms that operate with partial information, dynamic updating of the immunization order as the network changes, and integration with realistic logistical constraints (e.g., geographic distribution of vaccines).
In conclusion, the paper provides a robust, globally optimal immunization framework that significantly enhances epidemic control under resource constraints, offering a valuable tool for public health planners, cybersecurity professionals, and any domain where contagion processes on networks must be mitigated.
Comments & Academic Discussion
Loading comments...
Leave a Comment