ECAKP: Encrypt Collect Authenticate Kill Play
We are taught from a young age that plagiarism (copying other’s work) is wrong. However, the problem of Illegal copies of multimedia data is exacerbated by the widespread availability of circumvention devices, which enable people to make infringing copies of multimedia data. Recently, Joint Video Compression and Encryption (JVCE) has gained increased attention to reduce the computational complexity of video compression, as well as provide encryption of multimedia data. In this paper, a novel protection method for multimedia data (ECAKP) is proposed. It combines encryption process and compression with authenticating process. The method had been implemented and the results are discussed in detail.
💡 Research Summary
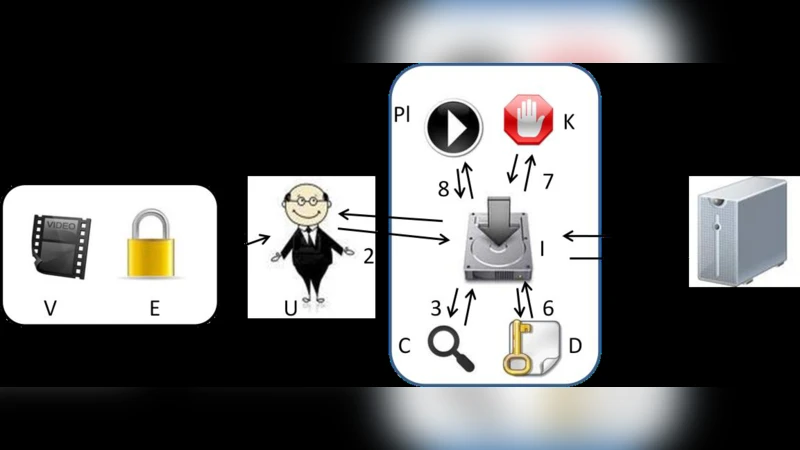
The paper introduces a novel multimedia protection framework called ECAKP, which stands for Encrypt‑Collect‑Authenticate‑Kill‑Play. The authors argue that existing solutions typically treat encryption/compression and user authentication as separate concerns, leaving a gap in comprehensive protection against illegal copying and distribution of multimedia content. ECAKP bridges this gap by integrating five distinct phases into a single workflow.
In the first phase (Encrypt), the original multimedia file (V) is encrypted using a randomly generated nonce (R_E) and a symmetric cipher (the exact algorithm is not specified, but AES‑like security is implied). The encrypted stream is then compressed with GZIP/Deflate, and a unique file identifier (ID_M) along with compression metadata is embedded in the header.
The second phase (Collect) occurs during installation. The installer (I) prompts the user for the file identifier and an e‑mail address, then creates a hardware fingerprint of the host PC by hashing components such as CPU ID, MAC address, and disk serial numbers. This fingerprint becomes the PC_ID.
During the third phase (Authenticate), the client sends both ID_M and PC_ID to a remote licensing server (S). The server consults a pre‑populated database of authorized purchases and applies one of four policy modes: (1) monitoring‑only, (2) massive‑fraud‑prevention, (3) fair‑use, or (4) strict‑enforcement. Depending on the policy, the server either logs the request, rejects it, or issues a license file (F_ID_PC) tied to the specific PC_ID.
Phase four (Kill) uses the received license file to decrypt and decompress the protected multimedia file, then aggressively disables any processes that could be used to record the screen, create virtual CD images, or maintain an internet connection. The implementation enumerates a whitelist of essential system processes (e.g., svchost, explorer, notepad) and terminates all others, thereby mitigating screen‑capture attacks.
Finally, in the Play phase, the decrypted video is handed to a custom player for playback. After playback, temporary files are deleted to prevent residual data leakage.
The authors validated ECAKP in a real‑world setting at Helwan University’s Faculty of Science. A programming course traditionally required the purchase of about 400 printed textbooks per semester. The authors replaced the textbook with a protected CD containing video lectures, text, and interactive quizzes. Although initial adoption was slow due to concerns about activation, the final enrollment saw 190 CDs sold, 182 successful activations, and only 8 users who never attempted activation. A post‑course survey revealed that 94.5 % of respondents purchased the CD primarily for video access, and additional motivations included cost savings, intellectual‑property protection, and enhanced learning flexibility.
The paper concludes that ECAKP offers a low‑cost, effective protection mechanism suitable for educational multimedia distribution. It deters piracy without requiring expensive hardware dongles or third‑party DRM solutions. The authors acknowledge limitations such as reliance on administrator privileges for process termination, sensitivity of hardware fingerprints to OS upgrades, and the lack of detailed cryptographic specifications. Future work is proposed to incorporate selective encryption during compression to speed up decryption and to strengthen key management and integrity verification for higher‑value commercial content.
Comments & Academic Discussion
Loading comments...
Leave a Comment