A New IRIS Normalization Process For Recognition System With Cryptographic Techniques
Biometric technologies are the foundation of personal identification systems. It provides an identification based on a unique feature possessed by the individual. This paper provides a walkthrough for image acquisition, segmentation, normalization, feature extraction and matching based on the Human Iris imaging. A Canny Edge Detection scheme and a Circular Hough Transform, is used to detect the iris boundaries in the eye’s digital image. The extracted IRIS region was normalized by using Image Registration technique. A phase correlation base method is used for this iris image registration purpose. The features of the iris region is encoded by convolving the normalized iris region with 2D Gabor filter. Hamming distance measurement is used to compare the quantized vectors and authenticate the users. To improve the security, Reed-Solomon technique is employed directly to encrypt and decrypt the data. Experimental results show that our system is quite effective and provides encouraging performance. Keywords: Biometric, Iris Recognition, Phase correlation, cryptography, Reed-Solomon
💡 Research Summary
The paper presents an iris‑based biometric recognition system that integrates a novel normalization step based on phase‑correlation image registration and a security layer that employs Reed‑Solomon error‑correction codes as a cryptographic primitive. The authors follow the conventional five‑stage pipeline—acquisition, segmentation, normalization, encoding, and matching—but introduce specific algorithmic choices at each stage.
In the segmentation stage, a Canny edge detector is first applied to generate an edge map of the eye image. The circular Hough transform is then used to locate the inner (pupil) and outer (iris) boundaries, while a parabolic Hough transform approximates the upper and lower eyelids. The paper does not provide detailed parameter settings for Canny (e.g., low/high thresholds) or for the Hough voting process, which raises concerns about reproducibility, especially under varying illumination or occlusion conditions.
Normalization is performed by aligning the segmented iris to a reference using phase correlation. The method exploits the Fourier shift property: a spatial translation between two images appears as a linear phase difference in the frequency domain. By computing the normalized cross‑power spectrum and locating its peak, the algorithm estimates the translation parameters (dx, dy). The authors claim to extend this to handle rotation and scaling through an iterative minimization of a similarity‑transform cost function, but they omit explicit equations, convergence criteria, or computational complexity analysis. After registration, the iris texture is unwrapped from Cartesian to polar coordinates, producing a rectangular “normalized” image that serves as the input for feature extraction.
Feature extraction uses a bank of 2‑D Gabor filters. Each filter is defined by a sinusoidal carrier modulated by a Gaussian envelope, with specific frequency and orientation parameters. Convolution of the normalized iris with these filters yields complex responses; the phase information is quantized into a binary IrisCode. The authors also generate a noise mask that flags pixels corrupted by eyelash or eyelid occlusion, but the mask creation algorithm is not described in detail.
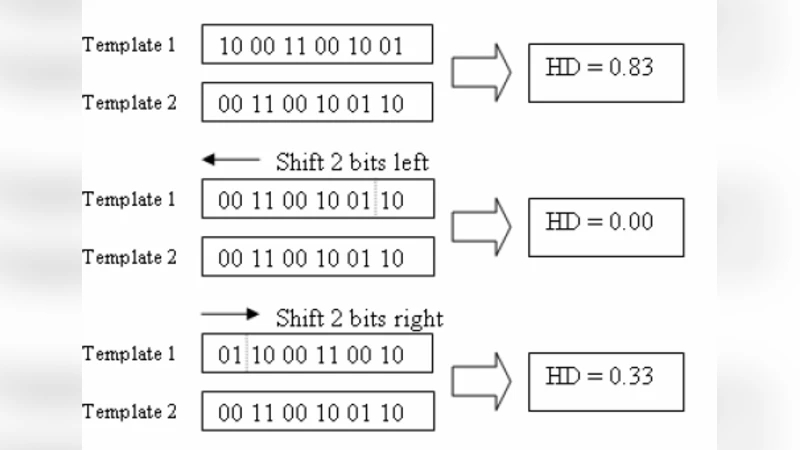
Matching relies on the Hamming distance between two IrisCodes, ignoring masked bits. The distance is computed as the proportion of disagreeing bits over the total number of unmasked bits. A low Hamming distance indicates a match. No threshold selection strategy or ROC analysis is presented, making it difficult to assess false‑accept and false‑reject rates.
The security contribution consists of applying Reed‑Solomon (RS) codes directly to the IrisCode. The authors first split the binary code into blocks of k bits, interpret each block as an integer, and map it to a row of a Hadamard matrix for an additional XOR operation. Because Hadamard correction alone is insufficient for burst errors caused by eyelash occlusion, RS codes are layered on top to provide robust error correction. During enrollment, the IrisCode is encoded with RS; during verification, the received code is decoded, correcting errors before the Hamming distance is computed. However, the paper does not discuss key management, the size of the finite field, or how the RS parity symbols are protected against tampering. Consequently, the claim of “cryptographic” security is not fully substantiated.
Experimental results are reported in two scenarios. Using a single image pair, the system achieves a 60 % correct‑accept rate; when multiple images per iris are stored, the rate rises to 93.6 %. The authors compare RS‑based error correction with other techniques, showing a performance gain, but they provide no details about the dataset (number of subjects, acquisition conditions), baseline algorithms, or statistical significance. No computational time or memory usage analysis is offered, which is critical for real‑time biometric deployment.
In conclusion, the paper demonstrates a complete iris‑recognition pipeline that combines phase‑correlation registration and Reed‑Solomon error correction. While the integration of these components is conceptually interesting, the manuscript lacks essential implementation details, rigorous experimental methodology, and thorough security analysis. Future work should address parameter optimization, extensive benchmarking against state‑of‑the‑art methods (e.g., Daugman’s algorithm, deep‑learning based encoders), and a formal threat model for the RS‑based cryptographic layer.
Comments & Academic Discussion
Loading comments...
Leave a Comment