Steganography and Steganalysis: Different Approaches
Steganography is the technique of hiding confidential information within any media. Steganography is often confused with cryptography because the two are similar in the way that they both are used to protect confidential information. The difference between the two is in the appearance in the processed output; the output of steganography operation is not apparently visible but in cryptography the output is scrambled so that it can draw attention. Steganlysis is process to detect of presence of steganography. In this article we have tried to elucidate the different approaches towards implementation of steganography using ‘multimedia’ file (text, static image, audio and video) and Network IP datagram as cover. Also some methods of steganalysis will be discussed.
💡 Research Summary
The paper provides a broad survey of steganography techniques across four major media types—text, still images, audio/video, and IP datagrams—and discusses corresponding steganalysis methods. It begins by defining the basic components of a steganographic system: the cover (C), the secret message (M), the stego function (Fₑ) and its inverse, and an optional stego‑key (K). The authors then categorize modern approaches according to the carrier medium.
For text, two simple schemes are described. The first uses a pre‑shared integer sequence as a key to select characters from specific positions in the cover text; a “0” indicates a space. The second embeds information in the number of extra spaces between words, mapping each count to a lookup table entry. Both methods are easy to implement but are fragile to reformatting or editing of the text.
Image steganography focuses on the Least Significant Bit (LSB) technique for uncompressed bit‑maps and on LSB manipulation of quantized DCT coefficients for JPEG images. The LSB method replaces the lowest bit of each color component with secret bits, which is straightforward but highly vulnerable to compression, scaling, and filtering. The JPEG‑based approach divides the image into 8×8 blocks, applies DCT, quantizes the coefficients, substitutes the LSB of selected coefficients with secret bits, and then re‑encodes the image. This method survives JPEG compression better but requires careful handling of quantization noise to avoid perceptible artifacts.
Audio and video steganography exploit the limitations of the Human Auditory System (HAS) and the Human Visual System (HVS). The paper outlines several audio techniques: LSB coding of sampled data, phase coding (embedding bits as phase shifts), spread‑spectrum methods (direct‑sequence and frequency‑hopping), and echo hiding (modulating echo amplitude, decay, and offset). Video steganography is presented as a natural extension, embedding data into individual frames using the same image and audio methods, with a scaling factor α controlling the strength of embedding across pixels and frames.
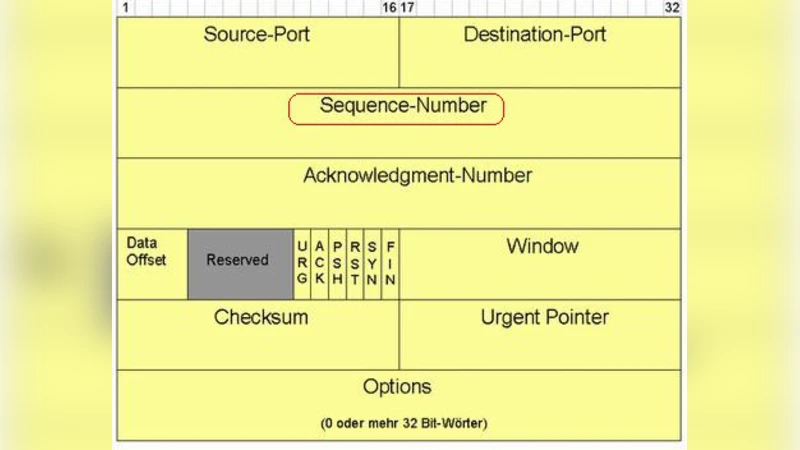
Network steganography is introduced as “covert channel” communication at the IP layer. The authors illustrate three header‑based carriers: the 3‑bit Flags field (particularly the DF bit) and the 13‑bit fragment offset in IPv4, the 16‑bit Identification field, and the 32‑bit Initial Sequence Number (ISN) in TCP. By agreeing on the path MTU and ensuring packets remain unfragmented, two parties can encode binary data in these fields without altering payload data, making detection by conventional IDS difficult. The paper also mentions UDP source ports, checksums, and ICMP code fields as additional candidates.
Steganalysis is treated as the counterpart process, beginning with the identification of suspect media, followed by statistical or visual analysis to confirm hidden content. Visual detection includes side‑by‑side comparison of cover and stego images, analysis of file‑size changes, color‑palette variations, and cropping artifacts. Network steganalysis focuses on detecting anomalous patterns in header fields, especially when IDS rely on whitelist signatures. The authors categorize attacks based on the information available: known‑carrier, steganography‑only, known‑message, and known‑steganography attacks.
In the conclusion, the paper acknowledges that each technique has inherent limitations: multimedia carriers are vulnerable to compression, format conversion, and noise, whereas IP‑datagram methods are susceptible to header normalization and MTU constraints. The authors stress that steganalysis must evolve alongside steganographic advances, and that ongoing research is needed to develop more robust embedding schemes and more effective detection tools.
Comments & Academic Discussion
Loading comments...
Leave a Comment