Preliminary Analysis of Google+s Privacy
In this paper we provide a preliminary analysis of Google+ privacy. We identified that Google+ shares photo metadata with users who can access the photograph and discuss its potential impact on privacy. We also identified that Google+ encourages the provision of other names including maiden name, which may help criminals performing identity theft. We show that Facebook lists are a superset of Google+ circles, both functionally and logically, even though Google+ provides a better user interface. Finally we compare the use of encryption and depth of privacy control in Google+ versus in Facebook.
💡 Research Summary
The paper presents a preliminary investigation of privacy issues in Google+, focusing on four main problem areas: photo metadata leakage, the solicitation of additional personal identifiers (such as maiden names), the structural limitations of Google+ circles compared with Facebook lists, and differences in encryption and fine‑grained content‑control features.
First, the authors observe that when a user uploads a picture to Google+, the platform automatically exposes EXIF metadata—including capture date and time, camera make and model, and sometimes GPS coordinates—to anyone with whom the photo is shared. While this information may appear innocuous, the paper argues that it can be weaponized for legal evidence, stalking, or physical threats (e.g., revealing ownership of an expensive camera). The authors illustrate the point with a public example: metadata from Larry Page’s vacation photos shows the use of a Canon EOS 5D Mark II, a $2,000 camera, thereby potentially incentivizing theft.
Second, the “About” section of Google+ encourages users to provide “other names,” explicitly citing examples such as maiden names or alternative spellings. Because many online services use a mother’s maiden name as a password‑recovery secret, disclosing this data creates a vector for identity‑theft attacks. The paper cites statistics indicating that identity theft costs the U.S. economy $15.6 billion annually, underscoring the seriousness of this design choice.
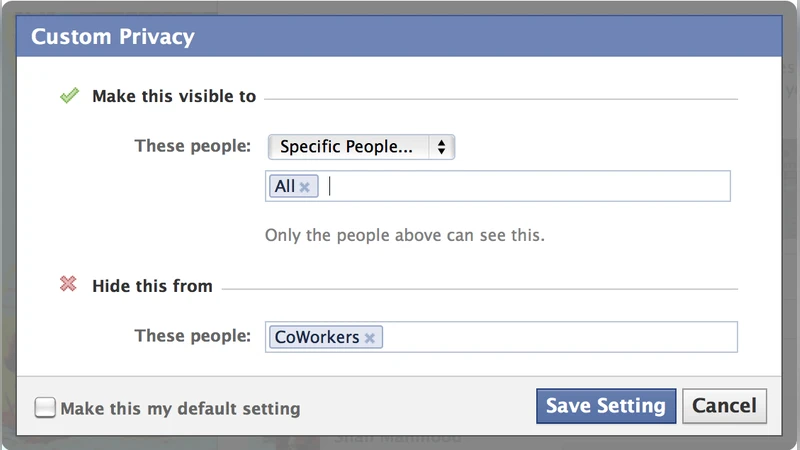
Third, the paper compares Google+ circles with Facebook lists. Google+ offers a visual drag‑and‑drop interface with four default circles (friends, family, acquaintances, following) and allows users to place contacts in multiple circles. However, the platform lacks an exception mechanism: if a post is shared with a larger circle, there is no way to exclude a subset of that circle, and the “public” option automatically includes all circles. Facebook, by contrast, treats all connections as “friends” but lets users create arbitrary lists and define exceptions (e.g., share with “All” while hiding from “Co‑Workers”). The authors argue that Facebook lists are a logical superset of Google+ circles, a claim reinforced by the existence of third‑party tools like “Circle Hack” that graft Google+‑style UI onto Facebook’s list system.
Fourth, the authors examine security controls. Google+ encrypts the entire session with TLS, whereas Facebook encrypts only the authentication phase, making Google+ more resistant to man‑in‑the‑middle attacks. Google+ also provides per‑post comment disabling, the ability to prevent resharing on a per‑item basis, and editable comments with visible timestamps. Facebook offers only coarse‑grained blocking (entire wall) and does not permit comment editing. While these features give Google+ users finer control, they also increase configuration complexity, potentially leading to user error.
Related work is surveyed, noting earlier reports of a Google+ privacy flaw that allowed unrestricted resharing of content, as well as various Facebook vulnerabilities (session hijacking, photo access hacks). The conclusion reiterates that despite Google+’s more polished UI and some stronger security mechanisms, it still exposes users to privacy risks through automatic metadata sharing and the collection of sensitive personal identifiers. The authors recommend that future social‑network designs adopt data‑minimization principles, provide opt‑out mechanisms for metadata exposure, and educate users about the implications of sharing auxiliary personal information.
Comments & Academic Discussion
Loading comments...
Leave a Comment