Model-Based Trace-Checking
Trace analysis can be a useful way to discover problems in a program under test. Rather than writing a special purpose trace analysis tool, this paper proposes that traces can usefully be analysed by checking them against a formal model using a standard model-checker or else an animator for executable specifications. These techniques are illustrated using a Travel Agent case study implemented in J2EE. We added trace beans to this code that write trace information to a database. The traces are then extracted and converted into a form suitable for analysis by Spin, a popular model-checker, and Pro-B, a model-checker and animator for the B notation. This illustrates the technique, and also the fact that such a system can have a variety of models, in different notations, that capture different features. These experiments have demonstrated that model-based trace-checking is feasible. Future work is focussed on scaling up the approach to larger systems by increasing the level of automation.
💡 Research Summary
The paper introduces a novel approach to trace analysis that leverages formal models and existing model‑checking tools instead of building dedicated trace‑analysis utilities. The authors instrument a J2EE‑based travel‑agent web application with two JavaBeans: a trace bean that captures relevant execution context (session ID, user ID, component URI, business operation name, etc.) and a trace‑SQL bean that persists these records into a central SQL database via JDBC. By storing all traces in a relational database, they can easily filter, aggregate, and transform the data for downstream processing, even when the application is distributed across multiple servers.
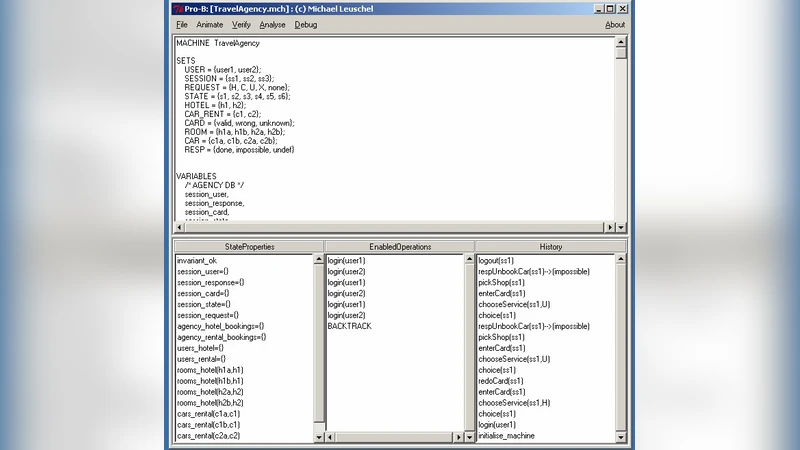
Two distinct formal models are constructed to validate the collected traces. The first is a B‑method abstract machine that defines system state (sessions, hotel and car bookings, assigned resources) and six invariants expressing core business rules, such as “a user with a booking must have an assigned hotel” and “no reservation proceeds without credit‑card approval.” Using the ProB animator, each trace entry is mapped to a B operation; the tool then checks whether the sequence of operations respects the invariants. Because ProB requires a finite‑state representation, the authors compress unbounded values (e.g., random session identifiers) into a small enumerated set and remove duplicate operation names with SQL DISTINCT.
The second model is written in Promela for the Spin model checker. Here the focus is on control flow and concurrency. Traces are converted into Promela execution sequences, and Linear Temporal Logic (LTL) properties such as “if a car is requested and available, it will eventually be booked” and “no request proceeds without credit‑card approval” are verified. Spin’s exhaustive state‑space exploration uncovers ordering violations and race‑condition‑like errors that are difficult to detect with manual log inspection.
Experimental evaluation shows that both model‑checking approaches successfully identified real defects in the travel‑agent system. ProB detected logical inconsistencies (e.g., missing credit‑card checks), while Spin revealed synchronization problems in distributed booking scenarios. The case study demonstrates that model‑based trace checking can be added to existing development processes with relatively low overhead: trace code can be inserted manually or, in future work, automatically via AspectJ; the models are written in familiar notations; and standard tools (Spin, ProB) perform the heavy lifting.
The authors acknowledge current limitations: trace insertion is still manual, and the mapping between implementation events and model operations relies on expert judgment. They propose future work on automated trace instrumentation, generation of model‑trace mappings, and scalability improvements for larger systems (e.g., efficient preprocessing, real‑time trace collection). Overall, the paper argues that using executable formal models as oracles for trace validation offers a cost‑effective, automated, and rigorous alternative to traditional testing and logging practices, potentially widening the adoption of formal methods in mainstream software engineering.
Comments & Academic Discussion
Loading comments...
Leave a Comment