Darwin inside the machines: Malware evolution and the consequences for computer security
Recent advances in anti-malware technologies have steered the security industry away from maintaining vast signature databases and into newer defence technologies such as behaviour blocking, application whitelisting and others. Most would agree that the reasoning behind this is to keep up with the arms race established between malware writers and the security community almost three decades ago. Still, malware writers have not as yet created new paradigms. Indeed, malicious code development is still largely limited to code pattern changes utilizing polymorphic and metamorphic engines, as well as executable packer and wrapper technologies. Each new malware instance retains the exact same core functionality as its ancestor and only alters the way it looks. What if, instead, malware were able to change its function or behaviour autonomously? What if, in the absence of human intervention, computer viruses resembled biological viruses in their ability to adapt to new defence technologies as soon as they came into effect? In this paper, we will provide the theoretical proof behind malware implementation that closely models Darwinian evolution.
💡 Research Summary
The paper “Darwin inside the machines: Malware evolution and the consequences for computer security” presents a theoretical framework for autonomous, function‑changing malware that follows the principles of Darwinian evolution. The authors begin by noting that modern anti‑malware solutions have shifted from massive signature databases toward behavior‑blocking, application whitelisting, and other heuristic approaches, yet contemporary malware still relies almost exclusively on polymorphic and metamorphic techniques that only alter appearance while preserving core functionality.
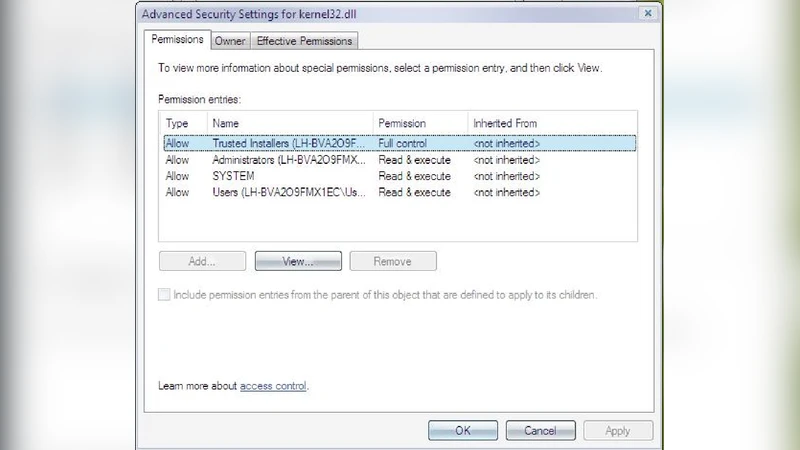
To explore a different paradigm, the authors map the three essential components of biological evolution—replication, variation, and differential fitness—onto computer viruses. Replication is the self‑reproducing capability of malware; variation is introduced through an “Evolutionary Function” (EF) that can, with a certain probability, generate new functional code (N) by harvesting existing API calls, script fragments, or other code present in the host environment. This approach sidesteps the brittleness of raw binary mutation (e.g., on the x86 instruction set) by leveraging already functional code, thereby increasing the likelihood that mutations remain viable. Differential fitness is measured by the malware’s ability to evade detection mechanisms such as signature scanners, behavior‑based blockers, or whitelisting systems; successful variants propagate, while ineffective ones die out.
The paper reviews prior work in artificial life (Avida, Ray’s self‑replicators) that demonstrated Darwinian evolution in controlled digital environments, emphasizing that those systems use highly evolvable instruction sets, unlike typical software languages. It argues that a similar evolvable “meta‑language” is unnecessary if the malware can co‑opt native APIs, thereby reducing the engineering burden. The EF itself can be concealed using existing polymorphic/metamorphic engines, making static detection difficult. Moreover, by mimicking benign application behavior (e.g., presenting a UI, importing innocuous APIs), the malware can exploit the industry’s bias against false positives, effectively “whitelisting” itself.
Three concrete threat scenarios illustrate how functional evolution could undermine current defenses:
-
Clean‑application mimicry – By adopting API calls common to trusted software, the malware gains a negative weight in behavior‑based scoring systems, allowing it to slip past heuristics. This mirrors biological viruses that express host‑like proteins to evade immune detection.
-
Whitelisting deception – An evolving malware could dynamically convert between executable, script, or macro forms, thereby evading whitelist filters that focus on a single file type. It could also generate large numbers of benign‑looking files whose hashes match the malicious payload, subverting reputation‑based whitelisting similar to how some bacteriophages mimic bacterial DNA methylation patterns.
-
Virtual‑machine anti‑emulation – By generating long, random API loops or parameter‑checking functions, the malware can exhaust the instruction‑limit of sandbox emulators, causing them to abort analysis. This technique, already used in polymorphic threats, becomes intrinsic to a self‑evolving malware that can continually devise new anti‑emulation tricks.
The authors emphasize that, unlike current malware whose functional repertoire is static, an autonomously evolving threat could continuously discover new exploits, adapt to emerging defenses, and blend with legitimate software, rendering signature‑based, behavior‑based, and whitelist defenses largely ineffective. They argue that the short generation times of digital viruses (orders of magnitude faster than bacterial generations) combined with high mutation rates could produce significant functional complexity within weeks, analogous to rapid adaptive changes observed in biological experiments (e.g., E. coli evolving citrate utilization).
In conclusion, the paper asserts that while no real‑world self‑evolving malware has yet been demonstrated, the theoretical construct is plausible and warrants serious consideration. It calls for the security community to anticipate such evolutionary threats, to develop detection strategies that do not rely solely on static signatures or predictable behavior patterns, and to explore defensive mechanisms that can cope with a moving target capable of autonomous functional innovation.
Comments & Academic Discussion
Loading comments...
Leave a Comment