Information Security Plan for Flight Simulator Applications
The Department of Defense has a need for an identity management system that uses two factor authentications to ensure that only the correct individuals get access to their top secret flight simulator program. Currently the Department of Defense does not have a web interface sign in system. We will be creating a system that will allow them to access their programs, back office and administrator functions remotely. A security plan outlining our security architecture will be delivered prior to the final code roll out. The plan will include responses to encryption used and the security architecture applied in the final documentation. The code will be delivered in phases to work out any issues that may occur during the implementation
💡 Research Summary
The paper presents a comprehensive information‑security plan for the Department of Defense’s (DoD) “Prometheus Flight Simulator,” a high‑value, top‑secret application that will be accessed remotely by warfighters, contractors, and internal staff. The authors, representing Capella University and the University of Hawaii‑Hilo, outline a mixed COTS‑and‑custom solution to provide a web‑facing sign‑in system that satisfies stringent DoD requirements, including FISMA compliance and NIST SP 800‑53 Level 4 security.
The core of the design is a dual‑factor authentication framework that combines hardware tokens (time‑based OTP) with Common Access Card (CAC) based Public Key Infrastructure (PKI) authentication. The PKI workflow involves the client presenting an X.509 certificate stored on the CAC, server‑side validation via OCSP/CRL, and enforcement of certificate revocation checks before granting access. This approach ensures strong non‑repudiation, confidentiality, and integrity for all sessions.
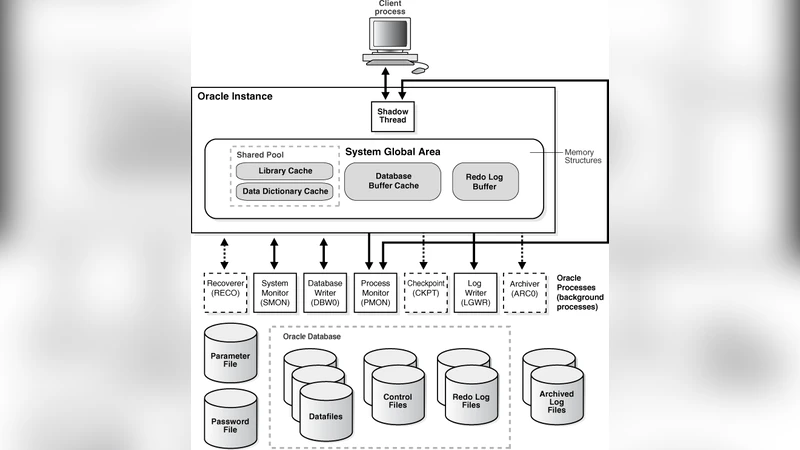
Architecturally, the solution follows DoD’s existing decentralized security model. A DMZ hosts the token and PKI servers, while internal networks contain the flight‑simulator application server, back‑office server, administrator server, and an Oracle database. All communications are protected with TLS 1.2+ and data at rest is encrypted with AES‑256. The database layer uses parameterized queries, transaction blocks, and server‑side input validation to prevent SQL injection and other injection attacks.
Compliance is addressed through a series of concrete controls: least‑privilege access, FIPS 140‑2 validated cryptographic modules, strong password policies, multi‑factor login, and rigorous audit logging forwarded to a centralized SIEM. System hardening includes disabling auto‑run, locking unused ports, enforcing USB usage policies, and conducting regular vulnerability scans per NIST SP 800‑61 guidelines. Incident response follows DoD standards, with evidence collection, reporting, and escalation procedures defined.
The development lifecycle adopts an Agile methodology with continuous security integration. Each sprint incorporates static code analysis (using CodePro Analytix), dynamic testing, and peer reviews to enforce secure coding standards. Change management is tracked via Git with an approval workflow, ensuring traceability of all modifications. The plan also outlines a phased rollout: Phase 1 supports 100 initial users, Phase 2 adds an onboarding system, and Phase 3 scales to 100,000 users, requiring horizontal scaling of the authentication infrastructure and directory services.
Overall, the paper delivers a detailed, standards‑based security blueprint that aligns with DoD policy, mitigates a wide range of cipher and network attacks, and provides a scalable path for future expansion. The authors’ emphasis on integrating physical and information security policies, coupled with concrete mitigation strategies for malicious ciphers, system hardening, and database protection, makes this plan a practical reference for high‑assurance government applications.
Comments & Academic Discussion
Loading comments...
Leave a Comment