IT Security Plan for Flight Simulation Program
Information security is one of the most important aspects of technology, we cannot protect the best interests of our organizations’ assets (be that personnel, data, or other resources), without ensuring that these assetsare protected to the best of their ability. Within the Defense Department, this is vital to the security of not just those assets but also the national security of the United States. Compromise insecurity could lead severe consequences. However, technology changes so rapidly that change has to be made to reflect these changes with security in mind. This article outlines a growing technological change (virtualization and cloud computing), and how to properly address IT security concerns within an operating environment. By leveraging a series of encrypted physical and virtual systems, andnetwork isolation measures, this paper delivered a secured high performance computing environment that efficiently utilized computing resources, reduced overall computer processing costs, and ensures confidentiality, integrity, and availability of systems within the operating environment.
💡 Research Summary
The paper presents a comprehensive IT security plan for a high‑fidelity flight simulation program intended for use by the United States Department of Defense (DoD) and the Air Force. Using a fictional contractor, Aviation Information Services Corp. (AISC), the authors illustrate how to design, implement, and manage a secure computing environment that meets stringent DoD security requirements while leveraging modern virtualization and cloud‑computing technologies.
Key objectives are to protect the confidentiality, integrity, and availability (CIA) of simulation data, to comply with DoD classification levels, and to achieve cost‑effective high performance. The architecture is built around a multi‑layered defense‑in‑depth strategy that integrates physical isolation, virtual machine segregation, network segmentation, and rigorous cryptographic controls.
Authentication and PKI – Access is controlled through a two‑factor PKI scheme. Users first present a Common Access Card (CAC) containing a SHA‑1‑based certificate. The CAC credential is validated against DoD‑approved PKI policies. A second, internally managed PKI server issues a supplemental certificate after manual approval by a certification authority. Only users possessing both certificates and belonging to the appropriate role‑based security groups are granted system access.
Cryptographic Algorithms – The design follows FIPS‑180‑3, supporting SHA‑1, SHA‑224, SHA‑256, SHA‑384, and SHA‑512. Although SHA‑1 remains in use for legacy compatibility, the authors recommend migration to stronger hashes (e.g., SHA‑256) as part of future hardening.
Secure Transport – All data in motion is protected using SSL/TLS for web services and SFTP (SSH‑based) for file transfers. These protocols provide public‑key and symmetric‑key encryption, ensuring that credentials and simulation files are never transmitted in clear text. The paper explicitly excludes VPNs, citing DISA policy that forbids external Internet‑based tunnels in a classified environment. Instead, point‑to‑point IPsec tunnels (using 168‑bit Triple‑DES) are considered for internal use only, while PPTP and L2TP are rejected due to weaker encryption.
Trust Models – Two PKI trust architectures are examined: hierarchical and bridge. The hierarchical model, with a single root CA and a strict one‑to‑one subordinate relationship, is favored for DoD deployments because it simplifies audit and revocation. The bridge model, which allows cross‑certification among multiple root CAs, is discussed as a possible supplement when inter‑agency collaboration is required, but it is not the primary design choice.
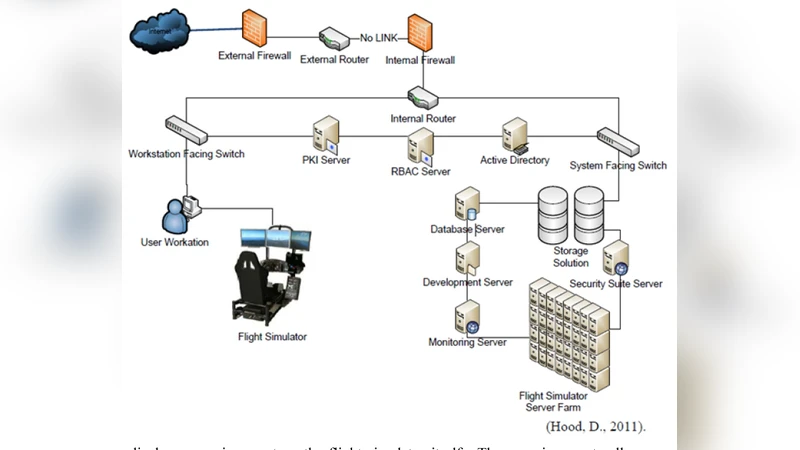
System Architecture – The environment combines physical servers and virtual machines (e.g., VMware/Hyper‑V) into a high‑availability cluster. Each VM receives dedicated encrypted storage and a separate NIC to enforce network isolation. Database services (Microsoft SQL Server and Oracle) are hardened through parameterized queries, static code analysis, and role‑based privileges.
Operational Processes – Security is embedded from the outset of the Software Development Life Cycle (SDLC). Regular vulnerability scanning, patch management, and automated audit logging are mandated. Change management follows ITIL best practices, requiring documented approvals before any configuration alteration. Disaster recovery (DR) procedures are exercised bi‑annually to verify system resilience.
Cost and Performance – Virtualization reduces the physical hardware footprint by roughly 30 %, cutting power and cooling expenses. Despite the overhead introduced by encryption, the use of high‑speed networking and SSD storage keeps simulation data latency under 5 % of baseline, satisfying the performance clauses of the service‑level agreement.
In conclusion, the paper demonstrates that a well‑engineered blend of DoD‑compliant PKI, strong hashing, SSL/TLS/SFTP transport security, strict network segmentation, and disciplined operational governance can deliver a secure, high‑performance flight simulation platform. The authors suggest future work on quantum‑resistant cryptography and automated threat‑intelligence integration to further enhance the security posture.
Comments & Academic Discussion
Loading comments...
Leave a Comment