IT Security Issues Within the Video Game Industry
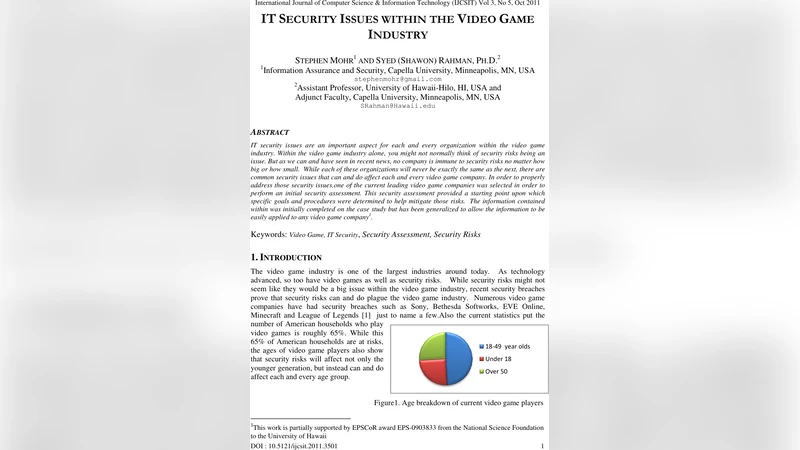
IT security issues are an important aspect for each and every organization within the video game industry. Within the video game industry alone, you might not normally think of security risks being an issue. But as we can and have seen in recent news, no company is immune to security risks no matter how big or how small. While each of these organizations will never be exactly the same as the next, there are common security issues that can and do affect each and every video game company. In order to properly address those security issues, one of the current leading video game companies was selected in order to perform an initial security assessment. This security assessment provided a starting point upon which specific goals and procedures were determined to help mitigate those risks. The information contained within was initially completed on the case study but has been generalized to allow the information to be easily applied to any video game company.
💡 Research Summary
The paper “IT Security Issues Within the Video Game Industry” examines the growing importance of information‑technology security for companies that develop, publish, and distribute video games. Although the industry is often associated with creative content rather than cyber‑risk, recent high‑profile breaches at Sony, Bethesda, and other studios demonstrate that game companies are attractive targets for attackers. The authors select ZeniMax Media Inc., a multinational publisher with subsidiaries such as Bethesda Softworks, id Software, and others, as a representative case study.
The study begins with a preliminary security assessment that covers three layers: enterprise‑wide weaknesses, network‑level vulnerabilities, and software/hardware‑specific risks. The most significant enterprise weakness identified is the frequent acquisition and integration of new studios. Each merger introduces foreign domains, authentication systems, and network segments that must be merged with existing Active Directory, Exchange, and Windows Server environments. Without careful segregation, these integrations can create over‑privileged accounts, trust‑relationship flaws, and hidden back‑doors.
Patch management is another critical issue. ZeniMax’s reliance on Microsoft server products means that unpatched vulnerabilities such as EternalBlue, PrintNightmare, or other CVEs could be exploited. However, indiscriminate patching can disrupt game servers and development pipelines, so the authors recommend a staged rollout after testing in a sandbox environment.
Common office and multimedia applications—Adobe Reader, Flash, QuickTime, Microsoft Office—are highlighted as typical infection vectors. Malicious macros in Office documents and phishing attachments in Outlook can compromise user workstations and, via Exchange, the broader corporate mail system. The paper advises strict mail‑gateway filtering, disabling of unsafe file types, and the deployment of Data‑Loss‑Prevention (DLP) tools.
On the software development side, the authors cite ISO/IEC TR 24772, which notes that every programming language contains constructs that can lead to undefined behavior, implementation‑dependent results, or outright vulnerabilities. Game engines written in C/C++, C#, or scripting languages are therefore prone to buffer overflows, memory corruption, and injection attacks if secure coding practices are not enforced. The authors recommend static and dynamic code analysis, secure‑coding guidelines, and regular peer reviews.
Network analysis reveals that ZeniMax operates a mixture of LANs, VLANs, and WAN links connecting offices in the United States, Europe, and Asia. While dedicated leased lines or MPLS circuits would provide the highest confidentiality and integrity, cost considerations often push companies to use the public Internet with IPsec‑based VPNs. The paper stresses that VPNs must be configured with strong encryption (AES‑256), mutual authentication (certificates or hardware tokens), and robust key‑management. Additional controls such as next‑generation firewalls, intrusion‑detection/prevention systems (IDS/IPS), and centralized log aggregation are deemed essential, especially after the Sony PlayStation Network breach of 2011.
Physical security and human factors are addressed in the final section. The authors propose access‑control badges, CCTV monitoring of data‑center entrances, and the use of hardware security modules (HSMs) for key storage. They also outline a comprehensive security program that includes:
- Formal information‑security policies covering data classification, retention, and disposal.
- Ongoing security awareness training for all staff, with phishing simulations for non‑technical employees and secure‑coding workshops for developers.
- An Incident Response Plan (IRP) that defines detection, containment, eradication, and recovery steps, along with a communication protocol for notifying customers and regulators.
- A roadmap for implementing technical controls, accounting for budget constraints, staffing shortages, and cultural resistance.
In conclusion, the paper argues that the video‑game sector’s rapid growth and its reliance on high‑value intellectual property make it a prime target for cyber‑attacks. Regardless of company size, a systematic risk‑assessment process, layered technical defenses, and a strong security culture are necessary to protect both the business and its player community. The findings and recommendations derived from the ZeniMax case study are presented as a template that other game developers and publishers can adapt to their own environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment