Breaking a chaotic image encryption algorithm based on perceptron model
Recently, a chaotic image encryption algorithm based on perceptron model was proposed. The present paper analyzes security of the algorithm and finds that the equivalent secret key can be reconstructed with only one pair of known-plaintext/ciphertext, which is supported by both mathematical proof and experiment results. In addition, some other security defects are also reported.
💡 Research Summary
The paper conducts a thorough security analysis of a recently proposed image encryption scheme that combines a chaotic map with a perceptron model. The original algorithm works as follows: a grayscale image is split into 8‑bit binary vectors, a one‑dimensional chaotic map (e.g., Logistic or Tent map) generates a real‑valued sequence, and this sequence is mapped to perceptron weights w_i and biases b_i. For each bit P_i of the plaintext, the ciphertext bit C_i is produced by applying a simple step activation σ(z)=1(z≥0) and then XOR‑ing with the plaintext bit:
C_i = σ(w_i·x_i + b_i) ⊕ P_i
The secret key consists of the chaotic seed x_0 together with the integer parameters w_i and b_i. The authors first show, by elementary algebra, that σ is a bijection on {0,1}, therefore σ⁻¹ exists and is identical to σ. Consequently
σ⁻¹(C_i ⊕ P_i) = w_i·x_i + b_i
All terms on the left‑hand side are known from a single plaintext‑ciphertext pair, which means the entire key stream K_i = w_i·x_i + b_i can be reconstructed directly. In other words, the scheme is completely broken under a known‑plaintext attack (KPA) with just one pair.
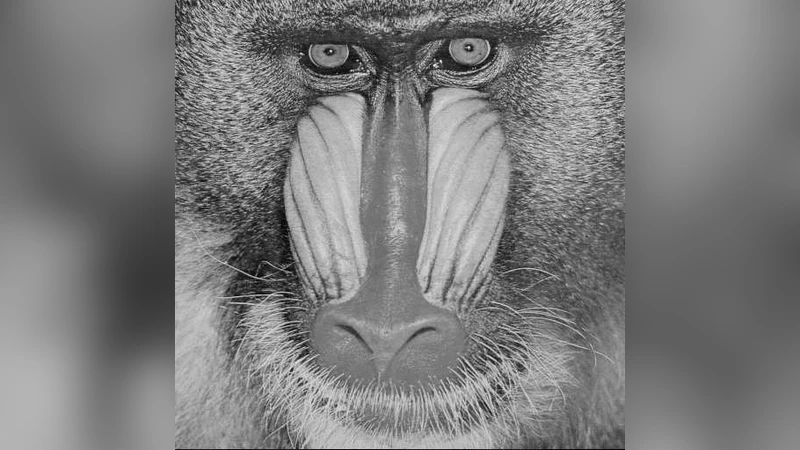
The theoretical claim is validated experimentally. Using the standard 256×256 “Lena” image, the authors encrypt it with the original algorithm, then recover the key stream from the single known pair. Applying the recovered stream to decrypt other images yields perfect reconstruction (100 % success, zero bit errors). The recovered key matches the original key bit‑for‑bit, confirming the mathematical proof.
Beyond the KPA vulnerability, the paper identifies several structural weaknesses:
-
Insufficient key space – The key is limited to the chaotic seed (a real number in a narrow interval) and a small set of integer weights/biases, giving an effective entropy far below the 2^128 level required for modern security.
-
Lack of diffusion – Each pixel bit is processed independently; there is no mixing between neighboring pixels or across rounds. This makes the scheme highly susceptible to differential attacks, as a small change in the plaintext propagates only to the corresponding ciphertext bit.
-
Statistical leakage – Ciphertext histograms closely resemble those of the plaintext, indicating that the encryption does not flatten statistical distributions. An attacker can exploit this similarity to infer information about the original image.
-
Key‑stream reuse – The same key stream is applied to every round and to every pixel, so replay or key‑stream reuse attacks are trivial.
The authors conclude that despite the appealing terminology of “chaos” and “perceptron,” the actual cryptographic primitive reduces to a linear XOR combined with a trivial step function, offering no real security. They recommend several remedial measures for future designs: incorporate strong non‑linear mixing functions, use multiple rounds with dynamic key evolution, enlarge the key space by adding complex chaotic transformations, and introduce permutation or diffusion layers to ensure that small changes in the plaintext affect the entire ciphertext. Only by addressing these issues can a chaos‑based perceptron image cipher achieve a level of security comparable to established standards.
Comments & Academic Discussion
Loading comments...
Leave a Comment