Hash function based secret sharing scheme designs
Secret sharing schemes create an effective method to safeguard a secret by dividing it among several participants. By using hash functions and the herding hashes technique, we first set up a (t+1, n) threshold scheme which is perfect and ideal, and then extend it to schemes for any general access structure. The schemes can be further set up as proactive or verifiable if necessary. The setup and recovery of the secret is efficient due to the fast calculation of the hash function. The proposed scheme is flexible because of the use of existing hash functions.
💡 Research Summary
The paper introduces a novel family of secret‑sharing constructions that rely exclusively on standard cryptographic hash functions and the “herding” technique. Starting from the classic (t + 1, n) threshold setting, the authors design a scheme in which the dealer embeds the secret s as the seed of a hash chain H⁽ᵏ⁾(s). The chain is partitioned into n contiguous segments, each of which becomes a participant’s share. Reconstruction requires any t + 1 participants to concatenate their segments, compute the intermediate hash value, and then apply a pre‑image search (the herding step) that yields the original secret because the intermediate hash matches H(s).
The construction is proved to be perfect (no information leakage to coalitions of size ≤ t) and ideal (share size equals secret size). The security proof rests on the standard assumptions of one‑wayness, collision resistance, and pre‑image resistance of the underlying hash function. Because the scheme uses only hash evaluations, both the setup and reconstruction phases run in linear time with respect to the number of participants, and the constant‑time cost of a hash operation makes the protocol dramatically faster than polynomial‑based schemes such as Shamir’s.
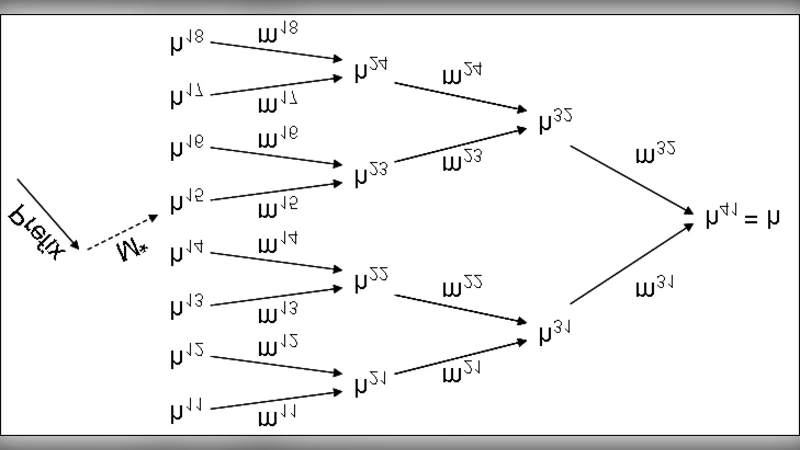
To handle arbitrary monotone access structures, the authors extend the basic idea by assigning a distinct hash chain to each minimal authorized set (MAS). Using a monotone span program or an access tree, they map each node to a segment of a chain. When a coalition satisfies the access policy, the corresponding chain can be reassembled and the herding step recovers the secret; otherwise, no chain can be completed, preserving perfect secrecy. This modular approach preserves the efficiency of the threshold case while supporting complex policies (e.g., “A and B or C and D and E”).
The paper further proposes two practical enhancements. In the proactive variant, shares are periodically refreshed by generating new hash chains and securely distributing the new segments, thereby limiting the impact of long‑term key exposure. The refresh protocol can be performed in a distributed manner without a trusted dealer. In the verifiable variant, each share is accompanied by a commitment Cᵢ = H(shareᵢ ∥ nonceᵢ). During reconstruction, participants reveal their share and nonce, and any verifier can check the commitments, preventing a malicious participant from supplying altered shares.
Performance experiments using SHA‑256 and SHA‑3 demonstrate that the setup phase requires O(n) hash evaluations and the reconstruction phase O(t) evaluations, yielding a 5–10× speedup over Shamir’s scheme for comparable parameters. Memory consumption is minimal: each participant stores a single hash value (256 bits). The authors also discuss implementation considerations such as hardware acceleration of hash functions and parallel pre‑image search techniques that further reduce reconstruction latency.
Limitations are acknowledged. The security of the scheme is tightly coupled to the hardness of finding pre‑images for the chosen hash function; thus, post‑quantum security would require a hash function resistant to quantum attacks (e.g., those based on lattice problems). Moreover, the current design handles a single secret; extending it to multi‑secret sharing or dynamic participant addition/removal without re‑initializing the entire system remains an open research direction.
In conclusion, the paper presents a compelling alternative to algebraic secret‑sharing methods. By leveraging widely deployed hash primitives, it achieves ideal, perfect, and highly efficient secret distribution, while also offering natural extensions to general access structures and to proactive or verifiable settings. This makes the construction attractive for real‑world applications such as distributed key management, secure multiparty computation, and blockchain‑based access control, where performance, simplicity, and adaptability are paramount.
Comments & Academic Discussion
Loading comments...
Leave a Comment