A Mechanism for Detection of Cooperative Black Hole Attack in Mobile Ad Hoc Networks
A mobile ad hoc network (MANET) is a collection of autonomous nodes that communicate with each other by forming a multi-hop radio network and maintaining connections in a decentralized manner. Security remains a major challenge for these networks due to their features of open medium, dynamically changing topologies, reliance on cooperative algorithms,absence of centralized monitoring points, and lack of clear lines of defense. Most of the routing protocols for MANETs are thus vulnerable to various types of attacks. Ad hoc on-demand distance vector routing (AODV) is a very popular routing algorithm. However, it is vulnerable to the well-known black hole attack, where a malicious node falsely advertises good paths to a destination node during the route discovery process. This attack becomes more sever when a group of malicious nodes cooperate each other. In this paper, a defense mechanism is presented against a coordinated attack by multiple black hole nodes in a MANET. The simulation carried out on the proposed scheme has produced results that demonstrate the effectiveness of the mechanism in detection of the attack while maintaining a reasonable level of throughput in the network.
💡 Research Summary
The paper addresses a critical security vulnerability in mobile ad‑hoc networks (MANETs) that use the widely adopted Ad‑hoc On‑Demand Distance Vector (AODV) routing protocol. While AODV is efficient for dynamic topologies, it is susceptible to black‑hole attacks, where a malicious node advertises a false route to a destination and then drops all intercepted packets. Existing defenses focus on detecting a single black‑hole node; however, a coordinated group of malicious nodes can collude to bypass those mechanisms, creating a “cooperative black‑hole” threat that is far more damaging.
To counter this, the authors propose a two‑layer defense mechanism that minimally modifies AODV. The first layer introduces a Data Routing Information (DRI) table maintained locally at each node. The DRI table stores two binary flags for every neighbor: the “From” flag indicates whether the node has ever received data packets from that neighbor, and the “Through” flag indicates whether it has ever forwarded data packets through that neighbor. For example, a “1 1” entry for neighbor X means the node has both received from and routed through X; a “0 0” entry means no interaction has occurred. These bits provide a lightweight historical trust metric that can be attached to routing control messages.
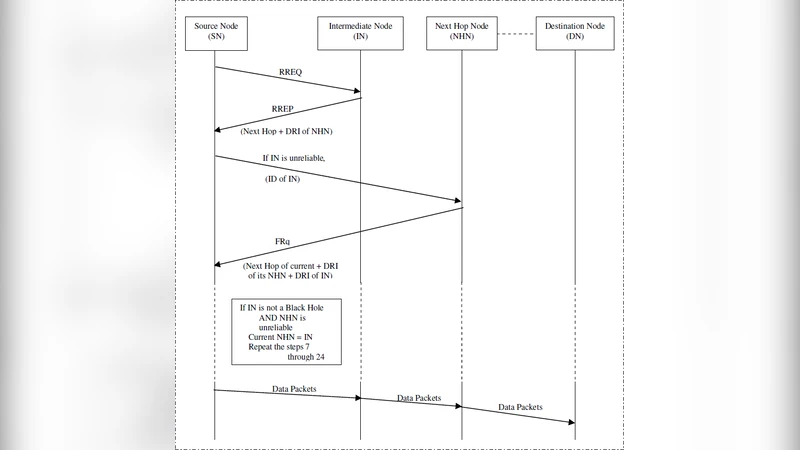
The second layer is a cross‑checking procedure that activates when a source node (SN) receives a Route Reply (RREP) from an intermediate node (IN) that is not already trusted according to SN’s DRI table. In that case, SN sends a Further Request (FRq) to the next‑hop node (NHN) advertised by IN. NHN replies with a Further Reply (FRp) containing: (i) its DRI entry for IN (i.e., whether IN has routed through NHN), (ii) the identity of NHN’s own next hop toward the destination, and (iii) the DRI entry for that subsequent hop. By comparing the DRI bits reported by NHN with the information advertised by IN, SN can verify whether IN’s claim of a valid route is consistent with actual traffic history. If inconsistencies are found, the route is flagged as malicious, the involved nodes are added to a faulty list, and data transmission is aborted.
The authors formalize the modified AODV operation in algorithmic pseudocode and illustrate the process with detailed diagrams. They then evaluate the scheme using NS‑2 simulations. The testbed consists of 50 mobile nodes, with 30 % of them acting as cooperative black‑hole attackers. Mobility speeds range from 0 to 20 m/s, and traffic is generated using Constant Bit Rate (CBR) sources. Performance metrics include packet delivery ratio, detection rate, control‑packet overhead, and throughput degradation.
Results show that the proposed mechanism achieves a detection rate exceeding 95 % even under coordinated attacks, while maintaining a throughput loss of less than 10 % compared to a benign network. Control overhead rises modestly due to the additional FRq/FRp exchanges, but the authors argue that the trade‑off is acceptable given the substantial security gain. They also discuss limitations: the DRI table requires an initial learning period before reliable trust values can be established, and the cross‑checking step introduces extra latency and message traffic. Future work is suggested in the areas of dynamic DRI updating, multi‑path cross‑checking to reduce latency, and integration with cryptographic authentication to further harden the protocol.
In summary, the paper contributes a practical, low‑complexity solution for detecting and mitigating cooperative black‑hole attacks in AODV‑based MANETs. By leveraging locally stored routing history (DRI) and a lightweight verification handshake (cross‑checking), the scheme enhances security without demanding heavyweight cryptographic infrastructure, making it suitable for resource‑constrained ad‑hoc environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment