A Distributed Protocol for Detection of Packet Dropping Attack in Mobile Ad Hoc Networks
In multi-hop mobile ad hoc networks (MANETs),mobile nodes cooperate with each other without using any infrastructure such as access points or base stations. Security remains a major challenge for these networks due to their features of open medium, dynamically changing topologies, reliance on cooperative algorithms, absence of centralized monitoring points, and lack of clear lines of defense. Among the various attacks to which MANETs are vulnerable, malicious packet dropping attack is very common where a malicious node can partially degrade or completely disrupt communication in the network by consistently dropping packets. In this paper, a mechanism for detection of packet dropping attack is presented based on cooperative participation of the nodes in a MANET. The redundancy of routing information in an ad hoc network is utilized to make the scheme robust so that it works effectively even in presence of transient network partitioning and Byzantine failure of nodes. The proposed scheme is fully cooperative and thus more secure as the vulnerabilities of any election algorithm used for choosing a subset of nodes for cooperation are absent. Simulation results show the effectiveness of the protocol.
💡 Research Summary
**
The paper addresses the problem of malicious packet‑dropping attacks in multi‑hop mobile ad‑hoc networks (MANETs), where compromised nodes can severely degrade or completely disrupt communication by selectively or wholly discarding packets. Existing defenses—such as watchdog/pathrater schemes, reputation‑based systems like CONFIDANT, hardware‑based credit counters, and mobile‑agent based monitoring—suffer from limitations including reliance on overhearing (which fails under collisions or weak signals), high computational or communication overhead, dependence on specialized hardware, and vulnerability to single points of failure when only a subset of nodes participates in detection.
To overcome these drawbacks, the authors propose a fully cooperative, distributed detection protocol that leverages the inherent redundancy of routing information in MANETs. The core idea is to intertwine cryptographic key distribution with intrusion detection (IDS) so that each reinforces the other: initial trust relationships are established via location‑limited side channels, and the IDS continuously updates trust information that, in turn, guides secure key management.
Each node hosts five logical components:
-
Monitor – passively listens to neighbor traffic, randomly copies incoming packets, and verifies whether neighbors forward them unchanged, drop them, or modify them. When the observed deviation from normal behavior exceeds a preset threshold, the monitor triggers the trust‑collection process.
-
Trust Collector – implements a majority‑consensus algorithm among the neighbors of a suspected node. The accusing node sends a “challenge” to the suspect; the suspect acknowledges and broadcasts a “verify_behavior” request to all its neighbors. Each neighbor replies with its measured degree of maliciousness. The suspect aggregates these values, computes a group‑trust metric (based on the absolute difference between individual trust values and the average of the majority), and broadcasts the result together with the signed responses. All messages are protected by public‑key cryptography and time‑stamps to prevent replay attacks.
-
Trust Manager – maintains a global trust table that records suspected nodes and their current trust scores. Upon receiving a new group‑trust certificate, the manager verifies its integrity, checks that the aggregation was performed correctly, and updates the node’s trust using a weighted combination of the old trust, the new certificate, and a time‑based replenishment factor (δ). The weighting factors α₁, α₂, α₃ are derived from the majority’s trust values, the size of the network, and the number of certificates received within a threshold interval.
-
Trust Propagator – exploits node mobility to disseminate trust certificates throughout the network. Certificates are piggy‑backed on regular routing packets, eliminating extra bandwidth consumption. The propagation distance (number of hops) is dynamically adjusted based on neighbor information, ensuring rapid spread even during transient network partitions. Redundant copies enable nodes to compare certificates locally and detect tampering.
-
Whistle Blower – activates when a node’s trust falls below a critical threshold, raising a global alarm that triggers network‑wide isolation of the malicious node.
The protocol’s design choices—full participation of all nodes, cryptographically secured majority voting, and routing‑information‑driven certificate propagation—provide robustness against Byzantine failures, selective forwarding attacks, and temporary network splits. By avoiding reliance on a small elected subset, the scheme eliminates observation bias that can arise when only local neighbors monitor a suspect.
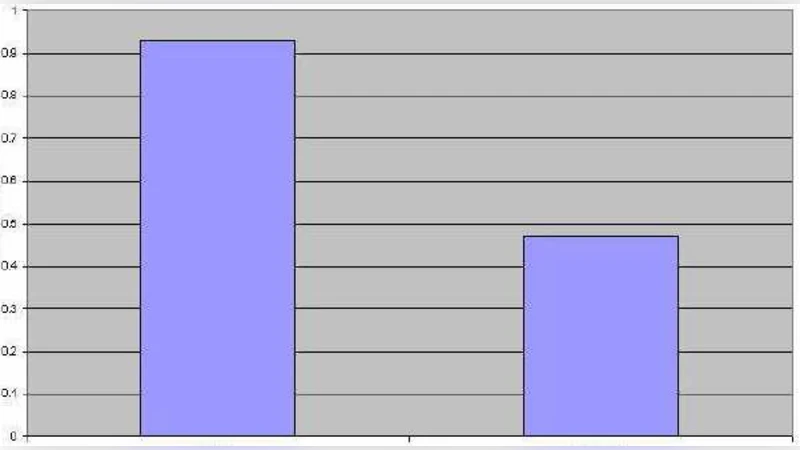
Simulation experiments were conducted in the NS‑2 simulator under varying conditions: different percentages of malicious nodes (10‑30 %), node speeds, and network partition scenarios. The proposed protocol was benchmarked against CONFIDANT and the classic watchdog/pathrater approach. Results show a detection rate exceeding 92 % and a false‑positive rate below 3 %, outperforming the compared schemes, especially in partitioned networks where trust information continues to propagate via mobility‑driven flooding. Computational overhead remains modest because most calculations are performed locally, and certificate exchange incurs negligible extra traffic due to piggy‑backing.
In summary, the paper presents a novel, fully cooperative distributed security framework for MANETs that tightly couples key management with intrusion detection. By leveraging the redundancy of routing data, employing majority‑based trust consensus, and ensuring cryptographic integrity, the protocol achieves high detection accuracy, low false alarms, and resilience to Byzantine behavior—all while maintaining low communication and storage overhead. This contribution represents a significant advancement over prior packet‑dropping detection mechanisms in ad‑hoc wireless environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment