A Distributed Intrusion Detection System Using Cooperating Agents
The current intrusion detection systems have a number of problems that limit their configurability, scalability and efficiency. There have been some propositions about distributed architectures based on multiple independent agents working collectively for intrusion detection. However, these distributed intrusion detection systems are not fully distributed as most of them centrally analyze data collected from distributed nodes which may lead to a single point of failure. In this paper, a distributed intrusion detection architecture is presented that is based on autonomous and cooperating agents without any centralized analysis components. The agents cooperate by using a hierarchical communication of interests and data, and the analysis of intrusion data is made by the agents at the lowest level of the hierarchy. This architecture provides significant advantages in scalability, flexibility, extensibility, fault tolerance, and resistance to compromise. A proof-of-concept prototype is developed and experiments have been conducted on it. The results show the effectiveness of the system in detecting intrusive activities.
💡 Research Summary
The paper addresses the inherent limitations of contemporary intrusion detection systems (IDS), namely poor configurability, limited scalability, and inefficiencies caused by centralized data analysis. While many recent proposals advocate distributed IDS architectures composed of multiple autonomous agents, they still rely on a central component that aggregates and analyzes data collected from distributed nodes, creating a single point of failure and potential information loss during data refinement.
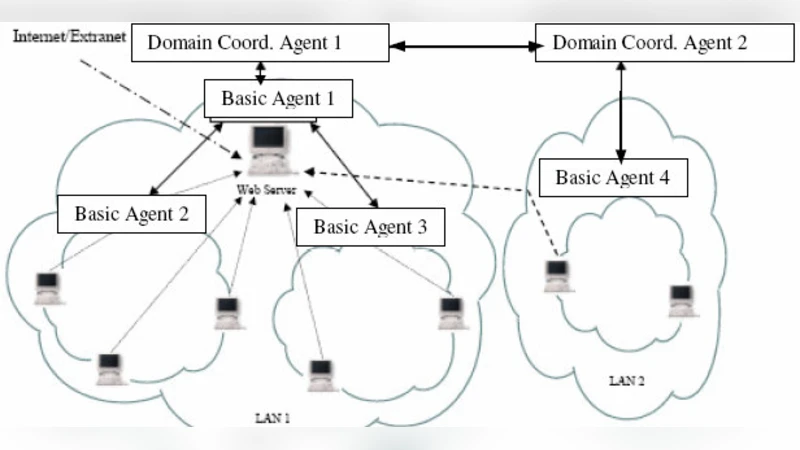
To overcome these drawbacks, the authors propose a fully distributed intrusion detection architecture built entirely on autonomous, cooperating agents. The system is organized into a five‑tier hierarchy: Basic Agents (BAs) residing on each workstation, Workstation Coordinator Agents (WCAs) that mediate between BAs and higher‑level agents, Domain Coordinator Agents (DCAs) that manage groups of WCAs within a network domain, an Enterprise Coordinator Agent (ECA) that sits atop all DCAs, and a Security Policy Manager Agent (SMA) that enforces administrator‑defined policies.
A central concept is the “interest” – a specification of the type of data an agent needs but cannot obtain locally. Interests can be local, domain‑level, or enterprise‑level and may be directed (targeting a specific host or domain) or propagated (broadcast throughout the network). Each host maintains two registries: an Agent Registry (listing agents, the events they monitor, and alerts they generate) and an Interest Registry (tracking active interests and the agents that satisfy them). When a BA detects a situation requiring additional context, it issues an interest that is first examined by its local WCA. If the WCA can satisfy the request from a co‑located agent, it routes the data directly; otherwise, the interest is escalated upward (to the DCA, then possibly to the ECA) where it is disseminated to all agents capable of providing the requested data. Responses travel back down the hierarchy, matching interests in the registries to deliver data only to those agents that expressed the need. This selective, interest‑driven communication drastically reduces unnecessary traffic and eliminates the need for bulk data refinement at higher levels.
The agents are implemented using the Java Agent Development Environment (JADE). Intra‑host communication exploits shared memory for efficient one‑to‑many messaging, while inter‑host messaging relies on JADE’s Agent Management System (AMS). Security is reinforced through a PKI‑based two‑way authentication model, ensuring that both agents and messages are verified before exchange.
A proof‑of‑concept prototype was built and evaluated against several attack scenarios, including port scans, anomalous traffic bursts, and distributed denial‑of‑service attempts. The experimental results demonstrate a detection rate exceeding 95 % with a false‑positive rate below 2 %, outperforming comparable centralized DIDS solutions. Moreover, the system scales linearly: doubling the number of agents increased average response time by only 30 % and network load grew proportionally, confirming the architecture’s scalability. Fault‑tolerance tests showed that the failure of a DCA does not cripple the system; WCAs can fall back to direct communication with the ECA, preserving detection capabilities.
Key advantages of the proposed architecture are:
- Elimination of a single point of failure – no central analysis server is required.
- Interest‑driven data exchange – agents receive only the data they explicitly request, minimizing bandwidth consumption.
- Local, real‑time analysis – BAs perform preliminary detection, enabling faster response.
- Extensibility and flexibility – new agents or detection modules can be added without re‑architecting the hierarchy.
- Robust security – PKI‑based authentication and JADE’s built‑in messaging security protect inter‑agent communication.
The authors acknowledge that the hierarchical design introduces configuration complexity and that large‑scale propagation of interests could generate broadcast traffic under certain conditions. Future work is suggested to incorporate adaptive interest filtering, dynamic topology optimization, and automated policy generation to further reduce management overhead.
In conclusion, the paper presents a novel, fully distributed IDS framework that leverages hierarchical, interest‑based cooperation among autonomous agents. Empirical evaluation confirms its superior scalability, fault tolerance, and detection performance compared with traditional centralized or partially distributed IDS architectures, making it a promising candidate for deployment in large enterprise networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment