A Graphical Password Based System for Small Mobile Devices
Passwords provide security mechanism for authentication and protection services against unwanted access to resources. A graphical based password is one promising alternatives of textual passwords. According to human psychology, humans are able to remember pictures easily. In this paper, we have proposed a new hybrid graphical password based system, which is a combination of recognition and recall based techniques that offers many advantages over the existing systems and may be more convenient for the user. Our scheme is resistant to shoulder surfing attack and many other attacks on graphical passwords. This scheme is proposed for smart mobile devices (like smart phones i.e. ipod, iphone, PDAs etc) which are more handy and convenient to use than traditional desktop computer systems.
💡 Research Summary
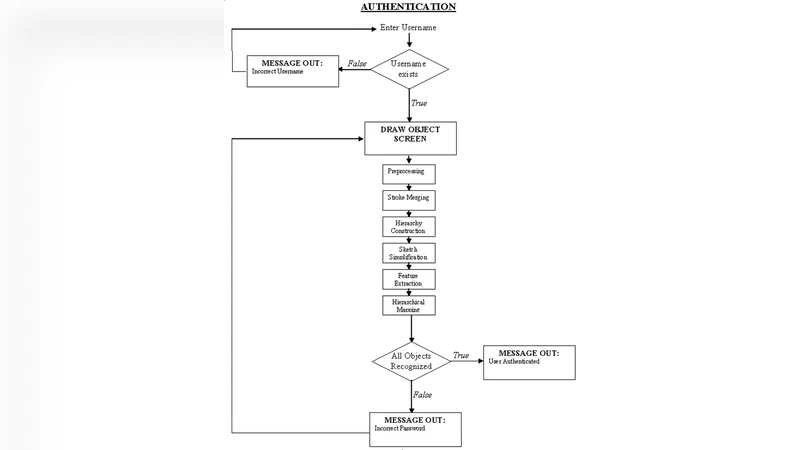
The paper proposes a hybrid graphical password scheme tailored for small mobile devices such as smartphones and PDAs. Recognizing the shortcomings of traditional textual passwords (poor memorability) and existing graphical password schemes (vulnerability to shoulder‑surfing and slow login), the authors combine recognition‑based and recall‑based techniques into a two‑phase process. In the registration phase, the user first enters a conventional username and textual password. Then a set of images is presented; the user selects one or more objects and draws each selected object on a touch‑sensitive screen using a stylus or finger. The drawing (coordinates, stroke order, possibly pressure data) is stored as the graphical component of the password. During authentication, the user repeats the same steps: entering the username and textual password, then reproducing the previously drawn objects. Successful authentication requires an exact (or within‑tolerance) match of the drawing.
The authors argue that this design mitigates shoulder‑surfing because the critical secret is the user’s drawing rather than visible image selections, and the dual‑factor nature (text + drawing) prevents an attacker who compromises only one factor from gaining access. They also claim compatibility with a range of mobile devices that support handwriting recognition, citing examples such as i‑Mode phones, Palm Pilots, and other 240×320 pixel devices.
The paper includes a literature review that classifies authentication methods into token‑based, biometric, and knowledge‑based categories, and further classifies graphical password schemes into recognition, pure recall, cued recall, and hybrid approaches. It surveys related work such as DAS, PassPoints, Passlogix, Passface, Déjà Vu, and recent hybrid proposals like CDS and Two‑Step, highlighting each method’s strengths and weaknesses, especially regarding shoulder‑surfing resistance and usability.
In the problem analysis, the authors identify several issues with existing schemes: large server storage for image databases, the need to remember precise grid coordinates, low password space for some methods, and difficulty of input on small screens. They suggest that their hybrid approach alleviates many of these problems by allowing users to draw familiar objects rather than remembering exact coordinates, while still providing a sizable password space due to the variability of drawing strokes.
However, the paper lacks empirical evaluation. No user study, timing measurements, or quantitative security analysis (e.g., entropy calculations, resistance to specific attacks such as video capture, smudge attacks, or brute‑force on the drawing space) is presented. Implementation details are deliberately omitted, stating they are “out of scope,” leaving open questions about how tolerance thresholds are set, how drawing variations are handled, and how the system scales with many users. The storage of selected images and drawing data in plaintext on the server is also a potential vulnerability not addressed.
In conclusion, the proposed system is an interesting conceptual combination of textual and graphical authentication that aims to improve memorability and resistance to observation attacks on mobile platforms. Its practicality, however, remains unproven due to the absence of experimental validation, detailed implementation guidelines, and rigorous security analysis. Future work should focus on user studies to assess memorability and login time, formal entropy evaluation of the drawing space, tolerance parameter optimization, and secure storage mechanisms for the image and drawing data.
Comments & Academic Discussion
Loading comments...
Leave a Comment