DDNFS: a Distributed Digital Notary File System
Safeguarding online communications using public key cryptography is a well-established practice today, but with the increasing reliance on `faceless’, solely online entities one of the core aspects of public key cryptography is becoming a substantial problem in practice: Who can we trust to introduce us to and vouch for some online party whose public key we see for the first time? Most existing certification models lack flexibility and have come under attack repeatedly in recent years, and finding practical improvements has a high priority. We propose that the real-world concept of a notary or certifying witness can be adapted to today’s online environment quite easily, and that such a system when combined with peer-to-peer technologies for defense in depth is a viable alternative to monolithic trust infrastructures. Instead of trusting assurances from a single party, integrity certifications (and data replication) can be provided among a group of independent parties in a peer-to-peer fashion. As the likelihood of all such assurance providers being subverted at the very same time is very much less than that of a single party, overall robustness is improved. This paper presents the design and the implementation of our prototype online notary system where independent computer notaries provide integrity certification and highly-available replicated storage, and discusses how this online notary system handles some common threat patterns.
💡 Research Summary
The paper introduces DDNFS (Distributed Digital Notary File System), a novel approach that adapts the real‑world concept of a notary to the digital realm in order to address the trust problem inherent in “faceless” online interactions. The authors argue that relying on a single Certification Authority (CA) or a monolithic PKI is increasingly untenable, as recent incidents have shown. Instead, they propose a peer‑to‑peer (P2P) system where multiple independent “digital notaries” jointly certify and replicate files, thereby reducing the probability that all trust anchors are simultaneously compromised.
The related‑work discussion situates DDNFS among systems such as Bayou, which provides weakly consistent replication, and epidemic (rumor‑mongering) algorithms that efficiently disseminate updates in large, unreliable networks. While Bayou lacks Byzantine fault tolerance and rumor‑mongering does not guard against malicious misinformation, DDNFS combines the strengths of both: it uses a push‑pull hybrid epidemic flooding mechanism for data dissemination and augments each message with a signed history (round counter and peer list), creating a “verifiable rumor” that can be cryptographically validated by recipients.
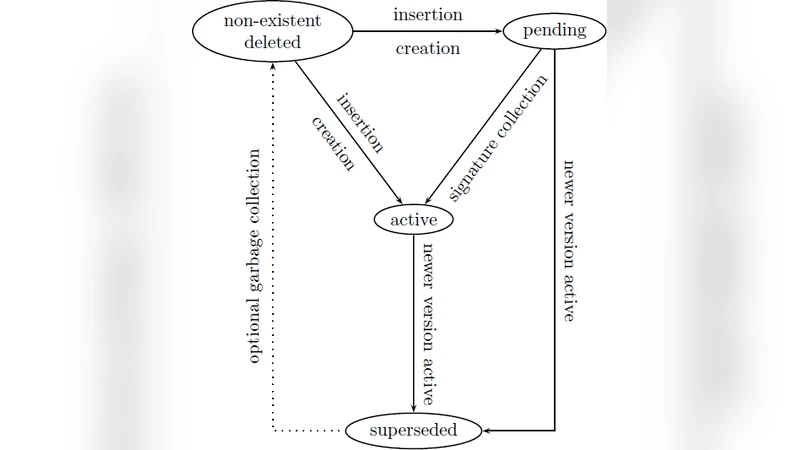
The design comprises four core components: (1) Peers – autonomous computers running the DDNFS client; (2) Network – an untrusted, possibly intermittent Internet connection; (3) Documents – immutable, fixed‑size objects identified by pathname and version; and (4) Policy – per‑document rules that specify the required number of certifications, author restrictions, and version‑supersession conditions. Administrators can modify policies remotely and add temporary peers to the system.
The Document Distribution Protocol works as follows: during each push round, a peer randomly selects a subset of other peers and sends the document together with a signed metadata block containing the current round number and a list of peers that have already been offered the document. Recipients verify the signatures, discard duplicates, and, if the document is new, increment the round counter and possibly forward it further. After the push phase, peers that missed the update can issue pull requests to obtain the latest version. A document becomes “committed” once it has gathered the minimum number of independent signatures required by its policy, at which point it can be safely read.
Security analysis covers several threat models: (a) malicious peers attempting to forge signatures – mitigated by mandatory signature verification; (b) network partition attacks – mitigated by the statistical resilience of random peer selection and the requirement for multiple independent certifications; (c) credential compromise – acknowledged as a risk that necessitates revocation and re‑issuance mechanisms not fully detailed in the prototype.
Implementation details reveal a lightweight POSIX‑based prototype written in C/C++. The system presents an overlay file system interface, allowing users to interact with files as if they were local; the underlying DDNFS client handles replication, certification, and consistency transparently. The codebase is deliberately small (≈30 KB), emphasizing simplicity and ease of deployment.
In conclusion, DDNFS demonstrates that a distributed notary model can provide strong integrity guarantees and high availability without relying on a single trusted authority. The approach effectively merges concepts from weakly consistent replication, epidemic dissemination, and multi‑party digital signatures. Limitations include reduced effectiveness when the peer population is small (fewer independent certifications) and the operational complexity of managing per‑document policies. Future work is suggested in the areas of dynamic trust scoring, automated certificate revocation, and scaling performance analyses for large‑scale deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment