Indices of Power in Optimal IDS Default Configuration: Theory and Examples
Intrusion Detection Systems (IDSs) are becoming essential to protecting modern information infrastructures. The effectiveness of an IDS is directly related to the computational resources at its disposal. However, it is difficult to guarantee especially with an increasing demand of network capacity and rapid proliferation of attacks. On the other hand, modern intrusions often come as sequences of attacks to reach some predefined goals. It is therefore critical to identify the best default IDS configuration to attain the highest possible overall protection within a given resource budget. This paper proposes a game theory based solution to the problem of optimal signature-based IDS configuration under resource constraints. We apply the concepts of indices of power, namely, Shapley value and Banzhaf-Coleman index, from cooperative game theory to quantify the influence or contribution of libraries in an IDS with respect to given attack graphs. Such valuations take into consideration the knowledge on common attack graphs and experienced system attacks and are used to configure an IDS optimally at its default state by solving a knapsack optimization problem.
💡 Research Summary
The paper tackles the problem of configuring a signature‑based Intrusion Detection System (IDS) under strict resource constraints, a challenge that becomes increasingly acute as modern networks grow in bandwidth and the volume of attacks explodes. While many IDSs (e.g., Snort) ship with thousands of signature rules, it is infeasible to enable all of them simultaneously because each rule consumes CPU, memory, and I/O bandwidth. Consequently, the authors aim to determine the most effective “default” configuration – the set of detection libraries that should be loaded when no additional contextual information is available – such that the overall protection is maximized for a given budget.
Modeling the environment
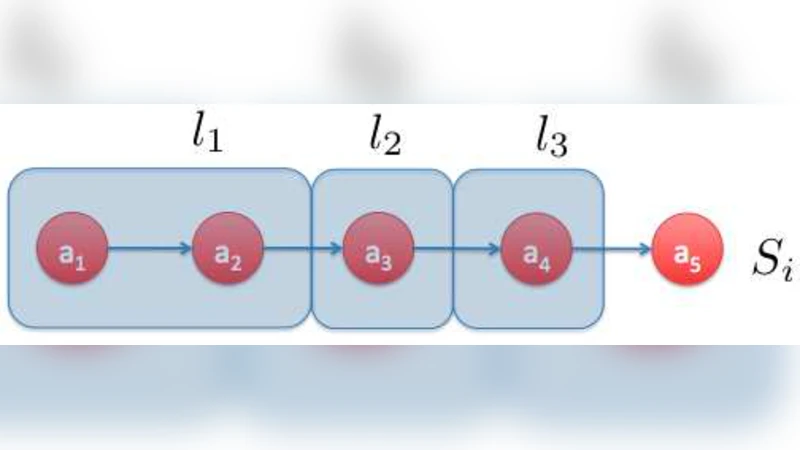
The authors first formalize the IDS components as a finite set of libraries (L={l_1,\dots,l_N}). Each library (l_i) has an associated cost (c_i=C(l_i)>0) and a detection scope (P_i\subseteq A), where (A={a_1,\dots,a_M}) denotes the universe of possible atomic attacks. An attacker’s campaign is modeled as a sequence (S\in A^*); the damage of a single attack (a_j) is given by a non‑negative function (D(a_j)). Importantly, detection is not binary: the probability that library (l_i) successfully detects attack (a_j) is denoted (\alpha_{ij}) (true‑positive rate), with (\alpha_{ij}=0) when (a_j\notin P_i). The false‑negative rate is (\alpha^N_{ij}=1-\alpha_{ij}).
Detectability metrics
A value function (v: A^*\rightarrow\mathbb{R}^+) quantifies the importance of an attack sequence (the simplest choice is cardinality, (v(S)=|S|), but weighted versions are possible). For a single library (l_i) and a campaign (S), the detection effectiveness is defined as
\
Comments & Academic Discussion
Loading comments...
Leave a Comment