Enhanced Secure Algorithm for Message Communion
This paper puts forward a safe mechanism of data transmission to tackle the security problem of information which is transmitted in Internet. The encryption standards such as DES (Data Encryption Standard), AES (Advanced Encryption Standard) and EES (Escrowed Encryption Standard) are widely used to solve the problem of communication over an insecure channel. With advanced technologies in computer hardware and software, these standards seem not to be as secure and fast as one would like. In this paper we propose a encryption technique which provides security to both the message and the secret key achieving confidentiality and authentication. The Symmetric algorithm used has two advantages over traditional schemes. First, the encryption and decryption procedures are much simpler, and consequently, much faster. Second, the security level is higher due to the inherent poly-alphabetic nature of the substitution mapping method used here, together with the translation and transposition operations performed in the algorithm. Asymmetric algorithm RSA is worldwide known for its high security. In this paper a detailed report of the process is presented and analysis is done comparing our proposed technique with familiar techniques
💡 Research Summary
The paper “Enhanced Secure Algorithm for Message Communication” proposes a hybrid cryptographic scheme that combines a modified version of the Fast and Secure Encryption Technique (FSET) with RSA public‑key encryption and SHA‑2 hashing. The authors argue that conventional symmetric ciphers such as DES, AES, and EES no longer provide sufficient speed or security for modern high‑throughput applications, especially when encrypting multimedia data. To address these perceived shortcomings, they design a new system that encrypts the actual payload with a symmetric algorithm (FSET) while protecting the symmetric key and a message authentication hash using RSA.
The FSET component works on 128‑bit (16‑character) blocks and a 128‑bit secret key. During initialization a 16‑row by 256‑column matrix is filled with the full ASCII range (0‑255). Each row is circularly shifted a number of positions equal to the ASCII value of a corresponding key byte, first using the next key byte and then using the current key byte, resulting in a key‑dependent permutation of the matrix. For each plaintext block, the algorithm maps every character to a “level‑one” ciphertext character by selecting the matrix entry at row i and column equal to the ASCII code of the i‑th plaintext character. The 16 resulting characters are placed in an array A1.
Eight rounds of “translation” and “transposition” follow. Translation consists of XOR‑ing the entire array A1 with a round sub‑key Kts_n derived from the matrix row n (columns 0‑15 concatenated). Transposition uses four additional sub‑keys Ktp_n0…Ktp_n3 (single matrix entries) to perform a series of circular shifts and a split‑merge of A1 into two 8‑element sub‑arrays (A2, A3), each shifted independently, then recombined and shifted again. After the eighth round the final ciphertext block is emitted. Decryption reverses these steps: the matrix is rebuilt from the secret key, the transposition and translation operations are undone, and the inverse mapping retrieves the original plaintext characters.
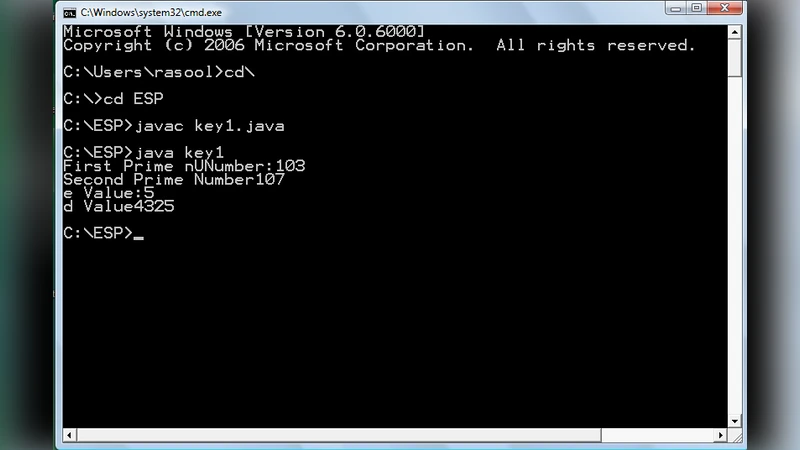
Key exchange and authentication are handled by RSA and SHA‑2. The receiver generates an RSA key pair (public (e, n) and private (d, n)) and publishes the public key. The sender computes a SHA‑2 hash h of the plaintext message, XORs h with the secret key K_s to obtain hmk = h ⊕ K_s, and then encrypts both K_s and hmk with the receiver’s public RSA key. The encrypted payload, encrypted hmk, and encrypted K_s are transmitted. The receiver decrypts K_s and hmk using the private RSA exponent, recovers h by XOR‑ing hmk with K_s, and finally decrypts the payload with FSET using K_s. A second SHA‑2 hash of the recovered plaintext is compared with h to verify integrity and authenticity.
The authors claim that the proposed scheme offers higher speed because the matrix‑based substitution and the simple XOR/shift operations are computationally lightweight, and higher security because the poly‑alphabetic substitution (different mapping per character position) together with eight rounds of diffusion makes cryptanalysis difficult. They also assert that RSA provides robust key protection and that SHA‑2 guarantees message authentication.
However, the paper suffers from several critical deficiencies:
-
Lack of Formal Security Analysis – No proofs or reductions to standard security notions (e.g., IND‑CPA, IND‑CCA) are provided. The security of the FSET component is argued qualitatively, without demonstrating resistance to known‑plaintext, chosen‑plaintext, or differential attacks. The key schedule, which simply extracts bytes from the same matrix used for substitution, may be vulnerable to related‑key attacks.
-
Key Space and Entropy Concerns – The secret key is 16 ASCII characters, each ranging from 0‑255, yielding a nominal 2^128 space. Yet the matrix initialization depends on the exact ASCII values, and the subsequent sub‑keys are deterministic functions of the same key. This deterministic derivation reduces effective entropy and may expose structural weaknesses.
-
Performance Evaluation Missing – Although the authors repeatedly claim “much faster” encryption, the manuscript contains no empirical timing results, throughput measurements, or memory usage data. The only reference to a comparison table is a vague mention of DES and AES, but the table itself is absent.
-
RSA Implementation Details Omitted – The RSA encryption of the secret key and hmk is described without specifying padding (e.g., OAEP) or message size handling. Without proper padding, RSA encryption is vulnerable to textbook attacks. Moreover, encrypting the XOR of hash and key (hmk) does not add meaningful security beyond protecting the hash; an attacker who recovers the secret key can recompute the hash directly.
-
Clarity and Reproducibility Issues – The paper contains numerous typographical errors, inconsistent notation, and incomplete algorithmic descriptions (e.g., exact order of the two circular shifts per row, handling of overflow when ASCII values exceed 255). Figures are referenced but not included, and pseudo‑code is absent, making replication difficult.
-
Comparison with Existing Work – The authors cite a “FSET” algorithm by Varghese Paul but do not provide a thorough comparative analysis. It is unclear whether the modifications truly improve security or merely re‑package existing ideas.
In summary, the proposed hybrid system is an interesting attempt to blend a custom symmetric cipher with established public‑key and hash primitives. Nevertheless, the lack of rigorous security proofs, missing performance data, and ambiguous implementation details undermine its credibility as a practical cryptographic solution. Future work would need to address these gaps by providing formal security reductions, detailed benchmark results on modern hardware, and a clear specification that can be independently verified.
Comments & Academic Discussion
Loading comments...
Leave a Comment