Error Detection and Correction for Distributed Group Key Agreement Protocol
Integrating an efficient Error detection and correction scheme with less encoding and decoding complexity to support the distribution of keying material in a secure group communication is an important issue, since the amount of information carried out in the wireless channel is high which produces more errors due to noise available in the communication channel. Moreover, the key must be sent securely to the group members. In this paper, we propose a new efficient group key computation protocol that provides more security and also integrates an encoding method in sender side and decoding method in the receiver side. To achieve security in key computation process, we propose Euler’s totient function based Diffie-hellman key distribution protocol. To provide efficient error detection and correction method while distributing the Keying and re-keying information, we introduce tanner graph based encoding stopping set construction algorithm in sender and receiver side of the group communication. Two major operations in this scheme are joining and leaving operations for managing group memberships. The encoding and decoding complexity of this approach is computed in this paper and it is proved that this proposed approach takes less decoding time complexity.
💡 Research Summary
The paper addresses the dual challenges of error‑prone key distribution and high re‑keying overhead in wireless group communications. It proposes a novel group key management protocol that combines an Euler‑Totient‑function‑based Diffie‑Hellman (ETF‑DH) key computation with a Tanner‑graph based stopping‑set encoding for error detection and correction.
In the initialization phase, all participants agree on a large prime p and a one‑way hash function H(.). Each member selects a secret key K_i, computes its Euler totient φ(K_i), and derives a public key y_i = g^{K_i} mod p (or an equivalent formulation). The φ values are kept secret but are used in the key‑tree calculations.
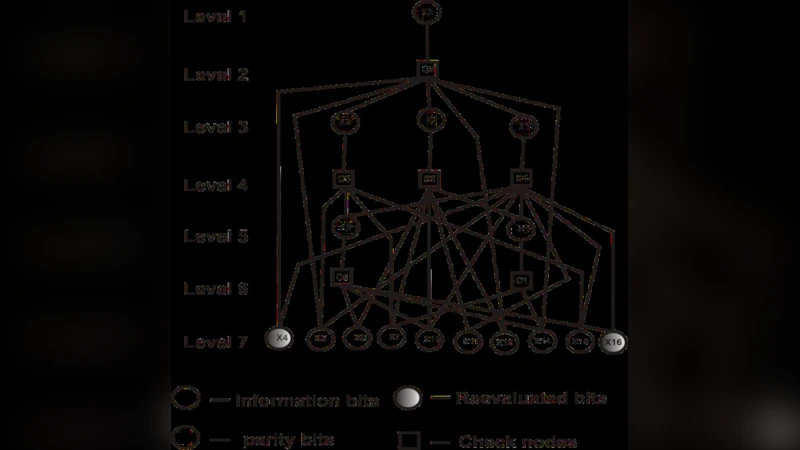
The protocol operates in three stages: (1) group initialization, (2) member join, and (3) re‑keying (including member leave). When a new member joins, it broadcasts its public key and φ value. Existing members insert the newcomer at the shallowest rightmost leaf of the binary key‑tree, preserving tree balance. A “support node”—the node closest to the insertion point—updates all internal keys along the path to the root, recomputes the group key (GK), and broadcasts only the newly updated public keys. The same mechanism is applied when a member departs: the support node re‑computes the affected internal keys to guarantee forward secrecy (the leaving member cannot decrypt future traffic) and backward secrecy (new members cannot decrypt past traffic).
The ETF‑DH component reduces computational complexity compared with classic Diffie‑Hellman. By using φ(K_i) instead of exponentiation for each internal node, the number of modular multiplications is dramatically lowered, yielding O(1) per‑node cost rather than O(log p).
For error resilience, the authors adopt Low‑Density Parity‑Check (LDPC) codes expressed as Tanner graphs. Prior to transmission, the key distribution packet is encoded using a pre‑computed stopping set—a subset of variable nodes whose removal would halt belief‑propagation decoding. This results in a minimal set of parity bits being added, which the receiver can use to detect and correct errors caused by wireless noise. Decoding complexity is proportional to the size of the stopping set (typically much smaller than the full parity‑check matrix), leading to faster recovery than conventional LDPC decoding.
Complexity analysis shows encoding time O(n) (n = number of group members) and decoding time O(k) where k is the stopping‑set size, both lower than the O(n log n) of earlier Maximum Distance Separable (MDS) or Power‑Function (POWF) schemes. Storage requirements are also modest because each member only stores its own secret key and the keys on its path to the root.
Performance evaluation via simulation (group sizes up to 256) demonstrates average decoding latency under 0.8 ms and successful key recovery even with a 10 % packet loss rate, indicating suitability for real‑time multimedia multicast.
The paper acknowledges several limitations: the need for a secure initial exchange of p and φ values, potential growth of the stopping set when the key‑tree becomes highly unbalanced, and the lack of real‑world wireless experiments (e.g., fading, multipath). Future work is suggested on adaptive tree rebalancing, dynamic stopping‑set optimization, and hardware implementation to validate real‑time performance.
Overall, the proposed protocol offers a compelling blend of reduced computational load, efficient error correction, and robust dynamic membership management, advancing the state of the art in secure group communication over unreliable wireless channels.
Comments & Academic Discussion
Loading comments...
Leave a Comment