A Contribution to Secure the Routing Protocol "Greedy Perimeter Stateless Routing" Using a Symmetric Signature-Based AES and MD5 Hash
This work presents a contribution to secure the routing protocol GPSR (Greedy Perimeter Stateless Routing) for vehicular ad hoc networks, we examine the possible attacks against GPSR and security solutions proposed by different research teams working on ad hoc network security. Then, we propose a solution to secure GPSR packet by adding a digital signature based on symmetric cryptography generated using the AES algorithm and the MD5 hash function more suited to a mobile environment.
💡 Research Summary
The paper addresses security weaknesses in the Greedy Perimeter Stateless Routing (GPSR) protocol, which is widely used in vehicular ad‑hoc networks (VANETs). After outlining the dynamic and infrastructure‑less nature of VANETs, the authors enumerate the main attacks that can compromise routing: (1) false traffic generation (identity spoofing, falsified position information) and (2) incorrect relaying (black‑hole, packet modification). They review existing secure routing solutions such as SRP, SAODV, and Ariadne, noting that most rely on public‑key infrastructure (PKI) and therefore may be unsuitable for highly mobile, resource‑constrained vehicular environments.
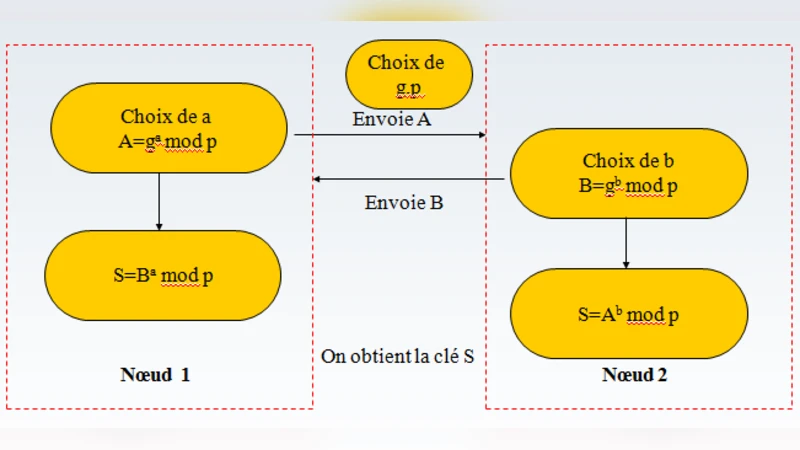
The core contribution is a symmetric‑key based “digital signature” mechanism. When two neighboring nodes first discover each other, they perform a Diffie‑Hellman key exchange to derive a shared secret key. This key is then used as the AES encryption key (128, 192 or 256 bits). For each GPSR packet, the sender computes an MD5 hash over the entire packet header, encrypts the 128‑bit hash with AES, and places the ciphertext in a newly added “Authentication” field of the packet. The receiver decrypts the field with the same shared key, recomputes the MD5 hash of the received packet, and compares the two values. If they match, the packet is considered authentic and unaltered. The authors refer to this process as a digital signature, although it is essentially a symmetric‑key MAC.
To justify the choice of AES, the authors implement both AES and Blowfish in Java and measure encryption/decryption latency using System.nanoTime for 128‑bit and 256‑bit keys on 512‑byte messages. Their results show AES to be roughly 30 % faster than Blowfish, which they argue makes AES more appropriate for the real‑time constraints of VANETs. They also propose a modified GPSR packet format that adds the 16‑byte authentication field to the existing header fields (version, command, reserved, length, source position, optional perimeter position, destination position, edge coordinates, port, and data payload).
While the proposal is conceptually straightforward, several critical issues arise. First, MD5 is known to be vulnerable to collision attacks; using it for integrity protection is insecure in modern contexts. Second, the scheme relies on a per‑neighbor shared secret, leading to O(n²) key management overhead in dense networks, and the paper does not discuss key distribution, revocation, or scalability. Third, unauthenticated Diffie‑Hellman is susceptible to man‑in‑the‑middle attacks, which could allow an adversary to inject forged packets. Fourth, the “signature” only guarantees one‑hop integrity; there is no mechanism for end‑to‑end verification across multiple hops, which is essential for routing protocols. Finally, the experimental evaluation is limited to raw cryptographic execution time; it lacks simulation or real‑world testing of routing performance, packet loss, latency, or throughput under realistic vehicular mobility models.
In conclusion, the paper presents an interesting attempt to secure GPSR using lightweight symmetric cryptography, demonstrating that AES can be efficiently employed on typical vehicular hardware. However, the reliance on MD5, the lack of robust key management, and the absence of comprehensive performance and security analyses limit the practical applicability of the solution. Future work should replace MD5 with a modern hash (e.g., SHA‑256), adopt authenticated key exchange (e.g., ECDH with certificates or identity‑based signatures), explore scalable key distribution schemes, and evaluate the impact on routing metrics through detailed VANET simulations.
Comments & Academic Discussion
Loading comments...
Leave a Comment