Hilbert Matrix Based Cryptosystem using a Session Key
Cryptography protects users by providing functionality for the encryption of data and authentication of other users. This technology lets the receiver of an electronic message verify the sender, ensures that a message can be read only by the intended person, and assures the recipient that a message has not be altered in transit. Classical cryptanalysis involves an interesting combination of analytical reasoning, application of mathematical tools and pattern finding. The objectives of the proposed work are to propose a new cryptographic method based on the special matrix called the Hilbert matrix for authentication and confidentiality and to propose a model for confidentiality and authentication using shared key cryptosystems with the concept of digital enveloping using a session key. In the present work various algorithms are presented for encryption and authentication based on Hilbert matrix using a session key.
💡 Research Summary
The paper proposes a novel cryptographic scheme that combines a Hilbert matrix–based symmetric encryption with session‑key techniques and RSA‑based digital enveloping. The authors argue that the special properties of the Hilbert matrix—its guaranteed invertibility for any order and the integer nature of its inverse—make it a suitable building block for a secure cipher. The system works as follows: a large prime is chosen and used to generate a secret session key n (the dimension of the Hilbert matrix) and a secret string K. The plaintext P is written as an m‑by‑1 column vector; a random padding of length (n‑m) is appended to form an n‑by‑1 vector T. The n×n Hilbert matrix H is multiplied by T, producing the ciphertext C = H·T. To protect the session parameters, n and the length m (or a derived value) are encrypted with the receiver’s RSA public key, yielding n′ and m′. The final transmitted package consists of C together with the RSA‑encrypted values n′ and m′ (and optionally K′, the RSA‑encrypted K).
On the receiver side, the RSA private key is used to recover n and m, the inverse Hilbert matrix H⁻¹ is computed, and H⁻¹·C yields T. The first m entries of T give the original plaintext P, while the trailing random padding is discarded. For authentication, the secret string K is also encrypted with RSA (producing K′). After decryption, the receiver compares the recovered K with K′; a match confirms the integrity and authenticity of the message. The random padding thus serves a dual purpose: obscuring the true size of the secret key and acting as a simple hash‑like tag.
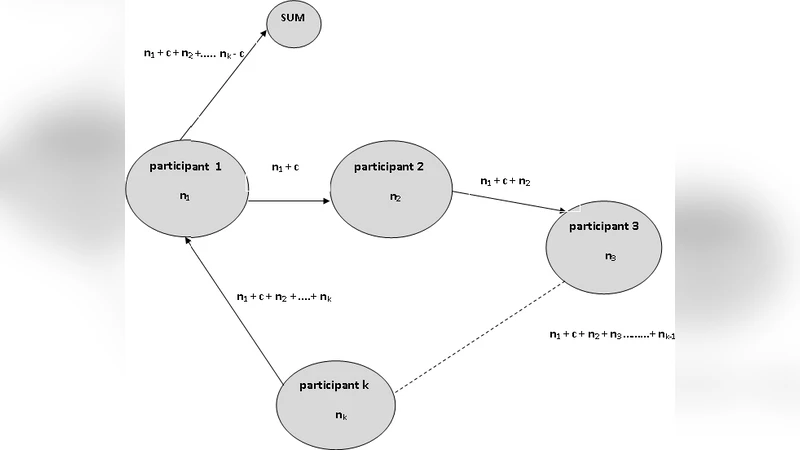
Beyond the basic two‑party scenario, the authors extend the construction to a multi‑party shared‑key environment. Each of k participants selects a private secret n_i. Through a sequential “sum protocol,” participants add their secret to an accumulating total and finally broadcast the sum n = Σ n_i to all parties. This shared value n becomes the common Hilbert matrix dimension for subsequent encryption. The shared‑key protocol is described in a series of steps but lacks cryptographic safeguards against intermediate value leakage.
The paper lists several claimed advantages of using Hilbert matrices: (1) they are always invertible; (2) their inverses consist of integer (actually rational) entries; (3) knowing the order n makes inversion straightforward, while an unknown order makes it “practically impossible” to recover the plaintext; (4) direct inversion suffers from rounding errors due to the matrix’s ill‑conditioned nature, which the authors paradoxically present as a security feature.
Critically, the manuscript suffers from several serious shortcomings. First, Hilbert matrices are notoriously ill‑conditioned; numerical inversion for large n is highly unstable, and any implementation relying on floating‑point arithmetic will introduce errors that can corrupt decryption. Although the authors claim integer inverses, the true entries are rational numbers, requiring exact arithmetic or arbitrary‑precision rational libraries, which are computationally expensive. Second, the core transformation C = H·T is linear. If an attacker obtains a modest number of plaintext‑ciphertext pairs (a realistic scenario in many communication settings), the Hilbert matrix H can be recovered by solving a system of linear equations, rendering the scheme vulnerable to known‑plaintext or chosen‑plaintext attacks. The secrecy of n is the only barrier; once n is guessed or inferred, the attack becomes trivial. Third, the use of RSA to protect n, m, and K is essentially a standard hybrid encryption approach that adds no novel security beyond what conventional protocols already provide. The paper does not discuss key sizes, padding schemes, or resistance to RSA‑specific attacks, leaving the overall security level undefined. Fourth, the multi‑party sum protocol does not incorporate any commitment or zero‑knowledge proof, so intermediate sums could be intercepted and used to infer individual n_i values, compromising the secrecy of the shared key.
Furthermore, the manuscript lacks any performance evaluation, security analysis, or formal proof. No experimental data are presented to demonstrate that the Hilbert‑based encryption is faster or more secure than existing symmetric ciphers (e.g., AES). The authors also do not address practical issues such as storage of large Hilbert matrices, generation of exact inverses, or resistance to side‑channel attacks.
In conclusion, while the paper introduces an interesting idea of leveraging the mathematical peculiarities of Hilbert matrices within a cryptographic framework, the proposal is not substantiated by rigorous analysis or empirical validation. The linear nature of the transformation, numerical instability, and insufficient key‑management safeguards raise significant doubts about its practical security. Future work would need to provide formal security proofs, robust implementation strategies (e.g., exact rational arithmetic), comprehensive performance benchmarks, and a more sophisticated multi‑party protocol that protects intermediate values. Only then could the Hilbert‑matrix approach be considered a viable alternative to established cryptographic primitives.
Comments & Academic Discussion
Loading comments...
Leave a Comment