A Cryptosystem Based on Hilbert Matrix using Cipher Block Chaining Mode
Cryptography is the science of using mathematics to encrypt and decrypt data. Cryptography enables you to store sensitive information or transmit it across insecure networks so that it cannot be read by anyone except the intended recipient. While cryptography is the science of securing data, cryptanalysis is the science of analyzing and breaking secure communication. Classical cryptanalysis involves an interesting combination of analytical reasoning, application of mathematical tools and pattern finding. The objectives of the proposed work are to propose a new cryptographic method based on the special matrix called the Hilbert matrix for authentication and confidentiality and to propose a model for confidentiality and authentication using a combination of symmetric and public cryptosystems. Further, it is extended to shared key cryptosystems with the concept of digital enveloping using a session key. In the present work an algorithm for shared key encryption is developed using Hilbert matrix cryptosystem. In this the block chaining modes of operation have been used to tackle the issues of confusion and diffusion.
💡 Research Summary
The paper proposes a novel symmetric‑key cryptosystem that leverages the special properties of the Hilbert matrix, and it integrates this construction with Cipher Block Chaining (CBC) mode and a digital‑enveloping technique to achieve both confidentiality and authentication in a shared‑key setting. After reviewing existing symmetric and public‑key schemes, the authors introduce several special matrices (Vandermonde, combinatorial, Cauchy, and Hilbert) and focus on the Hilbert matrix because it is a symmetric, positive‑definite Cauchy matrix whose inverse consists entirely of integer entries. This integer‑only inverse eliminates the common problem in Hill‑type ciphers where the inverse matrix contains non‑integral values that complicate decryption.
Key generation begins by selecting a large prime number n, which serves as the size of the Hilbert matrix and is kept secret between the communicating parties. The plaintext is represented as an m‑by‑1 column vector (with m < n). A secret string K of length (n − m) is chosen, encrypted with the receiver’s public key, and transmitted securely. The encrypted K is then concatenated with the plaintext vector to form an n‑by‑1 vector, which is multiplied by the n × n Hilbert matrix H to produce the ciphertext C. The ciphertext is sent to the receiver.
Decryption is straightforward because both H and its inverse H⁻¹ are known to the receiver. Multiplying C by H⁻¹ yields the original n‑by‑1 vector, from which the first m entries constitute the plaintext and the remaining (n − m) entries recover the secret string K (which can be decrypted with the receiver’s private key).
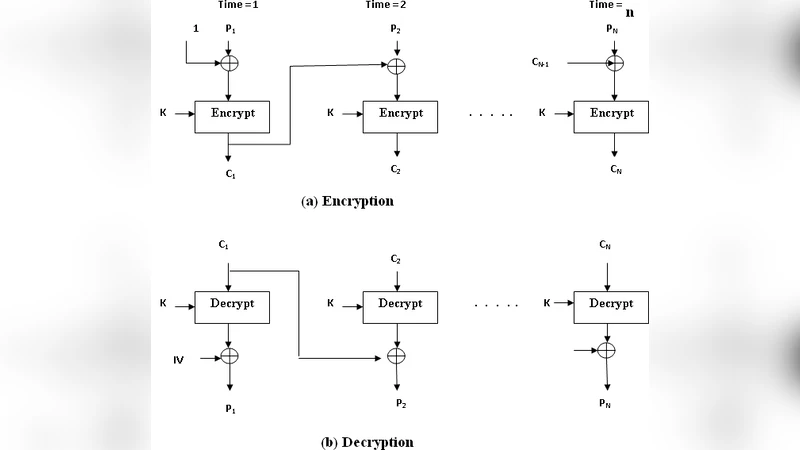
To address the weakness of deterministic block encryption (identical plaintext blocks yielding identical ciphertext blocks), the authors adopt CBC mode. Each plaintext block is XORed with the previous ciphertext block (or an initialization vector for the first block) before Hilbert‑matrix multiplication, thereby providing diffusion and preventing pattern leakage. The paper notes that the IV must be transmitted securely and not reused.
Security analysis hinges on the secrecy of n and the length of K. A sufficiently large prime n makes it computationally infeasible to reconstruct H⁻¹ without knowledge of n, and a long K prevents brute‑force recovery of the session key. However, the scheme requires a pre‑shared secret n, effectively a secure out‑of‑band channel, and the digital‑enveloping step adds complexity to key management. Moreover, Hilbert matrices are notoriously ill‑conditioned; as n grows, numerical instability can cause large rounding errors in floating‑point implementations, although the integer‑only inverse mitigates this to some extent. The computational cost is dominated by O(n³) matrix multiplication and inversion, which may be prohibitive for large n in real‑time applications.
The paper concludes that while the use of Hilbert matrices introduces an interesting mathematical twist and the combination with CBC improves confusion and diffusion, practical deployment would require careful handling of numerical stability, efficient integer matrix algorithms, and a robust protocol for exchanging n, K, and the IV. Future work is suggested to explore optimized integer‑based matrix operations, tighter integration of authentication mechanisms such as MACs or digital signatures, and performance benchmarking against established block ciphers.
Comments & Academic Discussion
Loading comments...
Leave a Comment