Trust transitivity in social networks
Non-centralized recommendation-based decision making is a central feature of several social and technological processes, such as market dynamics, peer-to-peer file-sharing and the web of trust of digital certification. We investigate the properties of trust propagation on networks, based on a simple metric of trust transitivity. We investigate analytically the percolation properties of trust transitivity in random networks with arbitrary degree distribution, and compare with numerical realizations. We find that the existence of a non-zero fraction of absolute trust (i.e. entirely confident trust) is a requirement for the viability of global trust propagation in large systems: The average pair-wise trust is marked by a discontinuous transition at a specific fraction of absolute trust, below which it vanishes. Furthermore, we perform an extensive analysis of the Pretty Good Privacy (PGP) web of trust, in view of the concepts introduced. We compare different scenarios of trust distribution: community- and authority-centered. We find that these scenarios lead to sharply different patterns of trust propagation, due to the segregation of authority hubs and densely-connected communities. While the authority-centered scenario is more efficient, and leads to higher average trust values, it favours weakly-connected “fringe” nodes, which are directly trusted by authorities. The community-centered scheme, on the other hand, favours nodes with intermediate degrees, in detriment of the authorities and its “fringe” peers.
💡 Research Summary
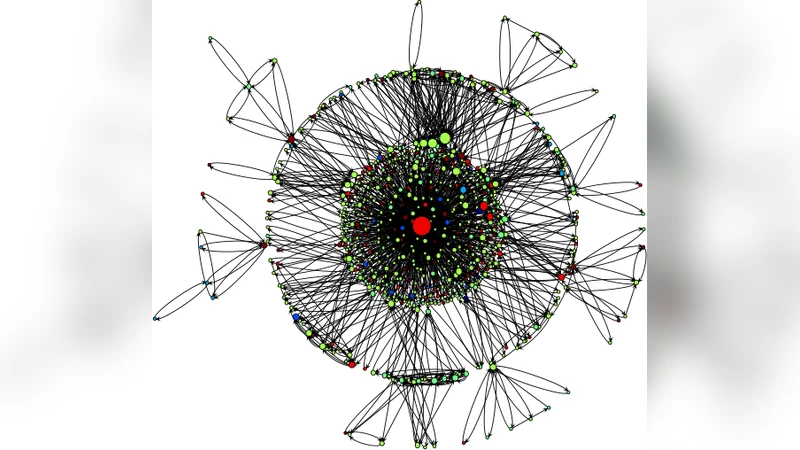
The paper investigates how trust propagates through complex networks by introducing a simple metric of trust transitivity and analyzing its percolation properties. Trust between two directly connected agents is modeled as a value close to one, while indirect trust is obtained by multiplying the trust values along a path. A key parameter is the fraction p of “absolute trust” (trust value exactly equal to one) present in the network. Using generating‑function techniques for random graphs with arbitrary degree distributions, the authors derive an analytical condition for a percolation transition. The transition is discontinuous: when p is below a critical threshold p_c, the average pairwise trust across the network collapses to zero; once p exceeds p_c, a finite, non‑zero average trust emerges abruptly. This result demonstrates that a non‑zero proportion of absolutely trusted links is a prerequisite for any large‑scale, global trust to be viable. In the limit p = 0, trust cannot percolate regardless of network size or degree heterogeneity.
To validate the theory, the authors examine the real‑world Pretty Good Privacy (PGP) web of trust. They construct two contrasting trust‑distribution scenarios. In the “authority‑centered” model, high‑degree nodes (certification authorities) hold many absolute‑trust links and directly endorse many low‑degree fringe nodes. In the “community‑centered” model, trust is exchanged primarily among nodes of similar degree, while the authority nodes possess only a limited set of absolute‑trust connections. Simulations on the empirical PGP topology reveal distinct propagation patterns. The authority‑centered scenario yields higher overall average trust and faster spread, but it creates a structural vulnerability: fringe nodes become overly dependent on a few authority hubs, and the removal or compromise of those hubs would dramatically reduce trust for a large portion of the network. Conversely, the community‑centered scenario distributes trust more evenly, giving intermediate‑degree nodes a pivotal role in bridging sub‑communities. Although the average trust is lower, the network is more resilient to targeted attacks on the authorities because trust does not rely on a single class of nodes.
The authors discuss the practical implications of these findings for a range of distributed systems, including peer‑to‑peer file sharing, recommendation engines, and blockchain‑based identity frameworks. They argue that system designers should ensure a minimal fraction of absolute‑trust links to guarantee a percolating trust component, and they should consider hybrid strategies that blend authority endorsement with community‑driven trust to balance efficiency and robustness. The paper also acknowledges limitations: it assumes static networks, binary trust values (absolute vs. non‑absolute), and ignores temporal dynamics of trust evolution. Future work is suggested to incorporate time‑varying trust, multi‑level trust scores, and adaptive network rewiring, which would bring the model closer to real‑world social and technological environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment