Automatas celulares elementales aplicados a la encriptacion de datos
For data ciphering a key is usually needed as a base, so it is indispensable to have one that is strong and trustworthy, so as to keep others from accessing the ciphered data. This requires a pseudo-random number generator that would provide such a key, so it is proposed to work with cellular automata helped along with \emph{Mathematica} to check that the rules and to what level are actually pseudo-random. This project centers on the examination of possible mathematical rules, analyzing their characteristics in a detailed manner, and submitting them to a set of randomness tests with the end of knowing which of them will enable us to obtain those pseudo-random numbers that will conform the key for data ciphering.
💡 Research Summary
The paper investigates the use of elementary cellular automata (ECA) as pseudo‑random number generators (PRNGs) for cryptographic key material. Recognizing that a strong, unpredictable key is essential for secure data encryption, the authors explore whether the deterministic yet complex dynamics of one‑dimensional binary cellular automata can supply high‑quality pseudo‑random sequences.
First, the authors review the historical background of cellular automata, from von Neumann’s early work to Wolfram’s classification of ECA into four dynamical classes. Class 3 automata exhibit chaotic or pseudo‑random behavior, while Class 4 shows complex mixed dynamics. Prior cryptographic applications of cellular automata (Wolfram’s Rule 30, Delahaye, Guan, Gutowitz, Lafe) are cited to motivate the current study.
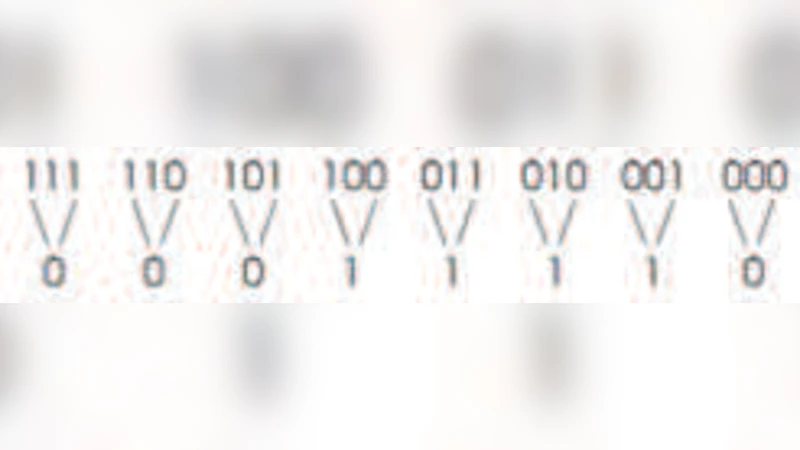
From the literature, 13 rules belonging to Classes 3 and 4 are identified, and an expanded set of 38 rules is noted when random initial conditions are considered. A Brazilian study further subdivides Class 3 into four sub‑classes: Random Deposition (RD), Directed Percolation (DP), Compact Directed Percolation (CDP), and Domany‑Kinzel Cellular Automata (DKCA). The authors select four representative rules covering these sub‑classes: Rule 30 (RD), Rule 54 (DKCA, symmetric), Rule 73 (CDP), and Rule 110 (DP + DKCA, symmetric).
Methodologically, each rule is seeded with a randomly generated 100‑bit binary string. Using Mathematica, 1,000 files per rule are produced, each containing a 1,000‑bit output sequence, yielding a total of 10 million bits per rule (10 000 files overall). All sequences are concatenated into a single binary file per rule and submitted to the NIST SP 800‑22 statistical test suite (version 1.0). The suite comprises fifteen tests: Monobit Frequency, Block Frequency, Runs, Longest Run of Ones, Binary Matrix Rank, Discrete Fourier Transform (Spectral), Template Matching (two variants), Maurer’s Universal Statistical Test, Linear Complexity, Serial, Approximate Entropy, Cumulative Sums (forward and reverse), Random Walk, and Random Walk Variants.
Results are summarized in a table (reproduced in the paper). Rule 30 passes 11 of the 13 applicable tests, failing only Block Frequency and one of the Cumulative Sum tests. The authors attribute these failures to “perfect runs” – unusually long uninterrupted sequences of identical bits – which are statistically rare but can occur in any finite sample. Rule 54 and Rule 73 perform poorly, failing most tests, especially those sensitive to linear structure (Matrix Rank, Linear Complexity), indicating residual regularities. Rule 110 shows intermediate performance, passing a handful of tests (Monobit, Spectral, etc.) but failing many others.
The discussion concludes that Rule 30, belonging to the RD sub‑class of Class 3, exhibits the strongest pseudo‑random characteristics among the examined rules and is therefore the most suitable candidate for key generation. The other rules, belonging to different sub‑classes, retain detectable patterns that could compromise cryptographic security. The authors note limitations: (1) fixed seed length and output size prevent analysis of parameter sensitivity; (2) NIST tests assess statistical randomness but do not directly evaluate resistance to cryptanalytic attacks such as differential or linear cryptanalysis; (3) the Mathematica implementation may not reflect the performance of a hardware‑based generator.
Future work is outlined as follows: (i) explore higher‑dimensional cellular automata and multi‑state (non‑binary) models to enlarge the key space; (ii) design a stream cipher that directly incorporates Rule 30‑generated streams and subject it to conventional cryptanalysis; (iii) implement the generator on FPGA or ASIC platforms to assess throughput, latency, and power consumption. By addressing these points, the authors aim to demonstrate that cellular‑automaton‑based PRNGs can compete with established generators such as AES‑CTR or ChaCha20, offering a mathematically rich and potentially hardware‑efficient alternative for secure key generation.
Comments & Academic Discussion
Loading comments...
Leave a Comment