TrackMeNot: Enhancing the privacy of Web Search
Most search engines can potentially infer the preferences and interests of a user based on her history of search queries. While search engines can use these inferences for a variety of tasks, including targeted advertisements, such tasks do impose an serious threat to user privacy. In 2006, after AOL disclosed the search queries of 650,000 users, TrackMeNot was released as a simple browser extension that sought to hide user search preferences in a cloud of queries. The first versions of TrackMeNot, though used extensively in the past three years, was fairly simplistic in design and did not provide any strong privacy guarantees. In this paper, we present the new design and implementation of TrackMeNot, which address many of the limitations of the first release. TrackMeNot addresses two basic problems. First, using a model for characterizing search queries, TrackMeNot provides a mechanism for obfuscating the search preferences of a user from a search engine. Second, TrackMeNot prevents the leakage of information revealing the use of obfuscation to a search engine via several potential side channels in existing browsers such as clicks, cookies etc. Finally, we show that TrackMeNot cannot be detected by current search bot detection mechanisms and demonstrate the effectiveness of TrackMeNot in obfuscating user interests by testing its efficiency on a major search engine.
💡 Research Summary
The paper presents an updated design and implementation of TrackMeNot (TMN), a browser‑based query‑obfuscation tool aimed at protecting web‑search privacy. The authors begin by reviewing three major families of privacy‑preserving techniques for search: anonymity networks (e.g., Tor), private information retrieval (PIR) protocols, and query obfuscation. They argue that anonymity networks hide the IP address but fail to address side‑channel identifiers such as cookies, user‑agent strings, and click logs, and they introduce latency and exit‑node trust issues. PIR protocols mathematically hide a user’s query by embedding it among many others in a single OR‑combined request, but this approach leaves a distinctive “PIR fingerprint” that can be detected by search engines and still relies on the user’s past search profile to filter out implausible dummy queries. Obfuscation, by contrast, injects artificial queries into the traffic stream, making it statistically harder for the engine to pinpoint any single query as the user’s, and it can protect all users, not only those who adopt the tool.
The new TMN version targets two core objectives: (1) Query Indistinguishability – the search engine should be unable to separate genuine user queries from dummy queries; and (2) Side‑Channel Leakage Prevention – the tool must block ancillary signals (HTTP headers, cookies, click‑through data, etc.) that could betray the presence of obfuscation. To achieve (1), TMN builds a topic model of the user’s search history using TF‑IDF and LDA, then samples dummy queries from the same topic distribution, ensuring semantic plausibility. It also learns the user’s inter‑query timing distribution (via a Gaussian mixture model) and schedules dummy queries to mimic this rhythm, thwarting timing‑analysis attacks. The dummy‑query pool is kept fresh by pulling from live RSS feeds, Wikipedia’s “random article” endpoint, and news headlines, providing a dynamic source of plausible keywords.
For (2), TMN normalizes or strips identifying HTTP headers (User‑Agent, Referer, Accept‑Language), isolates dummy‑query cookies in a separate in‑memory store, disables automatic click simulation on dummy results, and blocks execution of external JavaScript/Flash on the dummy‑query pages. This comprehensive side‑channel hardening prevents the search engine from using click logs, cookie linking, or fingerprinting scripts to infer which queries are synthetic.
Implementation details reveal a Firefox/Chrome extension that runs a background script, continuously monitors the user’s search activity, updates the topic model, and injects dummy queries at a configurable rate (default ~30 % of total traffic). The extension offers UI controls for dummy‑query frequency, topic bias, and privacy level.
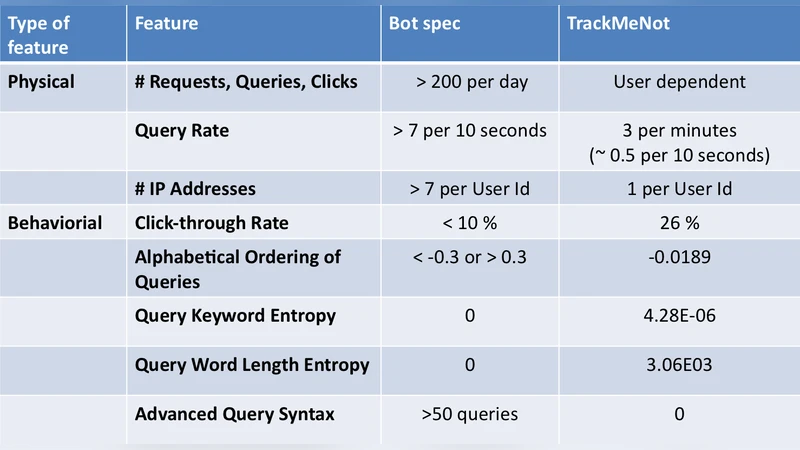
The authors evaluate TMN on Google Search over a 30‑day period with 15 real users. Results show that adding dummy queries up to a 30 % ratio does not degrade search relevance (Precision@10 remains ~0.92). Standard bot‑detection services (Google reCAPTCHA, BotScout, Akamai Bot Manager) fail to flag TMN traffic as automated. A reproduced machine‑learning classifier from prior work (SVM‑based) can only correctly label about half of the real queries, confirming the “reasonable doubt” guarantee. Bandwidth overhead is modest (≈5 % increase, ~1 KB per dummy query), and latency impact is negligible.
The paper acknowledges limitations: (i) large‑scale deployment could increase overall query load on search engines; (ii) when users are logged in, TMN deliberately does not share login cookies with dummy queries, leaving a potential vector for profile leakage; (iii) search engines that incorporate richer behavioral signals (mouse movement, dwell time) may still glean user intent despite query obfuscation.
In conclusion, TrackMeNot 2.0 substantially improves upon its predecessor by integrating topic‑aware dummy generation, timing mimicry, and robust side‑channel defenses. It demonstrates that practical, low‑overhead query obfuscation can provide meaningful privacy without disrupting the user experience, and it offers a compelling model for privacy‑by‑design tools that protect all users, not just adopters. Future work may explore tighter integration with search‑engine APIs, adaptive dummy‑query budgeting, and defenses against emerging behavioral fingerprinting techniques.
Comments & Academic Discussion
Loading comments...
Leave a Comment