An Adaptive Technique using Advanced Encryption Standard to Implement Hard Disk Security
The main objective of the paper is to study and develop an efficient method for Hard Disk Drive(HDD) Security using Full Disk Encryption (FDE) with Advanced Encryption Standards(AES) for data security specifically for Personal Computers(PCS) and Laptops . The focus of this work is to authenticate and protect the content of HDD from illegal use. The paper proposes an adaptive methods for protecting a HDD based on FDE. The proposed method is labeled as DiskTrust. FDE encrypts entire content or a single volume on your disk. DiskTrust implements Symmetric key cryptography with, Advanced Encryption Standards. Finally, the applicability of these methodologies for HDD security will be evaluated on a set of data files with different key sizes.
💡 Research Summary
The paper presents “DiskTrust,” an adaptive full‑disk encryption technique that leverages the Advanced Encryption Standard (AES) to protect data stored on personal computers and laptops while addressing the performance and cost drawbacks of traditional full‑disk encryption (FDE). Rather than encrypting the entire hard‑disk, DiskTrust creates a hidden volume that is invisible to unauthorized users. This volume is encrypted with symmetric‑key AES (supporting 128‑, 192‑, and 256‑bit keys) and is accessed only after successful password authentication. The authors first review existing FDE solutions such as TrueCrypt, DriveEncrypt, and R‑Crypto, highlighting their licensing models, platform support, and cryptographic foundations. They then discuss symmetric versus asymmetric encryption, focusing on AES’s block size, round structure, and key‑size dependent security properties.
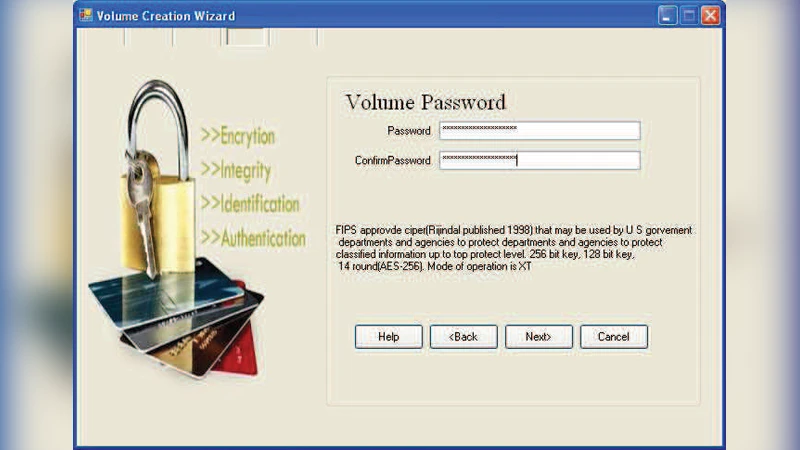
Implementation details are described through a graphical user interface that allows users to (1) create a hidden volume by selecting a file and specifying its size, (2) set and confirm a password that is transformed into an AES key via a key‑derivation function, and (3) mount or dismount the volume. When mounted, the operating system treats the hidden file as a virtual disk; all read/write operations are automatically encrypted or decrypted in real time. The authors evaluated the prototype on a Pentium V 2.4 GHz laptop using test files ranging from 321 KB to 7.13 MB. Four performance metrics were collected: encryption time, CPU processing time, CPU clock cycles, and battery power consumption. Results show a clear correlation between key length and resource usage: moving from a 128‑bit to a 192‑bit key increased power consumption and execution time by roughly 8 %, while a 256‑bit key caused about a 16 % increase. Measured encryption times were 287 ms (AES‑128), 310 ms (AES‑192), and 330 ms (AES‑256).
The authors argue that DiskTrust satisfies the CIA triad—confidentiality through AES encryption, integrity via password‑based authentication and volume‑mount verification, and availability by limiting encryption overhead to the hidden volume only. Because the hidden volume does not appear in standard file‑system listings, it is resistant to casual discovery, reducing the attack surface compared with full‑disk encryption. The paper concludes that DiskTrust offers a cost‑effective alternative to encrypting entire disks, delivering comparable security with lower initial setup time and computational load. However, the authors acknowledge open issues such as robust key management, password strength enforcement, and potential detection of hidden volumes through forensic analysis. Future work is suggested in integrating hardware‑based security modules (TPM, Intel SGX), extending the model to multi‑user environments, and exploring cloud‑storage synchronization for encrypted volumes.
Comments & Academic Discussion
Loading comments...
Leave a Comment