Selection of Model in Developing Information Security Criteria for Smart Grid Security System
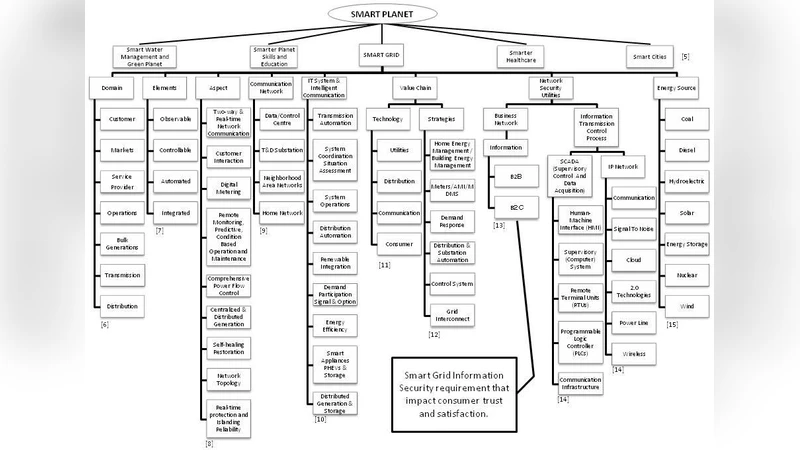
At present, the “Smart Grid” has emerged as one of the best advanced energy supply chains. This paper looks into the security system of smart grid via the smart planet system. The scope focused on information security criteria that impact on consumer trust and satisfaction. The importance of information security criteria is perceived as the main aspect to impact on customer trust throughout the entire smart grid system. On one hand, this paper also focuses on the selection of the model for developing information security criteria on a smart grid.
💡 Research Summary
The paper investigates how information security influences consumer trust and satisfaction within the emerging Smart Grid ecosystem, framing the analysis under the broader “Smart Planet” concept promoted by IBM. Recognizing that the Smart Grid’s two‑way communication and real‑time data exchange dramatically increase cyber‑security vulnerabilities, the authors argue that robust security criteria are essential for maintaining user confidence and the overall success of the grid.
The study proceeds in three logical stages. First, it identifies the need for a systematic method to capture and prioritize security requirements that affect end‑users. Second, it conducts a comparative evaluation of six candidate development models: Quality Function Deployment (QFD), Object‑Oriented (OO), Joint Application Design (JAD), Cleanroom, Structured Analysis and Structured Design (SASD), and Conjoint Analysis (CA). The comparison, presented in Table 1, assesses each model’s focus (e.g., customer‑driven quality, software design flexibility, human communication, error‑free development, user‑specific systems, market forecasting) and its suitability for the Smart Grid context.
The authors conclude that QFD is the most appropriate framework because it directly translates consumer needs into design specifications, employs the House of Quality (HOQ) matrix to prioritize requirements, and emphasizes overall system quality rather than merely technical correctness. While OO offers adaptability and JAD promotes stakeholder communication, these strengths are less critical for the security‑centric goals of the Smart Grid, where stable, well‑defined requirements are paramount. Cleanroom’s emphasis on error‑free code, SASD’s user‑specific focus, and CA’s market‑oriented analysis each miss the core need to align security features with end‑user trust.
QFD’s implementation is described in detail: security requirements are listed as rows, system objectives as columns, and the intersection cells quantify the impact of each requirement on each objective. This visual matrix enables stakeholders to see which security controls most strongly affect trust‑related goals and to allocate resources accordingly.
Recognizing that QFD alone cannot fully address data uncertainty, non‑linear relationships, or precise target‑value determination, the paper proposes three complementary techniques:
-
Fuzzy Logic – translates linguistic assessments (e.g., “high risk”, “moderate impact”) into quantitative scores using IF‑THEN rules, allowing decision‑makers to handle incomplete or ambiguous information.
-
Artificial Neural Networks (ANN) – processes large volumes of input data (sensor logs, incident reports, user surveys) to generate an objective Customer Satisfaction Index, thereby reducing reliance on purely subjective rankings.
-
Taguchi Method – applies robust design principles, orthogonal arrays, and the quality‑loss function to identify optimal parameter settings and to mitigate the effect of uncontrollable noise factors on security performance.
By integrating these methods with QFD, the authors aim to create a more resilient, data‑driven security design process that can both prioritize requirements and specify concrete improvement targets.
The paper concludes that adopting a QFD‑centric approach, reinforced by fuzzy logic, ANN, and Taguchi techniques, can systematically enhance information security in Smart Grids, thereby strengthening consumer trust and satisfaction. However, the authors acknowledge several limitations: the model comparison relies heavily on qualitative description rather than empirical testing; the security criteria themselves are not enumerated in detail; and the assumption of static requirements may not hold in a rapidly evolving grid environment. Future work is suggested to include pilot implementations, dynamic requirement management, and the development of a detailed, actionable security checklist for Smart Grid operators.
Comments & Academic Discussion
Loading comments...
Leave a Comment