Formal Analysis of UMTS Privacy
The ubiquitous presence of mobile communication devices and the continuous development of mo- bile data applications, which results in high level of mobile devices’ activity and exchanged data, often transparent to the user, makes privacy preservation an important feature of mobile telephony systems. We present a formal analysis of the UMTS Authentication and Key Agreement protocol, using the applied pi-calculus and the ProVerif tool. We formally verify the model with respect to privacy properties. We show a linkability attack which makes it possible, for individuals with low-cost equipment, to trace UMTS subscribers. The attack exploits information leaked by poorly designed error messages.
💡 Research Summary
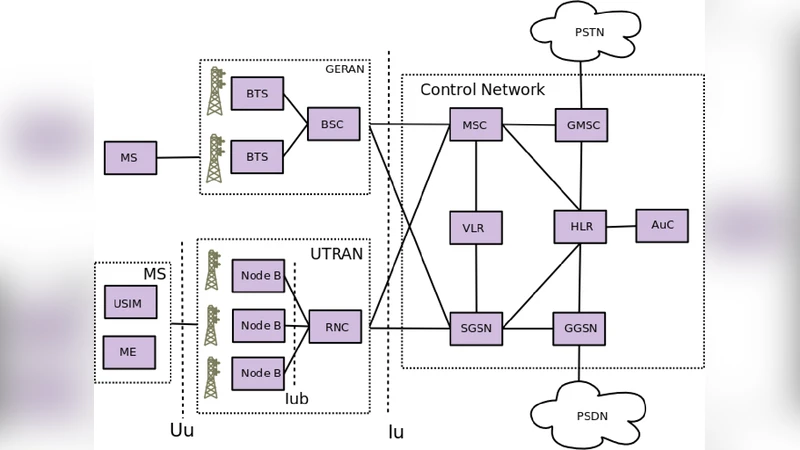
The paper presents a formal security and privacy analysis of the UMTS Authentication and Key Agreement (AKA) protocol, focusing on the often‑overlooked privacy property of subscriber untraceability. Using the applied π‑calculus to model the protocol and the automatic verifier ProVerif to analyze it, the authors build an abstract representation of the AKA exchange between a Mobile Station (MS) and a Serving Network (SN). For tractability, the model abstracts away the XOR‑based symmetric encryption used in the real protocol, allowing the adversary to see both the encryption key and the plaintext. While this over‑approximation would invalidate secrecy proofs, it is conservative for distinguishability properties because the attacker is given strictly more information than in the real world.
The core of the analysis lies in the handling of authentication failure messages. In the standard AKA flow, the Home Network (HN) sends the MS a challenge consisting of RAND and AUTN. The MS verifies the MAC (computed with function f1) and the freshness of the sequence number SQN_HN. If verification succeeds, the MS returns RES = f2_K(RAND). If verification fails, the MS sends one of two distinct error messages: “MAC FAIL” when the MAC check fails, and “SYNC FAIL” (including the current SQN_MS) when the sequence number is out of range. The authors observe that these two error messages leak enough information for an active adversary to distinguish whether a replayed authentication request originated for a particular subscriber.
The attack proceeds as follows: an adversary eavesdrops on a legitimate authentication request (RAND, AUTN) destined for victim MS v, stores it, and later replays it to the network. If the replay reaches MS v, the device processes the request normally and returns a correct RES. If the replay reaches any other device, the MAC verification will fail (or the SQN will be out of range), causing the device to return a “MAC FAIL” or “SYNC FAIL” message. By simply observing which error message is returned, the adversary can decide whether the victim is present, thereby achieving linkability. Because the attack only requires the ability to replay a captured packet and to read the error response, it can be carried out with inexpensive equipment.
The authors encode this scenario in ProVerif. The tool automatically discovers a distinguishing attack on the original protocol model, confirming the feasibility of the linkability exploit. To mitigate the problem, they propose a minimal modification: collapse the two failure messages into a single generic “AUTH FAIL” response that does not reveal whether the failure was due to MAC verification or sequence‑number mismatch, and omit the SQN_MS value from the response. The revised protocol is re‑modelled in ProVerif; the tool no longer finds any distinguishing attack, and a formal proof of unlinkability is obtained under the same over‑approximated assumptions.
The paper also discusses related work, noting that prior analyses of UMTS have focused on GSM‑UMTS interoperability attacks, IMSI‑catcher threats, and authentication weaknesses, but have not addressed privacy properties such as unlinkability. It acknowledges that the abstraction of XOR encryption is a limitation: while acceptable for the privacy property studied, it would be insufficient for secrecy claims. The authors suggest that future work should incorporate a faithful cryptographic model and explore other side‑channel leaks (timing, power consumption) that could undermine privacy.
In summary, the contribution of the paper is threefold: (1) identification of a subtle yet practical linkability attack on UMTS AKA stemming from differentiated error messages; (2) a formal verification of both the attack and its mitigation using applied π‑calculus and ProVerif; and (3) a discussion of the modeling trade‑offs and directions for more comprehensive privacy‑preserving protocol design in mobile networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment