An Implicit Optimization Approach for Survivable Network Design
We consider the problem of designing a network of minimum cost while satisfying a prescribed survivability criterion. The survivability criterion requires that a feasible flow must still exists (i.e. all demands can be satisfied without violating arc capacities) even after the disruption of a subset of the network’s arcs. Specifically, we consider the case in which a disruption (random or malicious) can destroy a subset of the arcs, with the cost of the disruption not to exceed a disruption budget. This problem takes the form of a tri-level, two-player game, in which the network operator designs (or augments) the network, then the attacker launches a disruption that destroys a subset of arcs, and then the network operator attempts to find a feasible flow over the residual network. We first show how this can be modeled as a two-stage stochastic program from the network operator’s perspective, with each of the exponential number of potential attacks considered as a disruption scenario. We then reformulate this problem, via a Benders decomposition, to consider the recourse decisions implicitly, greatly reducing the number of variables but at the expense of an exponential increase in the number of constraints. We next develop a cut-generation based algorithm. Rather than \emph{explicitly} considering each disruption scenario to identify these Benders cuts, however, we develop a bi-level program and corresponding separation algorithm that enables us to \emph{implicitly} evaluate the exponential set of disruption scenarios. Our computational results demonstrate the efficacy of this approach.
💡 Research Summary
The paper addresses the design of minimum‑cost networks that remain feasible under any arc disruption whose total disruption cost does not exceed a given budget Γ. This survivability requirement is modeled as a three‑level game: (1) the network operator decides which candidate arcs to build or augment (binary variables x), (2) an adversary selects a set of arcs to destroy (binary variables d) subject to rᵀd ≤ Γ, and (3) the operator routes flow (variables f) and may shed a fraction γ of demand if necessary. The third‑level problem minimizes a large penalty pγ to enforce feasibility; a zero penalty indicates that all demand can be satisfied after the disruption.
Directly enumerating every feasible disruption scenario leads to an “extensive form” (EF) mixed‑integer linear program whose size grows as O(|E|·S), where S is the number of possible attack sets (exponential in |E|). Solving EF with a commercial MILP solver is only possible for tiny instances.
To overcome this combinatorial explosion, the authors apply Benders decomposition. The master problem retains only the design variables x and a single continuous variable θ that represents the worst‑case operating cost across all attacks. For each scenario, the recourse (flow) subproblem is dualized, yielding Benders cuts that bound θ from below. However, generating cuts by explicitly iterating over all scenarios would defeat the purpose of decomposition.
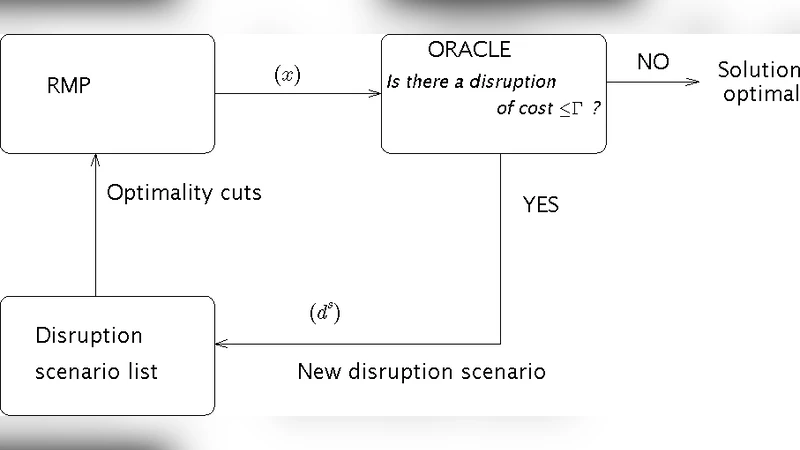
The key contribution is an “implicit optimization” cut‑generation scheme. Instead of enumerating scenarios, the authors formulate a bilevel separation problem that, given a current design x, finds the most damaging attack d* (i.e., the one that maximizes the penalty pγ). This separation problem can be solved as a single mixed‑integer program because the lower‑level flow problem’s dual variables appear linearly in the upper‑level objective. The optimal attack d* produces a new Benders cut, which is added to the master. The algorithm iterates: solve the master, solve the separation problem, add the cut, and repeat until no violating attack exists. Because each iteration only requires solving one MILP (the separation problem) plus the master (a relatively small MILP), the method implicitly evaluates the exponential attack set.
Computational experiments on benchmark power‑grid, transportation, and randomly generated networks demonstrate dramatic speedups. While the EF formulation often fails to finish within reasonable time or runs out of memory, the implicit Benders approach solves instances with dozens of nodes and hundreds of arcs in minutes, even when the disruption budget allows many simultaneous attacks. The resulting designs intuitively reinforce critical links and allocate redundancy where the adversary’s cost to disrupt is low.
The paper also discusses limitations. The dual‑based cuts can become numerous, potentially stressing memory for very large networks. The adversary model assumes total loss of capacity on disrupted arcs, which may be overly conservative for stochastic failure scenarios. Finally, the study focuses on a single‑commodity flow; extending to multi‑commodity or multi‑period settings would require more sophisticated cut structures.
Overall, the work provides a novel, scalable framework for survivable network design by embedding a worst‑case interdiction problem within a Benders decomposition and solving the resulting exponential scenario set implicitly. This advances both the theory of tri‑level optimization and the practical ability to protect critical infrastructure against intelligent attacks.
Comments & Academic Discussion
Loading comments...
Leave a Comment