Cooperative Secret Key Generation from Phase Estimation in Narrowband Fading Channels
By exploiting multipath fading channels as a source of common randomness, physical layer (PHY) based key generation protocols allow two terminals with correlated observations to generate secret keys with information-theoretical security. The state of…
Authors: Qian Wang, Kaihe Xu, Kui Ren
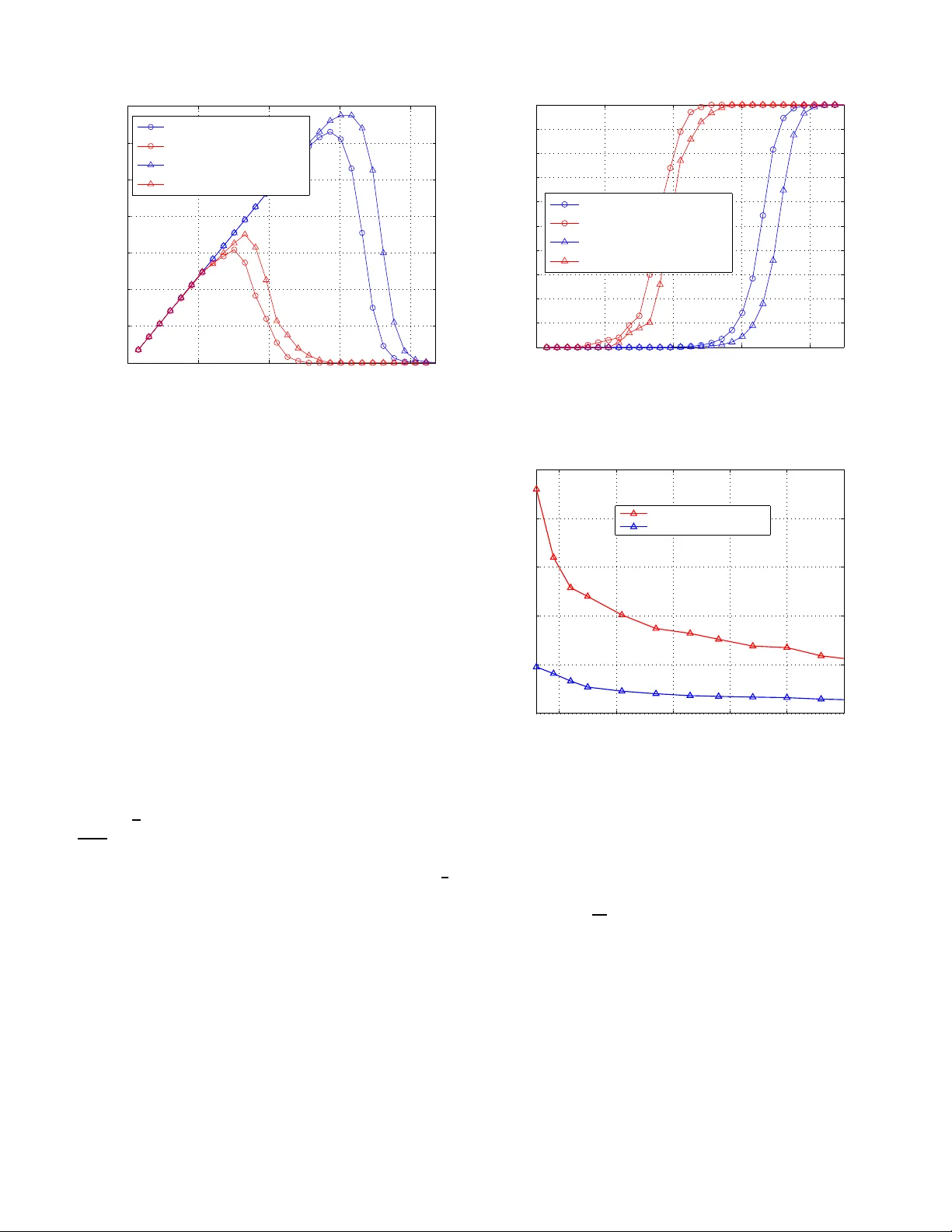
Cooperati v e Secret K e y Generation from Phase Estimation in Nar ro wband F ading Channels Qian W ang, Student Member , IEEE, Kaihe Xu, Stude nt Membe r , IEEE, a nd Kui Re n, Se nior Me mber , IEEE Abstract —By exploiting multipath fading channels as a source of comm on randomness, physical laye r (PHY) based key gener- ation pr otocols allow tw o ter minals with correlated observations to g enerate secr et ke ys with informa tion-theoretical security . The state of the art, howev er , still suffers from major limitations, e.g. , low key generation rate, lower entropy of key bit s and a h igh reliance on node mobil ity . In this paper , a n ov el cooperativ e key generation protocol is d ev eloped to facilitate high-rate key generation in narr owband fading channels, where two keying nodes extract the phase randomness of the fading channel with the aid of re lay node(s). For the fi rst time, we explicitly consider the effect of estimation methods on the extraction of secret key bit s from the und erlying fading channels and focus on a popu lar statistical method–maximum likelihood estimation (MLE). The perfo rmance of the coopera tive key generation scheme is extensively ev aluated theor etically . W e successfully establish both a th eoretica l upper bound on the maximum secret key ra te fro m mutual in fo rmation o f corr elated random sources and a more practical up per bound f rom Cramer - Rao bound (CRB) in estimation theory . Numerical exa mples and simul ation studies are also presented to demonstrate the perfo rmance of the cooperativ e key generation system. The results show th at the key rate can b e i mpro ved by a couple of orders of magnitude compared to the existing approac hes. Index T erms —Key generation, co operativ e networking, multi- path channel, single-tone estimation, maximum likelihood esti- mation, wireless network. I . I N T RO D U C T I O N A fundam ental problem of all wireless co mmunicatio ns is the secu re distrib ution o f secret keys, which m ust be generated and shared between autho rized par ties pr ior to the start of comm unication . In th e field o f cryptog raphy , the Diffie-Hellman key exchange p rotocol is on e o f the most basic and widely u sed cryptog raphic p rotocols for secure key establishment. The essential idea beh ind the Diffie-Hellman key exchange is that: two parties that h av e n o pr ior kn owledge of e ach o ther to join tly establish a shared secret key over an in secure commun ication ch annel. Howe ver , the pr otocol assumes the adversary has bounded co mputation power and relies upon co mputation al hardness of certain math ematical problem s to achiev e secure key gen eration. This body of cryptog raphic protocols achieve computational security . Recently , th e notion of phy sical layer (PHY) based key generation has been prop osed and the resulting ap proache s serve as alternative solutions to the key establishmen t prob lem The researc h of Kui Ren i s partial ly supported by the US Nat ional Science Founda tion under grants CNS-0831963 and CNS-1117811. Qian W ang, Kaihe Xu, and Kui Ren are with the Department of Electrica l and Computer Engineering, Illinois Institute of T echnology , 3301 South Dearborn Street, Suite 103 Siege l Hall, Chicago, IL, 60616 USA. E-mail: { qian, kai, kren } @e ce.iit.edu . in wireless networks. Based on the theory of reciprocity of antenn as and electromagnetic propag ation, the channel responses b etween two tran scei vers can b e u sed as a sou rce of common rand omness th at is not av ailable to adversaries in other locations. Such source of secrecy , which is provided by the fading pr ocess of wireless chan nels, can he lp to achieve information- theor etical security . This body of work can be traced back to th e origina l info rmation- theoretical form ulation of secure com munication due to [1]. Building on inf ormation theory and following [1], informa tion theorists cha racterized the fun damental bou nds and showed the feasibility o f gen- erating secrets using au xiliary random sources [2], [3], [4]. Howe ver , they are almost a ll based o n theoretical results and do no t p resent explicit construction s. T o the best o f our knowledge, Hershey et al. proposed the first key generatio n scheme based on differential p hase detection in [5]. Using multipath cha nnels as the source of commo n rando mness, recent researches focu s on measur ing a po pular statistic of wireless chann el, i.e. , rece i ved signal strength (RSS), for extracting shared secret b its between no de pairs [6], [7], [8]. It h as been d emonstrated th at these RSS ba sed m ethods ar e feasible on customized 802.11 platfo rms. The s tate of the art, howe ver , still suffers from majo r limitatio ns. First, th e key bit generation rate supported by these ap proach es is very low . This is due to the fact that the PHY based key generation relies on chan nel variations o r nod e m obility to e xtract hig h entropy bits. In the time intervals where channel changes slo wly , only a limited number of key bits can be extracted. T he resulting low key rate significantly limits their practical application gi ven the intermittent conn ectivity in mobile en viron ments. T o in crease the key rate, Zeng et al. pr oposed a key ge neration p rotocol by exploiting mu lti-antenna diversity [9]. But it also lead s to an increase in the complexity of the transceiv ers. Second, the generated raw key bit stre am has low r andomn ess. This is because the d istribution of the RSS m easurements or e stimates is not unifo rm, which results in un equally likely bits after quantization . As crypto graph ic k eys need to b e as rand om as possible so that it is infeasible to repro duce them or pred ict them, it is im portant to ensure high en tropy of th e generated keys. Howe ver , the pr oblem of how to safely and efficiently generate random key b its using chann el ran domness is still open. T o overcome the above limitations, in this paper, we in- vestigate th e pr oblem of coop erative k ey gen eration between two nod es with the a id of third parties, i.e. , relay node s. The introdu ction of the relay nodes is motiv ated by the diversity gain pr ovided by the relay nodes, which can poten tially help to increase the key rate by furn ishing the two nodes addition al correlated randomn ess. T o enhance the le vel of entropy of bit sequences, we p ropo se to exploit the un iformly distributed channel p hase for key gen eration. Specifically , we develop a novel time-slotted coo perative key gen eration scheme by exploiting chann el phase randomn ess under narro wband fading channels. For the first tim e, we explicitly consider the effect of e stimation metho ds on the extraction o f secr et key bits from th e un derlying fading chan nels and focu s on a popu - lar statis tical method–max imum likeliho od estimation (MLE). The main features of th e pr oposed scheme are : i) The key bit gene ration rate is improved by a co uple o f o rders of magnitud e c ompared to RSS b ased ap proach es. T his is due to the h igh-accu racy MLE and the fact that th e ra ndom channels between the relay and the keying nodes ca n be effectiv ely utilized durin g a sing le c oher ence time . That also implies the pro posed scheme can even work in a static environment where chan nels change very slowly; ii) The g enerated b it stream is very clo se to a truly ran dom sequen ce d ue to the use of uniformly distributed ch annel phase for bit generation; iii) It is robust to r elay node compr omise attacks since eac h relay node o nly contributes a small portio n of key bits a nd a small n umber of them can never ob tain the complete g lobal key bit in formatio n even collecti vely . Th e perform ance of t he cooper ati ve key g eneration scheme is exten si vely evaluated theoretically . W e successfully establish bo th a theoretical upper bo und on the maxim um secr et key rate from mu tual informa tion of c orrelated r andom sour ces and a more p ractical upper bo und fr om Cramer-Rao b ound (CRB) in estimation theory . W e also show that the coo perative gain in the key generation is similar to the beamfo rming gain in coop erative networking, i.e. , the resulting gain is lin ear to the num ber of relay nodes. N umerical examp les and simulation studies are also presen ted to demonstra te the p erforma nce o f the cooper ati ve ke y gen eration system. The results sh ow that the key rate can be impr oved by a couple of orders of magnitude compare d to the existing app roaches. The rest of the p aper is organized as follows : Section II gives problem form ulation and intro duces wireless fading channel m odel considered in this paper . Section III discusses related work. Sectio n IV provides the detailed d escription of our prop osed coop erative ke y gen eration sch emes. Section V and VI p resent th e theo retical perf ormance analy sis and sim- ulation studies, respe cti vely . Section VII provide s a security discussion of the propo sed sche me from both pr actical and theoretical aspects. Finally , Section VIII conclu des the paper . I I . P R O B L E M F O R M U L AT I O N A N D P R E L I M I NA R I E S In this section, we first defin e the PHY based key genera- tion pr oblem in wireless network s an d introdu ce the general assumptions mad e in the existing work [6], [7], [ 8], [1 0]. This will e xplain why wireless channel between a tra nsmitter- receiver pair can be used as a s ource of commo n r andomn ess for secret genera tion. T hen we discuss two most common channel models and focus on the narrowband fading chan- nel, wh ich is clo sely related to the key gener ation schem es developed i n this pap er . A. Pr oblem F ormu lation In a multipath fading wireless en vironm ent, the p hysical signals transmitted betwee n a transmitter-receiver pair rapidly decorre late in space, time an d frequen cy . That im plies that it is very hard for a thir d pa rty to p redict the chan nel state between the legitimate parties, i.e. , an eavesdropper at a third locatio n ( e.g. , one half o f wa velength away) c annot observe the same channel respo nse inform ation. This chan nel uniq ueness prop- erty of the transmitter-receiv er pair offers potential security guaran tees. Further , the chann el r ecipr o city ind icates the avail- ability of using co mmon rand omness be tween the transmitter - receiver pair: th e electroma gnetic wa ves traveling in both directions will unde rgo the same p hysical pertu rbations. That implies th at in a time-division duplex (TDD) system , if th e transmitter-receiv er pair op erates on the same f requency in both direction s, the channe l states/chann el impu lse r esponses observed at two ends will theor etically b e the sam e. Based on th ese two ob servations, we can see th at there exists a natural ra ndom so urce in wireless comm unications for secr ecy extraction. Consider two par ties A an d B (we term th em as keying nodes in the following discussion ) that want to establish a symmetrical key b etween them in the pre sence of an eav es- dropp er E . The keying node s are assumed to b e half -duplex in the sense that they can not transmit an d receive sign als at the sam e frequen cy sim ultaneously . I n th e first timeslot, A transmits a sign al x A to B , an d E can also hear this signal over the wireless chan nel. The signals received by B and E are: r B = h AB x A + n B r E = h AE x A + n E , where h AB and h AE are the chann el gains from A to B and A to E , respectively , and n B and n E are noises at B and E , r espectiv ely . In the second timeslot, B transmits a signal x B to A , and E ca n also hear this signal over the wireless channel. The signals re ceiv ed by A and E are: r A = h B A x B + n A r E = h B E x B + n E , where h B A and h B E are the ch annel gains fro m B to A and B to E , respec ti vely , and n A and n E are noises at A and E , respectively . The chann el f rom n ode i to n ode j is m odeled as a mu ltipath fading m odel with channel im pulse h i,j ( t ) . W e as- sume c hannel reciprocity in th e f orward and reverse directions during the cohe r ence time such that h i,j ( t ) = h j,i ( t ) an d th e underly ing n oise in each c hannel is additive white Ga ussian noise (A WGN). I n wireless commu nications, co her ence time is a statistical m easure of the tim e du ration over which the channel im pulse r esponse is essentially inv ariant, and quan ti- fies the similarity of the c hannel respon se at different times. The keying no des A and B comp ute the sufficient statistic ˆ r B and ˆ r A , respecti vely , and gener ate the secret ke y b ased on these o bservations. In our system, we assume there exist N relay no des, which are hon est and will he lp an d coop erate with the keying nod es A and B to gen erate secret keys. On the o ther side, the eav esdropp er E knows the whole key generation protoco l and can eavesdrop all the commu nications between legitimate n odes ( i.e. , A , B an d relay nodes). Based on communicatio n theory [11], the signals transmitted between A an d B and the signals transmitted b etween A ( B ) an d E , which is at least λ/ 2 away from the network nodes, experience indepen dent fading. As an example, consider a wireless system with 900 MHz carrier frequ ency . If an eavesdropper E is more than 16cm aw ay from the commu nicating nod es, it experiences indepen dent channel v ariations such that no useful info rmation is revealed to it. Follo wing the sam e assumptions in most key g eneration schemes [6] , [8], [12], [ 10], we assume that the adversary E aims to deri ve the secret ke y gene rated between legitimate nod es an d fu rther steal the transmitted priv ate info rmation in the future. T hose ac ti ve a ttacks wher e the a ttacker tampers the transmissions are o rthogo nal to ou r research an d thus no t considered in this paper . The above p roblem can b e con sidered as a key gen eration problem in co operative wireless n etworks in the presenc e of an eavesdropper . I n this pap er , we propo se to develop an efficient a nd secure co operative key gener ation proto col and provide an info rmation- theoretic study on maximum key rate using tech niques fr om both information theory and estima tion theory . The p roposed design should satisfy the following requirem ents: i) H igh key rate. Giv en the in termittent con- nectivity in mobile e n vironm ents, the key gen eration scheme should have a high key r ate; ii) Soun d key rando mness. As cryptog raphic keys ne ed to be as random as possible so that it is infeasible to rep rodu ce them or predict them, the resulting key bits should have a h igh level of entropy . No te that the existing sch emes usually r ely on c hannel variations or n ode mobility to extract high entropy bits. W e propo se to remove this constraint and establish random keys e ven in static en vironm ents. B. Narr owband a nd W ideb and F ading Cha nnels An important characteristic of a multipath chann el is the delay spread ν it causes to the signal [11]. If ν is large, the m ultipath compo nents are typically resolvable, leading to the wide band fading chann el, whe re the r esulting pro bability distributions for the gain s of mu ltipath c hannel paths are often modeled as log-n ormal or Naka gami [12]. I f ν is small, the multipath co mpone nts are ty pically nonreso lvable, leading to the narr owband fading ch annel, wher e the am plitude gain is Rayleigh distributed. In this p aper, we will foc us on a narr owband fading system for secret key gene ration. Ou r app roach c an also apply to wideband fading chann els. B ut as will b e shown, it suits best for narr owband fading chann el mo del. Let the transmitted signal be x ( t ) = R { ˜ u ( t ) e j 2 π f c t } , where ˜ u ( t ) is the comp lex envelope of x ( t ) w ith band width B and f c is its carr ier freq uency . Assume th e eq uiv alent lowpass time-varying ch annel impulse respon se is h ( τ , t ) = P N ( t ) n =0 α n ( t ) e − j φ n ( t ) δ ( τ − τ n ( t )) , the received signal can b e written as r ( t ) = x ( t ) ∗ h ( τ , t ) (1) = R ∞ Z −∞ h ( τ , t ) ˜ u ( t − τ ) dx e j 2 π f c t = R N ( t ) X n =0 α n ( t ) e − j φ n ( t ) u ( t − τ n ( t )) e j 2 π f c t , where α n ( t ) is a function of path loss and shadowing while φ n ( t ) depe nds o n delay , Doppler, and carr ier o ffset. T ypically , it is assumed that these two ran dom pr ocesses α n ( t ) and φ n ( t ) ar e indep endent. Note N ( t ) is the numb er of resolvable multipath compon ents. For n arrowband fading chann els, each term in the sum of Eq. (1) results fr om nonresolvable multipath compon ents. Under most delay sprea d characterizatio ns, ν ≪ 1 /B implies that the d elay associated with the k th m ultipath compon ent τ k ≤ ν ∀ k , so u ( t − τ k ) ≈ u ( t ) . I f x ( t ) is assumed to be an unm odulated ca rrier ( single-tone signal) x ( t ) = R { e j 2 π f c t } = co s 2 π f c t , it is narrowband for an y ν . Wi th th ese assumption s, the received signal becom es r ( t ) = R N ( t ) X n =0 α n ( t ) e − j φ n ( t ) e j 2 π f c t (2) = r I ( t ) cos 2 π f c t − r Q ( t ) sin 2 π f c t, where the in-ph ase and quadr ature com ponents ar e given by r I ( t ) = P N ( t ) n =1 α n ( t ) cos φ n ( t ) an d r Q ( t ) = P N ( t ) n =1 α n ( t ) sin φ n ( t ) , respectiv ely . The in-p hase and q uadratu re com- ponen ts of Rayleigh fading process are jointly Gau ssian random pro cess. The complex “lowpass” equivalent signal for r ( t ) is g iv en by r I ( t ) + j r Q ( t ) which has ph ase θ = arctan( r Q ( t ) /r I ( t )) , where θ is un iformly distributed, i.e. , θ ∈ U [0 , 2 π ] . So r I ( t ) + j r Q ( t ) can be written as r I ( t ) + j r Q ( t ) = | h | e j θ = | h | cos θ + j | h | sin θ , where | h | = p r I ( t ) 2 + r Q ( t ) 2 . Consider the additive wh ite Gaussian noise (A WGN) in the ch annel, Eq. ( 2) can b e written as r ( t ) = | h | cos θ cos 2 π f c t − | h | sin θ sin 2 π f c t + n ( t ) (3) = | h | cos(2 π f c t + θ ) + n ( t ) , where n ( t ) is a Gaussian noise pro cess with p ower spectral density N 0 2 . W e will estimate par ameters in r ( t ) an d use the u niformly distributed phase o f mu ltipath chann el for key generation . A list of impor tant notation is shown in T able. I. I I I . R E L AT E D W O R K The PHY b ased key gener ation can be tr aced ba ck to the original informatio n-theor etic formu lation of secu re c ommu- nication due to [1]. Building on info rmation th eory , [2], [3 ], [4] ch aracterized th e fun damental boun ds and showed th e feasibility of generatin g keys using externa l ran dom so urce- channel im pulse respon se. T o the b est o f our knowledge, the first ke y generation scheme suitable f or wireless network w as propo sed in [5]. In [5], the differential ph ase be tween two frequen cy tones is encod ed for key genera tion. Error contro l T ABLE I A S U M M A RY O F I M P O RTA N T N O TA T I O N . Symbol Definitio n p e the bit error probabilit y (BER) T c coheren ce time ν delay s pread q the number of quanti zation i nterv als T o ( T i ) observ ation time or beacon duration time N s the number of samples in the observ ation time N 0 the one-sided power spectra density (PSD) h I j i , h I ij channe l ga ins f s sampling rate N number of relay nodes R M I k ke y rate from mutual information with no relay R C RB k ke y rate from CRB with no relay R M I co coopera ti ve key rate from mutual information R C RB co coopera ti ve key rate from CRB coding techn iques are used fo r en hancing the reliab ility of key gener ation. Similar to [5], a techniq ue of using ra ndom phase for extracting secret keys in an OFDM system throug h channel estimation and quantization was recently proposed in [13]. This p aper characterized the pro bability of gener ating the same bit vector between two nodes as a function of signal-to- interferen ce-and- noise (SINR) an d quan tization lev els. A key g eneration schem e based on extractin g secret bits from cor related deep fades was p roposed in [6] an d dis- tinguished fro m th e afo remention ed work by using receiv ed signal strength ( RSS) as the rand om source via a TDD link for the protocol d esign. T wo cry ptograp hic to ols– info rmation reconciliation an d p riv acy amplification are used to eliminate bit vector discrepancies du e to RSS measurement a symmetry . The fin al key agreemen t is achieved by leaking out mini- mal inf ormation fo r error c orrecting and sacrificing a certain amount of en tropy f or g enerating nearly p erfect r andom secret bits. In [7 ], the au thors proposed tw o k ey generation schem es based on channel impulse response (CIR) estimation and RSS measurem ents. Different from [6], the two transceivers alternately send k nown prob e signa ls to each ano ther an d estimate the magnitu de of chan nel r esponse at successive time instants. The excursions in the fading channe ls are used for generating b its and th e timing of excur sions are used for key reconciliation . The re sulting sequen ce are fu rther filtered and quantized using a 1-bit quan tizer , which r esults in low key bit rate. Motiv ated b y ob servations f rom qu antizing jointly Gaussian process, a more g eneral ke y generation scheme was p roposed by explo iting empirica l measur ements to set quantization bound aries in [10]. W orking on the same RSS based app roach, [8] evaluated the ef fectiveness o f RSS b ased key extractio n in real en vironmen ts. It h as been shown that due to lack of channel variations static environments are not suitable for establishing secure ke ys, and node m obility helps to gener ate k ey bits with high entropy . The most recent work [14] pro posed an efficient an d scalable key genera tion sch eme that sup ports both p airwise and g roup key establishments. Due to noise, interference and other factors in the key g ener- ation process, discrepan cies may exist between the genera ted bit streams. V arian ts of this pr oblem hav e been extensively explored u nder the n ames in formation reconc iliation, p riv acy amplification and fuzzy extractors. [15] proposed the first pro - tocol to so lve the information-th eoretic key ag reement pro blem between tw o parties that initially po sses only correlated weak secrets. Th e key agr eement was shown to be th eoretically feasible when the in formatio n that the two bit strings co ntain about each o ther is mor e than the in formatio n th at the eaves- dropp er has about them. [16] u sed err or-correcting technique s to design a protoco l that is com putationally efficient for different distance metrics. Bas ed on the previous results, [17] propo sed a pro tocol that is efficient f or both parties an d ha s both lower round complexity and lo wer entr opy loss. Recently , [18] p roposed a two roun d key agreement p rotocol for the same settings a s [17]. I V . T H E P R O P O S E D S O L U T I O N S In this section, we present our co operative key gen eration algorithm s for extracting secret bits from wir eless chann els. The proposed algorithms employ the tec hnique of single-tone parameter estimation to estimate the unifo rmly distributed channel phase. When keying node s A and B alternately transmit kn own single- tone signals to e ach othe r , each r elay node also observes the fading signals transmitted throu gh the pairwise lin ks between him an d th e keying nodes. Therefo re, with the aid o f r elay no des, the keying no des A and B c an potentially in crease the key ra te using additiona l random ness in the same co her ence time inter val. A. Utilizing a S ingle Relay W e fist consider the s ingle relay case where o ne r elay n ode acts as a h elper to facilitate the key gener ation between the keying n odes A and B . T he basic idea is that an un modula ted carrier ( i.e. , single- tone sign al) is transm itted throu gh the fading ch annels back and forth betwee n the k eying n odes, an d the keying n odes per form m aximum Likelihood Estimation (MLE) b ased on th eir o bservation. Since each bidirection al channel between a pair of n odes is a time-division-dup lex (TDD) chan nel, which is reciproc al in both dire ctions, it will incur the same total phase shif t caused by multipath d ue to the channel r ecipr ocity principle . Generally , the protoco l consists of two main phases: i) Sing le-tone phase estimation and quantization ; ii) K ey reconciliation and priv acy amplification. Before we intr oduce the coo perative ke y gener ation pro to- col, we first intro duce the fundam ental building block– MLE used in single-to ne signal parameter estimations. Du ring the protoco l execution, the keying nod es A , B an d relay n odes use MLE to estimate the par ameters of a single-tone sign al with a known sign al model. Gi ven cer tain ob servation set Z and parameter set α , the o bjective of MLE is to estimate the parameter set that m aximizes the pdf of Z . In our ap plication, the received signal model can be wr itten as r ( t ) = b 0 cos( ω 0 t + θ 0 ) + n ( t ) , (4) where α = { b 0 , ω 0 , θ 0 } are the un known parameter s (a mpli- tude, frequ ency and phase, respectively) to be estimated. T he received signal is sampled at a constan t sampling freque ncy rate f s = 1 /T s to pr oduce the d iscrete-time observation r [ m ] = b 0 cos( w 0 ( t 0 + mT s ) + θ 0 ) + n [ m ] (5) Key ing node A Key ing node B 1 Relay node R 1 ( ) x t 1 ( ) x t 1 Genera te ( ) x t 1 TS : Receive ( ) AB r t 1 Receive ( ) AR r t l Estimate , AB AB Z T l 1 1 Estimate , AR AR Z T Key ing node A Key ing node B 1 Relay node R 2 ( ) x t 1 ( ) x t 2 Generate ( ) x t 2 TS : Receive ( ) BA r t 1 Receive ( ) BR r t l Estimate , B A BA Z T l 1 1 Estimate , B R BR Z T 2 ( ) x t Key ing node A Key ing node B 1 Relay node R 3 ( ) x t 3 Generate ( ) x t 3 TS : 1 Receive ( ) R A r t 1 Receive ( ) R B r t l 1 1 Estimate , R A R A Z T l 1 1 Estimate , R B R B Z T 3 ( ) x t Quantize AB T 1 Quantize AR T Quantize B A T 1 Quantize B R T 1 Quantize R A T 1 Quantize R B T Key ing node A Key ing node B 1 Relay node R 2 |K| After rounds: 2log q 2 3 Compute K K Compute 2 3 K K 2 3 K K 3 2 2 3 ( ) K K K K 1 2 ( , ) K K 1 3 ( , ) K K Compute 2 3 2 3 ( ) K K K K Fig. 1. Protocol for cooperat i ve k ey generation with one relay . for m = 0 , 1 , . . . , N s − 1 . Here, t 0 denotes the time of the first sample and n [ m ] s ar e Gaussian random samples with zero mean and variance σ 2 . Let Z = ( r [0 ] , r [1 ] , . . . , r [ N s − 1]) , the pdf of Z is [ 19] f ( Z ; α ) = 1 σ √ 2 π N s exp ( − 1 2 σ 2 N s − 1 X m =0 ( r [ m ] − µ [ m ]) 2 ) , where µ [ m ] = b 0 cos( w 0 ( t 0 + mT s ) + θ 0 ) . In the following discussion, we ign ore discussion o n the estimation of signa l amplitude b 0 since its estimation is independ ent f rom th e estimation of freque ncy and phase. The N s samples in Eq. (5) is provid ed as an input of the MLE estimator . Accordin g to the results in [19], the m aximum of fun ction f ( Z , α ) is achieved whe n θ 0 = − tan − 1 P N s − 1 m =0 r [ m ] sin( ω m ) P N s − 1 m =0 r [ m ] cos( ω m ) . (6) Thus, we can first estimate the frequ ency of the signal, and then calculate the ML estimate of the phase using Eq. (6). Specifically , the MLE is imp lemented in thr ee steps: 1) R ough frequency sear ch. W e calcu late the Discrete-time Fourier Transformation (DFT) of Z and find the ˆ k = arg ma x k | R [ ω k ] | , whe re ω k = 2 kπ N T s and N is th e leng th of the DFT . Here, N is chosen to be a power o f 2 and greater than N s . Then we can calculate the roughly esti- mated frequ ency as ω l = 2 ˆ kπ N T . Such frequ ency estimate has large estimation err or due to the li mited re solution of the DFT . Thus, a more accu rate estimation is desire d; 2) Fine f r equency searc h. Based on the rough estimation in the last step, we can calculate the ˆ ω by max imizing fu nc- tion | R ( ω ) | , w here R ( ω ) is the continu ous DFT of the sample sequen ce r [ m ] in th e interval [ 2( ˆ k − 1) π N s T , 2( ˆ k +1) π N T s ] . The fine search algorithm locates the value of ω clo sest to ω l that maximize s | R ( ω ) | . The seca nt method is used to comp ute su ccessi ve approx imations to the frequen cy estimate ˆ ω = arg ma x ω | R ( ω ) | . 3) P hase estimation. The p hase estimate can be calculated by substitutin g ˆ ω to Eq. ( 6). The perf ormanc e of MLE is m easured by th e variance of the estimation errors. This variance can be lower -boun ded by the Cramer-Rao b ound (CRB) [20]. The perfo rmance o f the ML estimator, which is closely related to the p erforma nce o f the propo sed co operative key gener ation scheme, will be discussed and analyzed later . W e present the cooper ati ve key generation protoco l as follows (See Fig. 1): Phase O ne: Single -tone phase estimatio n and quantizatio n . TS 1 : The protoc ol begins in timeslot 1 with transmission of a sinusoidal pr imary beacon of duratio n T 1 from n ode A : x 1 ( t ) = a 1 cos( w c ( t − t 1 )) , where t ∈ [ t 1 , t 1 + T 1 ) . T o simplify th e exposition, we assume t 1 = 0 in the following discussion, i.e. , the p rotocol starts at time zero p oint. Node B ( R 1 ) observes the initial transient r esponse of the multipath channel h A,B ( t ) ( h A,R 1 ( t ) ) to the beacon x 1 ( t ) over the in terval t ∈ [ τ AB , τ AB + ν AB ) ( t ∈ [ τ AR 1 , τ AR 1 + ν AR 1 ) ), where τ AB ( τ AR 1 ) deno tes the de lay of the shor test path and ν AB ( ν AR 1 ) d enotes the fin ite dela y spr ead of the c hannel h A,B ( t ) ( h A,R 1 ( t ) ). In order to ac hiev e a steady-state response at both B and R 1 , it is required that T 1 > max { ν AB , ν AR 1 } . The “steady-state” portion of the bea cons r eceiv ed at B and R 1 can be written as A t B : r AB ( t ) = a 1 α AB cos( w c t + θ AB ) + n AB ( t ) , A t R 1 : r AR 1 ( t ) = a 1 α AR 1 cos( w c t + θ AR 1 ) + n AR 1 ( t ) , where t ∈ [ τ AB + ν AB , τ AB + T 1 ) ( t ∈ [ τ AR 1 + ν AR 1 , τ AR 1 + T 1 ) ) for B ( R 1 ), an d n AB ( t ) ( n AR 1 ( t ) ) d enotes the ad ditiv e white Gau ssian noise (A WGN) in th e A → B ( A → R 1 ) channel. α AB ( α AR 1 ) and θ AB ( θ AR 1 ) ar e the steady- state gain an d th e p hase respo nse o f ch annel h A,B ( t ) ( h A,R 1 ( t ) ), respectively . At the end of primary beacon , a final tr ansient response of the multipath chan nel is also received by B ( R 1 ) over the interval t ∈ [ τ AB + T 1 , τ AB + ν AB + T 1 ) ( t ∈ [ τ AR 1 + T 1 , τ AR 1 + ν AR 1 + T 1 ) ). B ( R 1 ) uses only the steady-state portion of the n oisy obser vation to compute ML estimates o f the r eceiv ed frequency an d p hase, wh ich are deno ted by ˆ w AB ( ˆ w AR 1 ) an d ˆ θ AB ( ˆ θ AR 1 ), r espectiv ely . TS 2 : Up on the conclusion of the primary beacon r AB ( t ) , in timeslot 2, B begins the transmission of a sinusoidal secondary beacon at t 2 = max { τ AB + ν AB + T 1 , τ AR 1 + ν AR 1 + T 1 } . The second ary beacon transm itted by B at t 2 can be written as x 2 ( t ) = a 2 cos( w c ( t − t 2 )) , where t ∈ [ t 2 , t 2 + T 2 ) . A ( R 1 ) ob serves th e initial transient response of the multipath chann el h B ,A ( t ) ( h B ,R 1 ( t ) ) to beacon x 2 ( t ) over the inter val t ∈ [ t 2 + τ B A , t 2 + τ B A + ν B A ) ( t ∈ [ t 2 + τ B R 1 , t 2 + τ B R 1 + ν B R 1 ) ), where ν B A = ν AB ( ν B R 1 = ν R 1 B ) due to c hannel reciproc ity . In order to achieve a steady -state response at b oth A and R 1 , T 2 > max { ν B A , ν B R 1 } is requir ed. The steady- state portion of the beacons received at B an d R 1 can be written as A t A : r B A ( t ) = a 2 α B A cos( w c t + θ B A ) + n B A ( t ) , A t R 1 : r B R 1 ( t ) = a 2 α B R 1 cos( w c t + θ B R 1 ) + n B R 1 ( t ) , where t ∈ [ t 2 + τ B A + ν B A , t 2 + τ B A + T 2 ) ( t ∈ [ t 2 + τ B R 1 + ν B R 1 , t 2 + τ B R 1 + T 2 ) ) fo r A ( R 1 ), and n B A ( t ) ( n B R 1 ( t ) ) denotes the additive wh ite Gaussian n oise (A WGN) in the B → A ( B → R 1 ) chann el. α B A ( α B R 1 ) and θ B A ( θ B R 1 ) are th e steady-state gain and the phase r esponse of channel h B ,A ( t ) ( h B ,R 1 ( t ) ), respe cti vely . At the e nd of this beac on, a final transient response of the multipath chann el is r eceived by A ( R 1 ) over th e inter val t ∈ [ t 2 + τ B A + T 2 , t 2 + τ B A + T 2 + ν B A ) ( t ∈ [ t 2 + τ B R 1 + T 2 , t 2 + τ B R 1 + T 2 + ν B R 1 ) ). Similar to TS 1 , A ( R 1 ) uses only the steady-state por tion of the noisy ob servation to com pute ML estimates of the r eceiv ed frequen cy a nd phase, which are denoted by ˆ w B A ( ˆ w B R 1 ) and ˆ θ B A ( ˆ θ B R 1 ), r espectiv ely . TS 3 : Upon the con clusion o f the prim ary beac on r B R 1 ( t ) , in tim eslot 3 R 1 begins the transmission o f a sinusoidal secondary b eacon at t 3 = max { t 2 + τ B A + ν B A + T 2 , t 2 + τ B R 1 + ν B R 1 + T 2 } . T he third beacon tran smitted by R 1 at t 3 can be written as x 3 ( t ) = a 3 cos( w c ( t − t 3 )) , where t ∈ [ t 3 , t 3 + T 3 ) . A ( B ) observes the initial tra nsient response of the m ultipath chann el h R 1 ,A ( t ) ( h R 1 ,B ( t ) ) to beacon x 3 ( t ) over the interval t ∈ [ t 3 + τ R 1 A , t 3 + τ R 1 A + ν R 1 A ) ( t ∈ [ t 3 + τ R 1 B , t 2 + τ R 1 B + ν R 1 B ) ), where ν R 1 A = ν AR 1 ( ν R 1 B = ν B R 1 ) due to c hannel reciproc ity . In order to achieve a steady-state respon se at both A and B , T 3 > max { ν R 1 A , ν R 1 B } is required. T he stead y-state po rtion o f th e beacons received at A an d B can be written as A t A : r R 1 A ( t ) = a 3 α R 1 A cos( w c t + θ R 1 A ) + n R 1 A ( t ) , A t B : r R 1 B ( t ) = a 3 α R 1 B cos( w c t + θ R 1 B ) + n R 1 B ( t ) , where t ∈ [ t 3 + τ R 1 A + ν R 1 A , t 3 + τ R 1 A + T 3 ) ( t ∈ [ t 3 + τ R 1 B + ν R 1 B , t 3 + τ R 1 B + T 3 ) ) for A ( B ) , and n R 1 A ( t ) ( n R 1 B ( t ) ) denotes the additive wh ite Gaussian n oise (A WGN) in the R 1 → A ( R 1 → B ) channel. α R 1 A ( α R 1 B ) an d θ R 1 A ( θ R 1 B ) are th e steady-state gain and the phase r esponse of channel h R 1 ,A ( t ) ( h R 1 ,B ( t ) ), respectively . At th e end of this bea con, a final transient response of the multipath chann el is r eceived by A ( B ) over the interval t ∈ [ t 3 + τ R 1 A + T 3 , t 3 + τ R 1 A + T 3 + ν R 1 A ) ( t ∈ [ t 3 + τ R 1 B + T 3 , t 3 + τ R 1 B + T 3 + ν R 1 B ) ). Similar to TS 2 , A ( B ) uses only the steady-state por tion of the noisy ob servation to com pute ML estimates of the r eceiv ed frequen cy and ph ase, which a re denoted b y ˆ w R 1 A ( ˆ w R 1 B ) and ˆ θ R 1 A ( ˆ θ R 1 B ), r espectiv ely . Quantization . T o genera te high-entro py b its, we assume A , B and R 1 run the above steps once d uring each coherence time interval. For ease of e xposition, we term th e above steps as round 1 . After roun d 1, each of the three nod es ha s two phase estimates for qu antization A : ˆ θ B A mod 2 π , ˆ θ R 1 A mod 2 π B : ˆ θ AB mod 2 π , ˆ θ R 1 B mod 2 π R 1 : ˆ θ AR 1 mod 2 π , ˆ θ B R 1 mod 2 π Each node unifo rmly map s their phase estimates into th e quantization interval/index using the fo llowing formula: Q ( x ) = k if x ∈ [ 2 π ( k − 1 ) q , 2 π k q ) for k = 1 , 2 , . . . , q . Therefo re, in th e first ro und, the quan - tization of each phase value gener ates log 2 ( q ) secr et bits. Due to channel rec iprocity princip le, A and B share lo g 2 ( q ) bits gen erated from ˆ θ B A ( ˆ θ AB ); A and R 1 share log 2 ( q ) bits generated from ˆ θ R 1 A ( ˆ θ AR 1 ); B an d R 1 share log 2 ( q ) bits generated from ˆ θ R 1 B ( ˆ θ B R 1 ). Note the q uantization in dex k is encoded into bit vectors. In o ur implementatio n, we use gray codes to reduc e the bit err or probab ility (BER). Assume the desired key size is | K | . For round k = 2 , 3 , . . . , | K | 2 log 2 ( q ) , A , B an d R 1 repeat the op erations as in TS 1 , TS 2 and TS 3 to gener ate ph ase estimates and conv ert them into bit vectors thro ugh q -level quantization. After | K | 2 log 2 ( q ) round s, a key o f size | K | 2 is shared between A and B , which is deno ted a s K 1 . Sim ilarly , a key of size | K | 2 is shared between A and R 1 , which is den oted as K 2 ; a key of size | K | 2 is sha red between B and R 1 , which is deno ted as K 3 . Then R 1 computes K 2 ⊕ K 3 and transmits it over the public channel. A receives th e XOR inform ation and computes K 2 ⊕ ( K 2 ⊕ K 3 ) = K 3 . Similarly , B obtains K 2 by K 3 ⊕ ( K 2 ⊕ K 3 ) = K 2 . Now bo th A an d B have keys K 1 , K 2 and K 3 . Finally , A and B set the final key as K 1 || K 2 or K 1 || K 3 , and a secret key with size | K | is established. Note that we use either K 2 or K 3 instead of b oth as the comp onent of the final key . The rea son is th at with e ither one of K 2 and K 3 the eav esdropp er c an recover the other one by lev eraging K 2 ⊕ K 3 . Phase T wo: Key reconciliation a nd privacy amplification . Due to recip rocity pr inciple, the gene rated bit sequ ence at A and B sho uld be id entical. Howe ver , there may exist a small number o f bit discrepancie s due to estimation errors, h ardware variations an d half-du plex beacon transmission. These e rror bits can be corrected u sing key reconciliatio n techniques [17], [21]. Assume A and B hold K an d K ′ , resp ectiv ely . And the Hamming distance dis ( K , K ′ ) ≤ t . Following Code-o ffset construction in [ 21], we use a [ n, k , 2 t + 1] 2 error-correcting code C to correct err ors in K ′ ev en thoug h K ′ may no t be in C . When perfor ming key r econciliation , node A r andom ly selects a codeword c from C and co mputes secure sketch SS ( K ) = s = K ⊕ c . Th en s is sen t to no de B . Upon receiving s , node B subtracts the shift s fro m K ′ and gets Rec ( K ′ , s ) = c ′ = K ′ ⊕ s . The n node B dec odes c ′ to get c , and co mputes K b y shifting back to get K = c ⊕ s . Note that since the error-corre cting information s is pu blic to both the co mmunicatin g no des and the adversary , it can be used by the adversary to gue ss portions of the gen erated key [ 8]. T o cop e with this pro blem, A and B can further run priv acy amplification pro tocols [17] to recover the entropy loss. B. Ex ploiting Multiple Rela ys In this su bsection, we present the key gen eration p rotocol with mu ltiple relay nodes. As d iscussed above, when ther e exists on ly o ne relay R 1 , he can contribute lo g 2 q bits in each coherence time interval. Since the beaco n d uration (observa- tion tim e) T i is relativ ely small compa red to the coher ence time , a large p ortion of the coherence time interval can not be effectively utilized. Th is mo tiv ates us to incorpo rate more relays into the key gener ation pr ocess with potential two advantages: i) the key rate is further increased due to multiple relays’ con tribution du ring the same coherence time interval. This also implies that even if the no des o r the environment remain static, a key with hig h entropy can be generated quickly since it em ploys the ran domness of multiple different pairwise links; ii) th e security streng th is fur ther e nhanced as each relay on ly co ntributes a small portion of secret b its to the final key . That im plies, even if a small numbe r of relays are compro mised, the a dversary can never obtain the com plete global key bit inf ormation . W ith the aid of N relay no des, the protocol has a total of N + 2 timeslots for each r ound (durin g one co her ence time interval T c ). Assume the coh erence time a re ro ughly d ivided to N + 2 po rtions, each with length T c N +2 . The activities in each timeslot of round 1 are as follo ws (for ease of e xposition, we ignore the explicit value of t i for i = 1 , 2 , . . . , N + 2 ): 1) I n TS 1 , node A tran smits a sinusoid al pr imary bea con x 1 ( t ) . No de B ( R j , j = { 1 , 2 , . . . , N } ) n eglects the initial and final transient portion s of the received sig nal and u ses the steady p ortion to co mpute th e channel p hase estimates ˆ θ AB ( ˆ θ AR k ). 2) I n TS 2 , node B tran smits a s inusoidal secondar y b eacon x 2 ( t ) . Node A ( R j , j = { 1 , 2 , . . . , N } ) n eglects the initial and final transient portion s of the received sig nal and u ses the steady p ortion to co mpute th e channel p hase estimates ˆ θ B A ( ˆ θ B R j ). 3) I n TS i ( i = { 3 , 4 , . . . , N + 2 } ), n ode R k ( j = { 1 , 2 , . . . , N } ) altern ately tran smits a sinusoidal beacon x i ( t ) . Nodes A an d B neglect the initial and final transient portions of the recei ved sig nal and use the steady portion to compu te the ch annel phase estimates ˆ θ R j A ( ˆ θ R j B ) fo r j = { 1 , 2 , . . . , N } . Assume the d esired key size is | K | . For round k = 2 , 3 , . . . , | K | ( N +1) log 2 ( q ) , A , B and R 1 repeat the operatio ns as in TS 1 , TS 2 , . . . , TS N +2 to gener ate phase estima tes and con vert them into bit vectors th rough q -level quantization. After | K | ( N +1) log 2 ( q ) round s, a key o f size | K | N +1 is shared between A and B , which is deno ted as K 1 . Similarly , a key of size | K | N +1 is sha red between A and R j ( j = { 1 , 2 , . . . , N } ) , which is deno ted as K j 1 ; a key of size | K | N +1 is shared be tween B and R j ( j = { 1 , 2 , . . . , N } ) , which is denoted as K j 2 . Then R j computes K j 1 ⊕ K j 2 and tran smits it over th e p ublic channel. A receives the XOR info rmation and computes K j 1 ⊕ ( K j 1 ⊕ K j 2 ) = K j 2 . Similarly , B ob tains K j 1 by K j 2 ⊕ ( K j 1 ⊕ K j 2 ) = K j 1 . Now both A and B have 2 N + 1 keys K 1 , K j 1 and K j 2 for j = { 1 , 2 , . . . , N } . Finally , A and B set the final ke y as K 1 || ( K 11 or K 12 ) || ( K 21 or K 22 ) || · · · || ( K N 1 or K N 2 ) . The key reconciliation and privacy amplificatio n ph ase is the same as the single relay case. Note th at since a single coherence time inter val is e venly a llocated to th e ke ying nodes and relay no des, the increase of N resu lts in the decrease of available observation time T o (beacon duratio n T i ). As will be shown later, this would lead to the increase of estimation errors in ML E. T herefor e, there must exist an optimal max imum N under which key rate is maximized . V . T H E O R E T I C A L P E R F O R M A N C E A N A LY S I S In th is sectio n, we ana lyze the perfo rmance of th e coop- erative key generation protoco l in terms of the m aximum key rate the system can ach iev e. I n informatio n theory , the mutual infor mation of two rando m variables/sequen ces is a quantity tha t mea sures the mutual depend ence o f the two variables/sequences. Th erefore, the secr et key rate can be upper boun ded by the mutual information between the obser- vations of two transceivers. Motiv ated by this, we first pr ovide an info rmation-th eoretic study in to the upper bo und on the key rate using mu tual info rmation. This b ound den otes the maximum key rate th at can be g enerated from the commo n random ness between the keying no des. In estimatio n theory , Cramer-Rao bound p rovides a lower b ound on the variance o f biased and u nbiased estimator s of a determ inistic p arameter . Since we utilize m aximum likelihood estimatio n (MLE) in our propo sed key gener ation pro tocol, we also pro pose to d eriv e a tighter bo und o n the key rate u sing the Crame r-Rao bound (CRB). A. Kno wing the Limit: The Up per Bound on K ey Rate fr om Mutual In formation In this su bsection, we an alyze the mu tual informa tion b e- tween the observations of two nodes i and j at two en ds of a multipath fadin g cha nnel. W e start the an alysis f rom the no - relay case. As shown ab ove, all the received signals can be expressed a s Eq. ( 4). These single-ton e signals can be precisely reconstruc ted from samples taken at samp ling rate g reater or equal at Ny quist rate f s = 1 T s = 2 f c (Note in th e following analysis, we cho ose f s ≫ 2 f c ). The d iscrete-time observation at no des i and j ar e r ij [ m ] = aα ij cos( w c ( t ij + mT s ) + θ ij ) + n ij [ m ] (7) r j i [ m ] = aα j i cos( w c ( t j i + mT s ) + θ j i ) + n j i [ m ] (8) for m = 0 , 1 , . . . , N s − 1 , where t ij ( t j i ) deno tes the time of the first sample. Note that when th ere is no relay , nodes A and B each can gener ate N s samples by fu lly exploiting the coherence time interval. That is, if we neglect the transmission delay , d elay spread and p rocessing delay , the observ ation time ( i.e. , beacon du ration) is T o ≈ T c 2 . Th us, N s = T o f s = T c f s 2 . Let R ij = [ r ij [0] , r ij [1] , . . . , r ij [ N s − 1 ]] and R j i = [ r j i [0] , r j i [1] , . . . , r j i [ N s − 1]] denote the sam ples ob- tained at no des j an d i , r espectively . Acco rding to [12], I ( r ij ( t ); r j i ( t )) = I ( R ij ; R j i ) as r ( t ) is fu lly defined by R . In prac tice, given a set X of in depend ent identica lly dis- tributed data conditioned on an unkn own param eter θ , a sufficient statistic is a f unction T ( X ) whose value contains all the infor mation n eeded to compu te any estimate of th e parameter (e.g. a maximum likelihood estimate (MLE)). For ease of exposition, we r ewrite Eq. (4) her e r ( t ) = | h | cos θ cos 2 π f c t − | h | sin θ sin 2 π f c t + n ( t ) = | h | cos(2 π f c t + θ ) + n ( t ) . In MLE estimation, | h | co s(2 π f c t + θ ) + n ( t ) is sampled to estimate | h | an d θ , w here th e com plex expression of mu ltipath channel is h = | h | e j θ . Once | h | and θ are obtained , the terms | h | cos θ co s 2 π f c t and | h | sin θ sin 2 π f c t are both determined. So it is equivalent to sample and estima te a signal like | h | cos θ co s 2 π f c t or | h | sin θ s in 2 π f c t to fully deter mine the fading chan nel in formatio n. The “equi valent” r eceiv ed signa ls at no des i and j can be written as r ij [ m ] = aα ij cos θ cos( w c ( t ij + mT s )) + n ij [ m ] r j i [ m ] = aα j i cos θ cos( w c ( t j i + mT s )) + n j i [ m ] for m = 0 , 1 , . . . , N s − 1 . Because r [ m ] is fully defined b y r [ m ] and vic e versa, the mutual inform ation between r ij [ m ] and r j i [ m ] is the same as th at between r ij [ m ] and r j i [ m ] , i.e. , I ( R ij ; R j i ) = I ( R ij ; R j i ) , wher e R ij and R j i are th e discrete-time sequ ences of r ij [ m ] and r j i [ m ] , resp ectiv ely . Now the problem becomes a Gaussion random vari- able estimation p roblem, where the in-phase c ompon ent r I ( t ) = | h | co s θ = α cos θ is to b e estimated ( in the following, we abuse stand ard notation by letting h I denote the in-p hase comp onent) . Let S i = S j = [ a cos( w c (0 T s )) , a cos( w c (1 T s )) , . . . , a cos( w c ( mT s ))] . Both nodes i and j can co mpute a sufficient statistic b R j i and b R ij for R j i and R ij respectively [22 ] b R j i = S T j || S j || 2 R j i = h I j i + S T j || S j || 2 N i (9) b R ij = S T i || S i || 2 R ij = h I ij + S T i || S i || 2 N j (10) where || S j || 2 = S T j · S j and || S i || 2 = S T i · S i . Theorem 1: Let h I j i , h I ij ∼ N (0 , σ 2 h ) and N i , N j ∼ N (0 , σ 2 ) . Based on sufficient statistics ( b R j i , b R ij ) at two ends, nodes i and j can generate secret key bits at rate R M I k = ln 2 T c log 2 (1 + σ 4 h N 2 s P 2 σ 4 + 2 σ 2 σ 2 h N s P ) , where P den otes the transmission p ower , N s denotes the number of samples and T c is the coherence time . Pr o of: See Append ix A. In the a bove discussions, we focus o n two nodes i an d j with no relay nod e. W e next analyze the key rate when th ere are N relay nodes. If the samplin g r ate f s is fixed, the coherence time T c which contains 2 N s samples is d ivided into N + 2 shares. From the nodes A and B ’ s point of view , they e ach “sends” 2 N s N +2 samples. T hus, the cooperative key gener ate rate is R M I co = ( N + 1) ln 2 T c log 2 [1 + σ 4 h ( 2 N s N +2 ) 2 P 2 σ 4 + 2 σ 2 σ 2 h ( 2 N s N +2 ) P ] (11) Although the mutual in formatio n between ea ch n ode pairs decreases d ue to the r eduction of numb er of sam ples, the relay nodes help A and B to establish more key comp onents, this gain becomes mor e significant when SNR increases o r th e channel chan ges very s lowly . W e have the following theorem Theorem 2: When there are N rela y nodes, the cooperative gain is lim P →∞ R M I co R M I s = N + 1 (12) lim N s →∞ R M I co R M I s = N + 1 , (13) where R M I s = R M I k . As we can see, the gain of coopera ti ve key gen eration is similar to the beamfo rming gain in co operative networking , which is lin ear to the nu mber of relay node s. B. A Mor e Practical Bou nd: The Upper Bound on K e y Rate fr om Cramer -Rao bound (CRB) In th e last subsectio n, we derive a theo retical uppe r bound on key rate from m utual info rmation. This bou nd serves as a universal b ound in th e sen se that it does not depend on th e specific m ethod of estimation , and it is not tight in gener al. Therefo re, we next compute a more practical and tighter bound on key rate fro m Crame r-Rao b ound (CRB) in estimation theory . In the existing RSS based key gener ation m ethods, the signal en velops ar e sampled and q uantized for the calculation of secre t bits. By u sing the signal envelop, there exists a trade- off betwee n the reduction of the sensitivity of the system to timing error and the loss of v ariability in the resulting key [12]. Different from that, in this paper , we use the unifor mly distributed channel ph ase for key gen eration to achie ve a high lev el of en tropy . O ne of the most imp ortant proper ties of Maximum Likelihood estimators ( MLE) is that it attains the Cramer-Rao bou nd at least a symptotically . Similarly , startin g from the no-re lay case, we have the following theorem: Theorem 3: When maxim um likelihood estimation (MLE) and un iform quan tization are used, the expected ke y rate is upper-boun ded by R C RB k = P QI A log 2 q T c , where P QI A is the av erage prob ability o f quantization index agreemen t. Pr o of: See Append ix B. 0 0.0012 0.0024 0.0035 0.0047 0.0059 0.0071 1300 1400 1500 1600 1700 1800 1900 Observation time T o (s) Upper bounds on key rate (bits/s) R k CRB , SNR = 20 dB, q = 16 R k CRB , SNR = 25 dB, q = 16 R k CRB , SNR = 30 dB, q = 16 R k MI , SNR = 20 dB, q = 16 R k MI , SNR = 25 dB, q = 16 R k MI , SNR = 30 dB, q = 16 Fig. 2. Ke y rate versus observat ion time T o under differe nt SNRs. When th ere are N relay nod es, the numb er of samples at each node is N co s = 2 N s N +2 . W e substitute N s for N co s in Eq. ( 24) and obtain the new CRB f or ˜ θ . T his b ound is used to calculate P co QI A . T hus, the expected key rate for coop erative key generation becomes R C RB co = ( N + 1) P co QI A log 2 q T c . (14) It is easy to see that as q increases, node i and j could generate a longer bit v ector during th e same coherence time T c . Howe ver , du e to estimation errors the probab ility of gener ating the same bit vector b ecomes less. W e can d erive the maximum key agreement rate whe n q satisfies ∂ R C RB co ∂ q = 0 . (15) From th e a bove discussion, we conclude that there exists an optimal q at which m aximum key rate can be ac hieved. W e demonstra te ho w key rate changes as a fun ction of q through simulations in Section VI. C. Nu merical Illustration on Th eor etical Upper Bo unds Assume co her ence time T c = 1 4 ms . Th e example in Fig. 2 presents the t wo upper b ounds on key rate be tween two nodes ( i.e. , no relay) as the observ ation time T o increases. The results show th at th e upp er bound derived from mu tual informatio n serves as the uni versal up per bo und o n ke y ra te. As expected , with a fixed number o f qu antization levels, th e incr ease of SNR or T o leads to the increase of key ra te. Since ther e are only tw o n odes, the observation time for each node can be up to 7 ms. When T o changes f rom 0 to 2.4 ms, key rate increases rapidly , and it increases almost linearly as a function of T o after 2.4ms. Hence, a less observation tim e can be pro perly chosen to still maintain an accep table level o f key rate. On the other hand, while the maximum T o is constrained by T c / 2 , one can fur ther enhance the key rate by in creasing SNR. Fig. 3 plots the upper bounds on ke y rate when the number of relays N in creases. The close match of the bound from 1 500 1000 1500 2000 2500 3000 3500 4000 4500 0 0.5 1 1.5 2 2.5 3 3.5 4 4.5 5 x 10 6 Number of relays N Upper bounds on key rate (bits/s) R co MI , SNR = 25 dB R co CRB , SNR = 25 dB Fig. 3. ke y ra te v ersus the number of re lays N . Note tha t the observa tion time T o is not fixed, i.e. , T o decrea ses a s N increases. T ABLE II S I M U L AT I O N C O N FI G U R A T I O N Carrier frequency f c 900 MHz Sampling frequen cy f s 2.7 GHz A verage moving speed v 10 m /s Coherenc e time T c 14 ms Node distance d 2 m – 10 m Delay spread ν 1.2 µ s mutual informatio n and the bou nd fro m CRB before N = 500 shows that, the CR B can b e used to ef ficiently a pproach the un iv ersal uppe r boun d wh en the nod es u se ML ph ase estimation. Recall that as N increases, the ob servation time T o for each node de creases because the whole coher en ce time are equ ally distributed to the keying nodes a nd relay nod es. Due to the fact that the decr ease o f T o causes more estimation errors, there exists a threshold on key rate. Th is ca n be clearly observed from the results: th e bo und based on CRB gradually achieves the maximu m an d decreases after N = 25 00 . For the sake of clearly illustrating the inflectio n poin t on the boun d curve fro m CRB, we limit th e range of N in the figu re. In fact, there also exists a inflection p oint on th e bo und curve from mutu al informa tion when N goes to infinity . Discussion . In o ur pro tocol, the keying nodes re ly on a common time refe rence to generate absolu te phase estimates. If there exists no c ommon time reference amo ng the nodes, each n ode h as to co unt o n its own local time obtained from its local oscillator . This im plies that the phase estimate gener ated by each n ode will ha s an “u nknown” of fset associated with th e node itself, which prevents the key gen eration proto col from working co rrectly . As a futu re direction, it is worth while to extend o ur protocol to overcome the effect of unkn own p hase offsets and allow ke y gener ation in the unsync hronized case. W e are also g oing to build a simple prototy pe to validate the effecti veness of the p rotocol. The no des can be implemen ted by TMS32 0C6713 DSKs boar ds, and the prima ry b eacons can be generated and sent out by a fu nction g enerator, e.g. , HP33120 A. In th e imple mentation, we can use phase- locked 10 0 10 2 10 4 10 6 10 8 0 200 400 600 800 1000 1200 1400 Number of quantization levels q key rate (bits/s) R k CRB , SNR = 25 dB, T o = 7.5 µ s R k SIM , SNR = 25 dB, T o = 7.5 µ s R k CRB , SNR = 30 dB, T o = 7.5 µ s R k SIM , SNR = 30 dB, T o = 7.5 µ s Fig. 4. Ke y rate versus the number of quantiz ation le vels q . loops (PLLs) to realize p hase and f requency estimation func- tions for im proving the efficiency . Since each n ode transmits a perio dic extension of a b eacon received in a previous timeslot, the phase and frequency estimation functions during the synchr onization timeslots can be realized by using phase- locked loops (PLLs) with h oldover circuits, i.e. , the PLLs are required for eac h no de to store its loca l p hase an d freq uency estimates du ring protoc ol execution. V I . S I M U L AT I O N S T U D I E S A. Ke y Rate an d Bit E rr or Pr obability This section pr esents simu lation results of the coop erativ e key gen eration pr otocol in multipath fading channels. In o ur simulation, we sample the beac on signa l with sam pling ra te f s = 3 f c , wh ere f c = 900 M Hz is the carrier frequen cy of the sing le-tone signal. I n a mobile scenario, we assume the moving speed v = 10 m/s. Thus, the Dop pler freq uency sh ift is f d = v λ = 30 Hz, whic h results in a coher ence time T c = 0 . 423 f d = 14 m s. Assume ν is the delay spr ead with a typ ical value 1 . 2 × 10 − 6 s and the d istance d b etween nodes ch anges from 2m to 1 0m. Thus, the random propag ation delay τ = d c = 6 . 67 ns ∼ 33 . 3 ns. W e c hoose T o much la rger than the delay spread ν so that steady- state response can be achieved. T he simulation settings a re summariz ed in T able II. T wo different methods are used here to estima te the variance of the ph ase estimation error : (i) full ML estimation and (ii) ap proxim ate analytical pr edictions using CRB. The first exam ple considers the e ffect of quantization level q on ke y rate. Fig. 4 plots the ke y rate versus q giv en SNR = 25dB and T o = 7.5 µ s using both the CRB analytical prediction s and si mulation s. The results show tw o regimes of operation . In the small-quantization level r egime, the ef fect of log 2 q dominate s th e key rate. In this regime, the pr obability that two estimates fall into the same interval P QI A is very high. T hus, the increa se of q leads to the increase of key rate. According to Eq. (15), wh en q begins to exceed a threshold , 10 0 10 2 10 4 10 6 10 8 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 Number of quantization levels q Bit error probability p e CRB, SNR = 25 dB, T o = 7.5 µ s SIM, SNR = 25 dB, T o = 7.5 µ s CRB, SNR = 30 dB, T o = 7.5 µ s SIM, SNR = 30 dB, T o = 7.5 µ s Fig. 5. Bit probabili ty erro r p e versus the number of quanti zation lev els q . 0.3 0.5 1 1.5 2 2.5 3 x 10 −5 0 0.5 1 1.5 2 2.5 x 10 −3 Observation time T o (s) Bit error probability p e SIM, SNR = 25 dB, q = 16 CRB, SNR = 25 dB, q = 16 Fig. 6. Bit error probabili ty p e versus observa tion time T o . the key r ate b egins to decrease and enters into the large- quantization level regime . In this regime, the key rate decreases quickly as q furth er increases. T his is due to th e fact that the estimation error s dom inate the pe rforman ce as the length of ea ch inter val 2 π q decreases, i.e. , P QI A is very sensitive to the estimatio n error s when the length of inter val is small. As might be expected, th e CR B can b e u sed to efficiently pred ict the perfor mance when q is relatively sm all, e.g. , q < 10 3 in this setting. Since CRB is a lower bound on the variance of the estimation er ror, it takes a much larger q to r each the inflexion point compared to th e simulation results. The above result intuitively suggests that an o ptimal q can be cho sen to maximize the key r ate. T o ev aluate the BER perfor mance, Fig. 5 plots the b it erro r prob ability between two nodes as a function of q . T he results s how that, with a fixed T o = 7 . 5 µ s, p e can be maintain ed at a very low lev el if q < 100 . W e can use Gray codes (on e b it of er ror is intro duced between adjacent sectors) to encode the quan tization indices to reduce 1 2 3 4 5 6 7 8 500 1000 1500 2000 2500 3000 Number of Relays N Key rate (bit/s) R k SIM , SNR = 10 dB, T o = 11 µ s, q = 16 R k SIM , SNR = 25 dB, T o = 11 µ s, q = 16 R k SIM , SNR = 40 dB, T o = 11 µ s, q = 16 Fig. 7. Ke y rate versus the number of relays N . p e . Also n ote that in these results, the coheren ce time is not fully exploited ( i.e. , the observation time T o = 7 . 5 µ s ≪ T c ), so on e can also reduce p e so as to increase key rate b y setting a larger T o . Fig. 6 plots bit error probab ility p e as a function of observation time T o under SNR = 25 d B and q = 16 . The results sho w that th e increase o f T o is equi valent to the increase of SNR, wh ich results in a close match of simu lation results and CRB. Fig. 7 plots the key rate of the coo perative key generation pro tocol a s the n umber of relay no des increases when the quantizatio n levels is fixed at q = 16 . W e ch oose T o = 11 µ s to main tain a high level of estimatio n accuracy . The results show that key r ate increases linear ly as a function of N , which confirms our previous analysis that the gain of cooper ati ve key ge neration scales with the numb er o f relays. As a final p oint on the r esults, we n ote that the f urther increase of SNR ( e.g. , from 25 dB to 4 0 dB) does not help mu ch to improve the per forman ce. T his is beca use the estimation accuracy is already high en ough when choo sing a short q and a reaso nable value of T o . B. Ke y Rand omness and The E ffect of Mobility As we discussed above, the propo sed cooperative key gen- eration scheme employs the in herent ra ndomn ess of u niformly distributed ch annel phases in m ultipath narrowband fading channels. W e employ a widely u sed ran domness test suite NIST to verify the rand omness of the secret-bit ge nerated from o ur simu lation [ 23]. T o pass the test, all p-values m ust be greater than 0 . 01 . In the te st, we ran domly select 10 b it sequences g enerated from ou r simulation and compute their p-values f or 8 tests. The re sults in T able III show that the av erage en tropy o f ou r ge nerated bit seq uences is very clo se to a truly ran dom sequence . V I I . S E C U R I T Y A N A L Y S I S In this section, we pr ovide a security discussion fo r the propo sed co operative key gener ation scheme. W e focus on TEST P − v alue A vg DFT 0.6039 Lempel Z i v Comp. 0 .4453 Monobit F req. 0.5547 Runs 0.4045 Approximate Entropy 0.5869 Cumu. Sums (Forward) 0.5951 Cumu. Sums (Rev erse) 0.5887 Block Frequenc y 0.5732 Serial 0.5732, 0.5091 T ABLE III R E S U LT S O F N I S T. both practical and analytical aspects. Th e secur ity o f th e propo sed key g eneration sch eme is g uaranteed b ased on the assumption that the adversary is not located ne ar the legitimate parties, i.e. , A , B an d other relay no des. The is due to the spatial dec orrelation fact: sinc e the sign al dec orrelates over a distance of app roximately on e half length [11], it is almost impossible fo r an adversar y which is lo cated at a different place with the transceivers to obtain the iden tical c hannel response f or key gen eration. That is, an entity wh ich is at least λ/ 2 aw ay from the network nodes experiences fading channels to th e nod es are statis tically independent of the channels between the comm unicating no des. As an example, consider a wire less system with 900MHz carr ier f requen cy . If the adversary is more than 1 6cm away from the co mmunicatin g nodes, it e xperien ces in depend ent channel v ariations such that no useful info rmation is revealed to it. By passively observing th e signa ls transmitted between legitimate nodes, it has been empir ically shown in [10] that the eavesdropper cannot o btain any significan t inform ation abo ut the signals received at legitimate nodes. Another key po int regarding the secu rity aspect is that we rely o n th e un iformity o f th e chan nel phase for extracting secret key bits in the nar rowband fadin g ch annels. As dis- cussed in Section I I-B, th e com plex lowpass equiv alent signa l for r ( t ) can be written as r LP = r I ( t ) + j r Q ( t ) , where the phase of r ( t ) is θ = arcta n( r Q ( t ) r I ( t ) ) . For un correlated Gaussian ra ndom variables r I ( t ) an d r Q ( t ) , it can be shown that θ is u niform ly distributed over [0 , 2 π ] [11]. Consequently , our prop osed PHY b ased key gene ration algo rithm is best suited for the narrowband fading channels, where r ( t ) has a Rayleigh-distributed am plitude an d unifo rm ph ase. W e have the following theorem: Theorem 4: The cooper ati ve ke y gen eration scheme is se- cure, i.e. , the resu lting secr et key is effecti vely concealed from the eavesdropper observing the p ublic info rmation: 1 N + 1 I ( M 0 , M 1 , M 2 , . . . , M N ; K AB , K 11 , K 21 , . . . , K N 1 ) ≤ ǫ Pr o of: See Append ix C. V I I I . C O N C L U S I O N In this paper, a novel coo perative key gener ation p rotocol was d ev eloped to facilitate high -rate ke y generatio n in nar- rowband fading c hannels, where two ke ying nodes extract the phase rando mness of the fading channel with the aid of relay node(s). For the first time, we explicitly considered the ef fect of estimation m ethods on th e extraction of secre t key bits from the und erlying fading channels and focu sed on a pop ular sta- tistical m ethod–m aximum likelihood estimation (MLE). The perfor mance of the coo perative key generation scheme was e x- tensiv ely ev aluated theoretically . W e successfu lly established both a theoretical upper bound on the maximum secret key rate from mutua l in formatio n of cor related rando m sou rces and a more p ractical upper bou nd from Cramer-Rao bou nd (CRB) in estimation theory . Numerica l examples and simulation stud ies were a lso pre sented to demo nstrate the perfo rmance of the cooper ati ve ke y gen eration system. The results sh ow that the key rate can be impr oved by a couple of orders of magnitude compare d to the existing app roaches. A P P E N D I X A P R O O F O F T H E O R E M 1 Pr o of: From the above d iscussion, it is easy to see that b R ij is a zer o mean Gaussian random variable with variance σ 2 h + σ 2 || S i || 2 . Similarly , b R j i is a ze ro mean Ga ussian rand om variable with variance σ 2 h + σ 2 || S j || 2 . Assume that nodes i and j transmit with power P = a 2 2 . W e have || S i || 2 = || S j || 2 ≈ P N s . Obviously , ( b R ij , b R j i ) retains all the comm on random ness in ( R ij ; R j i ) . Thu s, the m utual inform ation I ( r ij ( t ); r j i ( t )) = I ( R ij ; R j i ) (16) = I ( b R ij ; b R j i ) . The mutual in formation I ( b R ij ; b R j i ) can be co mputed as follows I ( b R ij ; b R j i ) = H ( b R ij ) + H ( b R j i ) − H ( b R ij , b R j i ) (17) = ln 2 2 log 2 2 π e ( σ 2 h + σ 2 P N s ) + ln 2 2 log 2 2 π e ( σ 2 h + σ 2 P N s ) − H ( b R ij , b R j i ) = ln 2 log 2 2 π e ( σ 2 h + σ 2 P N s ) − H ( b R ij , b R j i ) . Obviously , b R ij and b R j i form a multivariate n ormal distri- bution, thus H ( b R ij , b R j i ) = ln 2 2 log 2 [(2 π e ) 2 det (Σ)] , (18 ) where Σ is the covariance matrix of vector h b R ij , b R j i i T , i.e. , Σ = " σ 2 h + σ 2 P N s Cov ( b R ij , b R j i ) Cov ( b R ij , b R j i ) σ 2 h + σ 2 P N s # . (19) The covariance of b R ij , b R j i is calc ulated by Cov ( b R ij , b R j i ) = E ( b R ij b R j i ) − E [ b R ij ] E [ b R j i ] (20) = E " ( h I ij + S T j || S j || 2 N i )( h I j i + S T i || S i || 2 N j ) # = E [ h 2 ij ] = σ 2 h . And det (Σ) is the determ inant of Σ , which is compu ted by det (Σ) = ( σ 2 h + σ 2 P N s ) 2 − σ 4 h (21) = 2 σ 2 h σ 2 P N s + σ 4 P 2 N 2 s . Thus, the mutual inf ormation between n odes i an d j is I ( b R ij ; b R j i ) = ln 2 log 2 (1 + σ 4 h N 2 s P 2 σ 4 + 2 σ 2 σ 2 h N s P ) . (2 2) Assume the coherence time is T c , the maximum key rate is R M I k = 1 T c I ( b R ij ; b R j i ) (23) = ln 2 T c log 2 (1 + σ 4 h N 2 s P 2 σ 4 + 2 σ 2 σ 2 h N s P ) , where the sup erscript M I in R M I k denotes that th e key rate is derived as an u pper bou nd from mutu al information. A P P E N D I X B P R O O F O F T H E O R E M 2 Pr o of: T o facilitate an alysis, we assum e that when the number of samples increases by u sing larger o bservation time, the estima tion e rrors converge to zero-mean Gaussian r andom variables with variances σ 2 ˜ θ , which can be lo wer-bounded by th e Cramer-Rao b ound s (CRB) [ 20]. Fig. 8 plo ts both the distribution of the MLE errors using simulation and the CRB results. The simu lation results sho w that variance of t he estimation errors σ S I M σ 2 ˜ θ = 1 . 687 7 · 10 − 6 is lower -bou nded by the CRB σ C RB σ 2 ˜ θ = 1 . 561 6 · 10 − 6 . When estimating the unknown ph ase o f a sampled sinu soid of amplitude a in wh ite noise with Power Sp ectral Den sity (PSD) N 0 2 , th e CRB f or the variance of the p hase estimate is given as σ 2 ˜ θ ≥ 4 f s σ 2 (2 N s − 1) a 2 N s ( N s + 1 ) ≈ 4 N o a 2 T o ≈ 4 N 0 f s a 2 N s , (24) where f s is the sampling r ate, N s is the numb er of samples in the observation, an d T o is the observation time ( i.e . , beacon duration ) in secon d. T he approx imations can be o btained by assuming that N s is large and the fact that N s /f s = T o = T c 2 . Consider Eq. (8), we assume a r = aα is the received signal strength (we neglect th e sub script i, j for simplicity). The a mplitude response of th e fading ch annel α is Ray leigh distributed, and E [ α 2 ] = 2 σ 2 h , then a 2 r = 2 σ 2 h a 2 . Hen ce, the CRB b ound fo r the received signal can be expressed a s a function of SNR and N s σ 2 ˜ θ ≥ 4 SNR N s , (25) where SNR = a 2 r 2 N 0 f s = 2 σ 2 h P σ 2 . (26) Suppose [0 , 2 π ] is divided into q = 2 n lev els. Now we analyze the probability that n odes i an d j ’ s estimations fall into the same interval when performin g quantizatio n. Let P QI A denote the av erage pro bability of qu antization ind ex −6 −4 −2 0 2 4 6 x 10 −3 0 50 100 150 200 250 300 350 Phase estimation error of MLE Pdf of ML estimation errors MLE Simulation CRB SNR = 25dB T o = 3 µ s Fig. 8. T he comparison of ML estimat ion error dist ributi on using simulat ion and CRB. agreemen t. W ithout loss of ge nerality , assume that θ falls into th e i -th sector [ 2 π i q , 2 π ( i +1) q ) ( i ∈ { 0 , 1 , · · · , q − 1 } ) . As phase estimation errors are independen t and Gaussian distributed accord ing to the CRB in Eq .(25), th e pr obability that ˆ θ = θ + ˜ θ ∈ [ 2 π i ′ q , 2 π ( i ′ +1) q ) is ( see Fig. 9) P i ′ ( θ ) = Z 2 π ( i ′ +1) q 2 πi ′ q 1 √ 2 π σ ˜ θ e − ( x − θ ) 2 2 σ 2 ˜ θ dx, (27) where i ′ ∈ { 0 , 1 , · · · , q − 1 } an d ˜ θ is th e estimation error . Thus, P QI A can b e comp uted as P QI A ( θ ) = P q − 1 i ′ =0 P i ′ ( θ ) 2 . Note that P QI A ( θ ) is a f unction of θ . The value of P QI A ( θ ) goes up when the “tr ue” θ appro ximates th e cen ter of a sector and down when θ is clo se to the boun daries of a secto r . In fact, gi ven φ ∈ [0 , 2 π ] , P QI A ( θ ) is symmetric to the center of a sector and is chang ing perio dically with period 2 π / q . Our simulation results indicate that the variance o f phase estimate is much smaller than one. Thus, g iv en θ ∈ [ 2 π i q , 2 π ( i +1) q ) , P QI A ( θ ) is mainly determin ed by P i ( θ ) ( i ′ = i ) . Based o n the above an alysis, we can com pute th e average prob ability o f quantization in dex agreement as P QI A = Z 2 π ( i +1) q 2 πi q P QI A ( θ ) q 2 π dθ (28) ≈ Z 2 π ( i +1) q 2 πi q P 2 i ( θ ) q 2 π dθ. When nodes i and j ’ s e stimates lie in the same inter val, th ey agree on a bit vector of len gth log 2 q ; o therwise they ag ree on no bit. Hence, the expected key rate is R C RB k = P QI A log 2 q T c . (29) Note tha t p e ≈ 1 − P QI A if we assume zero bits are gen- erated when two no des’ estimates fall into different intervals. If gray codes are utilized, p e ≈ 1 − P QI A / log 2 q . 0 2 ( 1 ) i q S 2 i q S 2 ( 1 ) i q S 2 ( 2) i q S 2 ( 1 ) i q S 2 q S 2 S ˆ T T Fig. 9. An illustrati on of estimati on error distri butio n on quantiz ation interv als. A P P E N D I X C P R O O F O F T H E O R E M 3 Pr o of: Assume N relay nodes are inv olved with the key establishment. An eavesdropper E mon itors a ll the co mmu- nications and tries to use these in formation to find the secret key . W ith out loss of gen erality , we assum e the key can b e established in o ne rou nd. W e h av e I ( b R AB ; b R B A ) = K AB (30) I ( b R AR j ; b R R j A ) = K j 1 (31) I ( b R B R j ; b R R j B ) = K j 2 (32) Suppose A an d B alw ays choose K j 1 as the ir key c ompon ent. Let M 0 = { b R AE , b R B E } . T he infor mation E could learn dur- ing the agreement of K j 1 is M j = { b R AE , b R B E , b R R j E , K j 1 ⊕ K j 2 } . Because chann els between any two pair of no des a re indepen dent, hence, for any ǫ > 0 , we have I ( b R AE , b R B E ; K AB ) ≤ ǫ (33) I ( b R AE , b R B E , b R R j E ; K j 1 ) ≤ ǫ, (34) After the r elay node R j broadc asts K j 1 ⊕ K j 2 , E learns K j 1 ⊕ K j 2 . Howev er I ( K j 1 ⊕ K j 2 ; K j 1 ) = 0 . (35) It is equ i valent to a on e-time-pad encry ption on K j 1 with secrete key K j 2 . W ithout kn owing K j 2 , E could learn n othing from the ciphertext K j 1 ⊕ K j 2 , thu s we have I ( M j ; K j 1 ) = I ( b R AE , b R B E , b R R j E ; K j 1 ) + (36 ) I ( K j 1 ⊕ K j 2 ; K j 1 ) ≤ ǫ. The total inform ation obtained by E is the set { M 0 , M 1 , M 2 , . . . , M N } , whose elements are indepen dent of each other . On the other side, A an d B obtain the key set { K AB , K 11 , K 21 , . . . , K N 1 } , whose eleme nts are also indepen dent of each other . Acco rding to the in depend ence of the rand om variables an d the basic pr operties of mutual informa tion, we hav e I ( M 0 , M 1 , M 2 , . . . , M j ; K AB , K 11 , K 21 , . . . , K j 1 ) = I ( M 0 ; K AB ) + n X j =1 I ( M j ; K j 1 ) ≤ ( N + 1) ǫ R E F E R E N C E S [1] C. E. Shannon, “Communi cation theory of s ecrec y systems, ” Bell System T ech nical Journ al , vol. 28, n o. 4, pp. 656–715, 1949. [2] U. M. Maure r , “Informati on-theoret ically secure secret-k ey agree ment by not authentic ated public discussion, ” in Pro c. of EUR OCRYPT’97 , 1997, pp. 209–225. [3] U. M. Ma urer and S. W olf, “Secret-k ey a greement over unauthe nticat ed public channe ls i: Definition s and a complete ness result, ” IEEE T ransac- tions on Information Theory , vol. 49, no. 4, pp. 822–831, 2003. [4] R. Ahlswede and I. Csisz ´ ar , “Common randomness in information theo ry and cryptogr aphy - i: Secret sharing, ” IEEE T ransactions on Information Theory , vol. 39, no. 4, pp. 1121–1132, 1993. [5] A. A. Hassan, W . E . Stark, J. E. Hershe y , and S. Chenna keshu, “Cryp- tographi c ke y agreement for mobile radio, ” Digital Signal Pr ocessing , vol. 6, pp. 207–212, 1996. [6] B. Azimi-Sadjadi , A. Kiayi as, A. Mercado, and B. Y ener , “Robust k ey generat ion from signal en v elopes in wireless netwo rks, ” in Proc . of CCS’07 , 2007, pp. 401–410. [7] S. Mathur , W . Trappe, N. Mandayam, C. Y e, and A. Reznik, “Radio- telep athy: extra cting a secret key from an unauthe nticat ed wireless channe l, ” in Proc. of MobiCom’08 , 2008, pp. 128–139. [8] S. Jana, S. N. Premnath, M. Clark, S. K. Kasera, N. Patw ari, and S. V . Krishnamurthy , “On the effec ti vene ss of secret ke y extracti on from wireless signal strength in real en vironments, ” i n Pro c. of MobiCom’09 , 2009, pp. 321–332. [9] K. Zeng, D. Wu , A. J. Chan, and P . Mohapatra , “Exploiti ng m ultipl e- antenna div ersity for shared secret key generation in wirele ss networks, ” in Pr oc. of INFOCOM’10 , 2010, pp. 1837–1845. [10] C. Y e, S. Mathur , A. Rez nik, Y . Shah, W . T rappe, and N. B. Mandayam, “Informati on-theore tically secret key generation for fading wireless chan- nels, ” I EEE T ransact ions on Inf ormation F ore nsics and Security , vol. 5, no. 2, pp. 240–254, 2010. [11] A. Goldsmith, W ireless Communic ations . Cambridge Uni ve rsity Press, 2005. [12] R. Wilson, D. Tse, R. A. Scholtz, and L . Fello w , “Channel identificati on: Secret sharing using reci procity in uwb channel s, ” IEE E T ransactions on Informatio n F oren sics and Security , pp. 364–375, 2007. [13] A. M. Sayeed and A. Perrig, “Secure wireless communications: Se cret ke ys through multipat h, ” in Proc .of ICASSP’08 , 2008, pp. 321–332. [14] Q. W ang, H. Su, K. Ren, and K. Kim, “Fast and scalabl e secret ke y generat ion explo iting channel phase randomness in wireless networks, ” in Pr oc. of IEEE INFOCOM’11 , 2011, pp. 1422–1430. [15] R. Renner and S. W olf, “The exac t price for unconditi onally secure asymmetric cryptography , ” in Proc . of EUROCRYPT’04 , 2004, pp. 109– 125. [16] Y . D odis, J. Katz, L. Reyzin, and A. Smith, “Robust fuzzy extra ctors and authent icate d key agreement from close secre ts, ” in Proc. of CRYPTO’06 , 2006, pp. 232–250. [17] B. Kanukurthi an d L. Re yzin, “Ke y agreement fro m close secrets o ver unsecured channels, ” in Pr oc. of EU R OCRYPT’09 , 2009, pp. 206–223. [18] Y . Dodis and D. W ichs, “Non-malle able extrac tors and symmetric key cryptogra phy from weak secrets, ” i n Pr oc. of STOC’09) , 2009, pp. 601– 610. [19] D. C. Rife, “Digital-t one parameter estimation in the presence of gaussian noise, ” Ph.D. dissertation, Polytechnic Univ ersity , 1973. [20] D. Rife and R. Boorstyn, “Single-t one parameter estimation from discrete -time observat ions, ” IEEE T ran sactions on Information Theory , vol. 20, no. 5, pp. 591–598, Sep. 1974. [21] Y . Dodis, R. Ostrovsk y , L. Reyzin, and A. Smith, “Fuzzy extract ors: Ho w to generate strong keys from biometrics and other noisy data, ” SIAM J ournal of Computing , v ol. 38, no. 1, pp. 97–139, 20 08. [22] L. Lai and H. V . Poor , “ A unified frame work for ke y agree ment over wireless fadi ng channel s, ” in IEEE Information Theory W orkshop (ITW) , 2009, pp. 100–104. [23] A. Rukhin, J. Soto, J. Nechv atal, M. Smid, E. Barker , S. Leigh, M. Le v enson, M. V angel, D. Banks, A. He chert, J. Dray , and S. V o, A Statist ical T est Suite F or Random and Ps eudor andom Number Generator s F or Cryp togr aphic Applications , 800th ed., Nationa l Institute of Standar ds and T echnol ogy , May 2001.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment