Website Detection Using Remote Traffic Analysis
Recent work in traffic analysis has shown that traffic patterns leaked through side channels can be used to recover important semantic information. For instance, attackers can find out which website, or which page on a website, a user is accessing simply by monitoring the packet size distribution. We show that traffic analysis is even a greater threat to privacy than previously thought by introducing a new attack that can be carried out remotely. In particular, we show that, to perform traffic analysis, adversaries do not need to directly observe the traffic patterns. Instead, they can gain sufficient information by sending probes from a far-off vantage point that exploits a queuing side channel in routers. To demonstrate the threat of such remote traffic analysis, we study a remote website detection attack that works against home broadband users. Because the remotely observed traffic patterns are more noisy than those obtained using previous schemes based on direct local traffic monitoring, we take a dynamic time warping (DTW) based approach to detecting fingerprints from the same website. As a new twist on website fingerprinting, we consider a website detection attack, where the attacker aims to find out whether a user browses a particular web site, and its privacy implications. We show experimentally that, although the success of the attack is highly variable, depending on the target site, for some sites very low error rates. We also show how such website detection can be used to deanonymize message board users.
💡 Research Summary
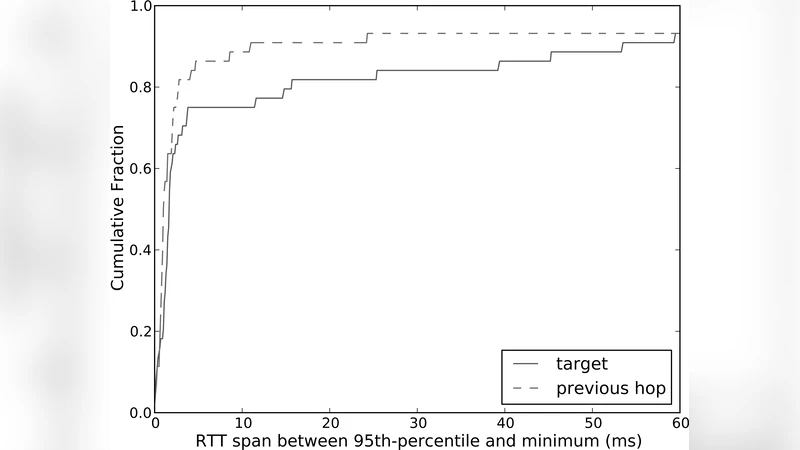
The paper introduces a novel remote traffic analysis attack that allows an adversary to infer a home broadband user’s web‑browsing activity without ever observing the user’s traffic directly. The core insight is that a remote attacker can probe the queue at the user’s DSL access router (DSLAM) by sending frequent ICMP echo requests (pings) and measuring the round‑trip time (RTT) of each probe. Because the DSL “last‑mile” link is orders of magnitude slower than the rest of the Internet path, the queuing delay incurred at the DSLAM dominates the variation in RTT. When the user downloads a web page, a burst of large TCP packets queues up at the DSLAM; each subsequent ping experiences an extra waiting time proportional to the total size of those packets. By subtracting the minimum RTT observed (which approximates the constant propagation and transmission delays on the rest of the path) from each measured RTT, the attacker isolates the queuing component and reconstructs an approximate time‑series of the total bytes arriving at the DSLAM in each probe interval.
The authors formalize this process with a FIFO queue model, ignoring the negligible service time of the tiny ping packets and assuming that the DSLAM serves packets at a constant rate proportional to size. They present a simple algorithm that, for each probe, computes the arrival and departure times, estimates the total size of user packets that arrived during the preceding interval, and discards small variations below a noise threshold η. The resulting series closely mirrors the original traffic’s packet‑size sequence.
To turn this noisy side‑channel data into a usable fingerprint, the paper adapts the well‑known website fingerprinting technique to a detection scenario: the attacker wants to know whether the victim visited a particular target site, not which site among many. Because the remote measurements are much noisier than local ones, the authors employ Dynamic Time Warping (DTW) as a distance metric, which can align sequences of differing length and tolerate timing jitter. They build a training set of DTW profiles for 1,000 popular websites using an emulated DSL link and a virtual execution environment that mimics a typical home user’s browser behavior. The remote attacker then probes a real DSL line in the United States from a rented server in Montreal, Canada, collecting RTT traces while the victim browses the web. For each target site, the attacker computes the DTW distance between the observed remote trace and the stored profile; a low distance indicates a match.
Experimental results show highly variable performance across sites. For a substantial fraction of the tested websites, the attack achieves false‑positive rates below 1 % and false‑negative rates under 5 %, demonstrating that reliable detection is possible despite the noisy side channel. When the training and testing data are collected from the same physical location (i.e., the same DSL environment), detection rates improve dramatically, confirming that environmental mismatches are a primary source of error. Conversely, sites with traffic patterns similar to many others or with less distinctive burst structures are harder to detect.
The paper also discusses practical implications. The attack costs only a few dollars per month for a virtual private server and a lightweight probing script, and it imposes negligible additional load on the victim’s connection, making it hard for users to notice. Potential adversaries include corporations monitoring employee browsing of competitors, or entities attempting to deanonymize participants on message boards by correlating visits to specific forums. The authors outline several limitations: the technique relies on the presence of a low‑bandwidth “last‑mile” link (DSL), it degrades when ISPs apply traffic shaping or QoS that adds variable delay, and it requires a pre‑collected training set for each target site. Future work suggested includes multi‑path probing, machine‑learning‑based noise reduction, and defensive measures such as randomizing queuing delays.
In conclusion, the study demonstrates that remote queuing side‑channels are a realistic and potent privacy threat. By showing that an attacker can remotely reconstruct a user’s traffic pattern and reliably detect visits to specific websites, the paper expands the threat model for traffic analysis beyond local eavesdroppers and calls for renewed attention to the design of broadband access networks and the development of countermeasures.
Comments & Academic Discussion
Loading comments...
Leave a Comment