A New Trusted and Collaborative Agent Based Approach for Ensuring Cloud Security
In order to determine the user’s trust is a growing concern for ensuring privacy and security in a cloud computing environment. In cloud, user’s data is stored in one or more remote server(s) which poses more security challenges for the system. One of the most important concerns is to protect user’s sensitive information from other users and hackers that may cause data leakage in cloud storage. Having this security challenge in mind, this paper focuses on the development of a more secure cloud environment, to determine the trust of the service requesting authorities by using a novel VM (Virtual Machine) monitoring system. Moreover, this research aims towards proposing a new trusted and collaborative agent-based two-tier framework, titled WAY (Who Are You?), to protect cloud resources. The framework can be used to provide security in network, infrastructure, as well as data storage in a heterogeneous cloud platform. If the trust updating policy is based on network activities, then the framework can provide network security. Similarly, it provides storage security by monitoring unauthorized access activities by the Cloud Service Users (CSU). Infrastructure security can be provided by monitoring the use of privileged instructions within the isolated VMs. The uniqueness of the proposed security solution lies in the fact that it ensures security and privacy both at the service provider level as well as at the user level in a cloud environment.
💡 Research Summary
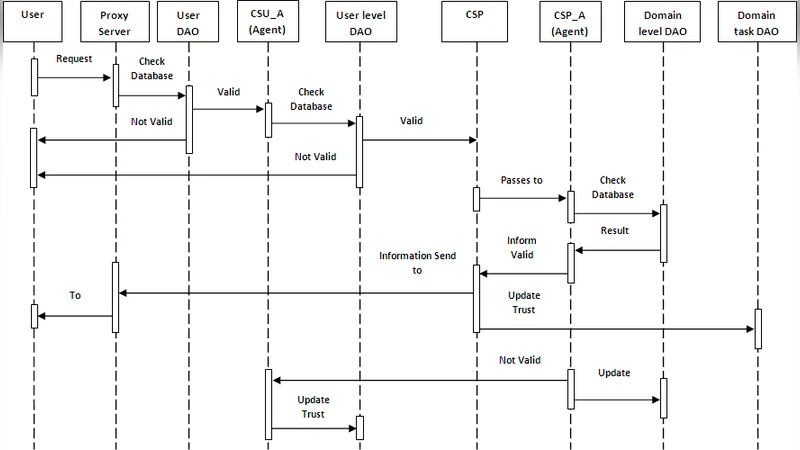
The paper addresses the growing concern of trust management in cloud computing, where users’ data reside on remote servers and are exposed to a variety of security threats. To mitigate these risks, the authors propose a two‑tier, agent‑based framework called WAY (Who Are You?). The architecture consists of a proxy server that mediates initial authentication, a Cloud Service User Agent (CSU_A) operating in a “Broker Domain” (Level 1), and a Cloud Service Provider Agent (CSP_A) residing in the “Provider Domain” (Level 2). Each agent maintains a local database of trust values for users or domains and updates these values after every interaction.
The workflow proceeds as follows: a Cloud Service User (CSU) submits credentials to the proxy server. Upon successful basic authentication, the request is forwarded to CSU_A, which checks the user’s current trust score against a predefined threshold. If the score exceeds the threshold, the request is passed to the CSP; otherwise it is dropped. At the provider side, CSP_A evaluates the trustworthiness of the originating domain using its own trust database. Only when the domain’s trust score also exceeds its threshold does the CSP deliver the requested data back to the user via the proxy. After each successful or failed transaction, both agents adjust the corresponding trust scores—incrementing for trusted actions and decrementing for malicious or unauthorized behavior. Repeated violations eventually lead to the user or domain being black‑listed.
The authors claim that this dual‑layer trust verification can simultaneously protect network traffic, storage access, and infrastructure operations (e.g., monitoring privileged VM instructions). They argue that, unlike traditional cryptography‑centric solutions, their approach focuses on dynamic, behavior‑based trust assessment, thereby providing a more adaptable security posture.
In the related‑work section, the paper briefly surveys cryptographic schemes, dynamic security measures, and domain‑trust models, positioning WAY as a novel combination of proxy‑mediated authentication and distributed trust agents. However, the discussion lacks a deep comparative analysis and does not clearly differentiate WAY from existing proxy‑based or multi‑domain trust frameworks.
The experimental evaluation is limited to a Java simulation executed on a modest desktop (2 GB RAM, Intel i3). Three user categories—trusted, innocent, and non‑trusted—are modeled, and two task types (trusted and non‑trusted) are generated over a fixed time window. Results show that non‑trusted users have a markedly lower success rate in completing tasks, while trusted and innocent users succeed more often. No quantitative metrics such as latency, throughput, false‑positive/negative rates, or scalability are reported. Moreover, the simulation does not incorporate realistic cloud workloads, network conditions, or sophisticated attacks like SQL injection, XSS, or DDoS, limiting the external validity of the findings.
The performance analysis section describes a probabilistic trust update mechanism but omits the actual mathematical formulation (e.g., weighting factors, decay functions). Consequently, readers cannot reproduce or verify the trust calculations. The paper also fails to detail how VM monitoring of privileged instructions is implemented, leaving a critical component of the proposed security model unexplained.
Overall, the contribution of the paper lies in proposing a conceptual two‑tier trust architecture that combines proxy authentication with distributed trust agents. While the idea of dynamically adjusting trust scores based on observed behavior is appealing, the manuscript suffers from several shortcomings:
- Insufficient technical detail – The trust scoring algorithm, threshold selection, and VM monitoring mechanisms are described only at a high level.
- Weak experimental validation – The simulation lacks realism, does not benchmark against existing solutions, and provides limited performance metrics.
- Limited novelty discussion – The related‑work comparison is superficial, making it difficult to assess the true originality of the approach.
- Presentation issues – The paper contains numerous typographical errors, inconsistent terminology, and a lack of clear figures or pseudocode.
For the framework to be considered a solid contribution, future work should (a) formalize the trust model with explicit equations, (b) implement a prototype on a real cloud platform (e.g., OpenStack or Kubernetes) to evaluate security and performance under realistic attack scenarios, and (c) compare the approach against state‑of‑the‑art trust and access‑control mechanisms. Only then can the proposed WAY architecture be validated as an effective solution for enhancing cloud security through collaborative, trust‑aware agents.
Comments & Academic Discussion
Loading comments...
Leave a Comment