Quantum cryptography
This is a chapter on quantum cryptography for the book “A Multidisciplinary Introduction to Information Security” to be published by CRC Press in 2011/2012. The chapter aims to introduce the topic to undergraduate-level and continuing-education students specializing in information and communication technology.
💡 Research Summary
This chapter provides a comprehensive introduction to quantum cryptography aimed at undergraduate and continuing‑education students in information and communication technology. It begins by contrasting classical cryptography, whose security rests on unproven mathematical assumptions, with quantum cryptography, whose security is guaranteed by the laws of physics. The authors motivate the field by noting that future quantum computers could efficiently factor large numbers (Shor’s algorithm) and thus break widely used public‑key schemes such as RSA, while the one‑time pad remains information‑theoretically secure. Quantum cryptography solves the key‑distribution problem that plagues the one‑time pad by exploiting the behavior of single quantum particles, typically photons.
The chapter explains the distinction between classical bits and quantum bits (qubits). A qubit can be prepared in one of two non‑orthogonal bases (commonly denoted X and Z). Measuring a qubit in the wrong basis yields a random outcome and irreversibly collapses the original state. This “measurement‑induced disturbance” is illustrated with a vivid analogy of a box with two doors: opening the correct door reveals the stored color, while opening the wrong door randomizes it. The no‑cloning theorem is introduced to show that an unknown qubit cannot be perfectly copied because any attempt to read it inevitably disturbs it. This property underpins the security of quantum key distribution (QKD).
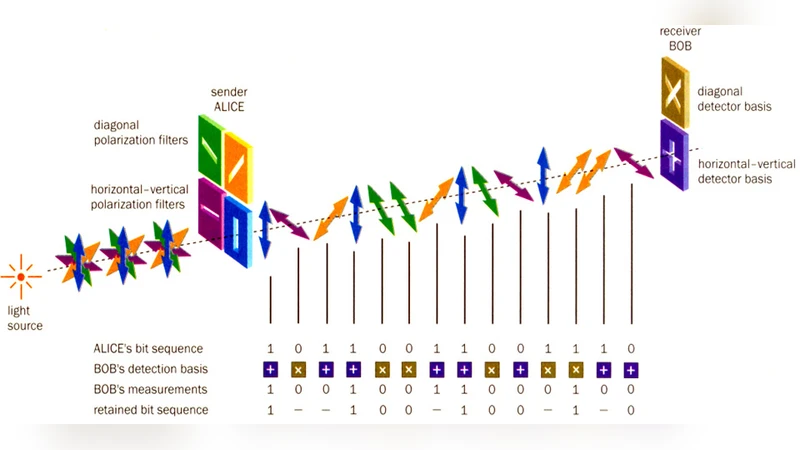
The core protocol, BB84, is described in detail. Alice generates a random bit string and encodes each bit onto a photon using either the horizontal/vertical polarization basis or the diagonal (+45°/‑45°) basis, chosen at random. Bob receives the photons and, also at random, selects one of the two measurement bases using interchangeable polarizing beam splitters. After transmission, Alice and Bob announce over an authenticated public channel which bases they used for each photon, discarding all bits where the bases differed. The remaining “sifted key” is shared with high probability of agreement, provided no eavesdropping occurred.
Eavesdropping is modeled by an adversary Eve who intercepts photons and measures them. Because Eve does not know the basis, she guesses correctly only half the time; the other half the time she introduces errors that raise the quantum bit error rate (QBER). Alice and Bob estimate QBER by publicly comparing a random subset of the sifted key. If the error rate exceeds a predetermined threshold, they abort the session; otherwise they proceed.
Practical implementations are discussed next. Real devices—single‑photon sources, optical fibers or free‑space channels, polarizing beam splitters, and single‑photon detectors—are imperfect. Photon loss, detector dark counts, and misalignment of measurement bases cause a baseline QBER of a few percent even in the absence of an attacker. Consequently, the protocol must assume the worst case: all observed errors could be due to eavesdropping.
To obtain a perfectly correlated secret key, Alice and Bob apply classical error‑correction algorithms (e.g., Cascade or LDPC codes) over the public channel, reconciling any discrepancies introduced by device imperfections. This public exchange inevitably leaks some information to Eve, so a final privacy‑amplification step is required. By applying a randomly chosen universal hash function, they compress the reconciled key into a shorter final key about which Eve’s knowledge is negligible (e.g., less than 10⁻⁶ bits). Numerical examples illustrate that with a 4 % QBER, 2000 raw bits can be distilled into 754 secure bits; with an 8 % QBER, only about 105 secure bits remain.
The chapter concludes by emphasizing that while quantum cryptography offers unconditional security in principle, its real‑world security depends on the quality of hardware, accurate error estimation, and robust classical post‑processing. Authentication of the public classical channel, careful management of loss and noise, and ongoing advances in photon‑source and detector technology are essential for scaling QKD to long distances and practical networks. The authors point to emerging directions such as satellite‑based QKD and integrated photonic platforms, suggesting that quantum cryptography is poised to become a cornerstone of future information‑security infrastructures.
Comments & Academic Discussion
Loading comments...
Leave a Comment