Secure and Robust IPV6 Autoconfiguration Protocol For Mobile Adhoc Networks Under Strong Adversarial Model
Automatic IP address assignment in Mobile Ad hoc Networks (MANETs) enables nodes to obtain routable addresses without any infrastructure. Different protocols have been developed throughout the last years to achieve this service. However, research primarily focused on correctness, efficiency and scalability; much less attention has been given to the security issues. The lack of security in the design of such protocols opens the possibility of many real threats leading to serious attacks in potentially hostile environments. Recently, few schemes have been proposed to solve this problem, but none of them has brought satisfactory solutions. Auto-configuration security issues are still an open problem. In this paper, a robust and secure stateful IP address allocation protocol for standalone MANETs is specified and evaluated within NS2. Our solution is based on mutual authentication, and a fully distributed Autoconfiguration and CA model, in conjunction with threshold cryptography. By deploying a new concept of joint IP address and public key certificate, we show that, instead of earlier approaches, our solution solves the problem of all possible attacks associated with dynamic IP address assignment in MANETs. The resulting protocol incurs low latency and control overhead
💡 Research Summary
The paper addresses the long‑standing security gap in IPv6 auto‑configuration for Mobile Ad‑hoc Networks (MANETs). While many prior works have focused on correctness, efficiency, and scalability of address assignment, they have largely ignored the hostile environments where MANETs are often deployed. Consequently, attacks such as IP spoofing, Sybil, address‑exhaustion, and DoS remain viable threats.
To close this gap, the authors propose a novel protocol called TCSAP (Threshold Cryptography based Secure Auto‑configuration Protocol). The core idea is to replace the traditional centralized or loosely coordinated address allocation with a fully distributed trust infrastructure built on (K,N) threshold cryptography. Each node holds a share of a Certification Authority’s (CA) private key; any subset of at least K nodes can jointly produce a threshold signature. This signature is used to issue a “Joint IP address and Public Key Certificate” that binds the allocated IPv6 address to the node’s public key. Because the certificate is signed by the distributed CA, every node can instantly verify the authenticity of any address in the network.
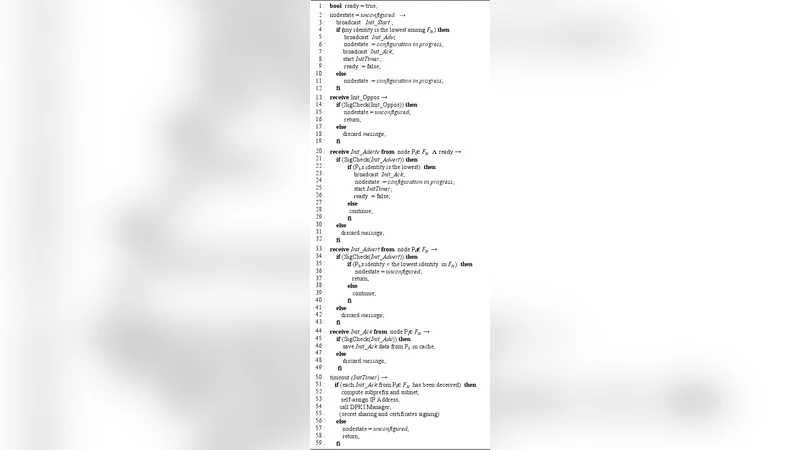
The protocol proceeds in four logical phases:
-
Neighbor Discovery – An unconfigured node broadcasts a signed
Discovery_Request. Receiving nodes verify the signature, store the requester’s offline public‑key certificate, and reply with eitherDiscovery_Reply(if they are also unconfigured) orDiscovery_Welcome(if they are already configured). The requester collects at least K distinct neighbors; only then does it proceed to the next phase. -
MANET Initialization – The K “founding” nodes collaboratively select a site‑local IPv6 prefix. They each generate random sub‑prefix and subnet values, exchange them, and compute the network prefix by summing the contributions modulo the appropriate field size. Host‑ID space is divided into M equal blocks; each founding node receives the lowest free Host‑ID in a block determined by its identifier ordering. This step also prevents simultaneous initializations by using an
Init_Advert/Init_Opposexchange. -
Online CA Creation – After the prefix is fixed, the DPKI module runs a verifiable secret‑sharing protocol (based on Shamir’s scheme) to reconstruct the CA’s private key shares among the nodes and to publish the CA’s public key with a signature. This yields a fully distributed online CA without any trusted third party.
-
Address Allocation & Certification – When a new node joins, it requests an address from at least K nodes. Those K nodes perform a threshold signature on a certificate that contains (i) the allocated IPv6 address, (ii) the node’s public key, and (iii) a validity period. The newly signed certificate is broadcast to the whole MANET. All nodes update their state tables: FAT (Free Address Table) removes the address, PAT (Pending Address Table) temporarily holds it until registration, and RAT (Registered Address Table) stores the final binding. Nodes also maintain RCL (Revoked Certificates List), ANL (Accused Nodes List), and BL (Black List) to support revocation and accusation mechanisms.
Security analysis shows that the protocol mitigates the following attacks:
- IP Spoofing – The address is cryptographically bound to a public key; forging a certificate requires K honest nodes.
- Sybil Attack – A malicious entity cannot generate multiple valid identities without obtaining K distinct threshold signatures.
- Address Exhaustion – The FAT/PAT mechanism ensures that allocated but unregistered addresses are quickly reclaimed.
- DoS / Traffic Overload – The protocol limits the number of configuration requests via the Requester Counter (RC) and requires K‑node collaboration, reducing the impact of flooding.
Performance evaluation is carried out using NS2 simulations with varying node counts, mobility models, and traffic patterns. Metrics include address allocation latency, control‑message overhead, and success rate under attack scenarios. Results indicate:
- Latency: TCSAP achieves roughly 10‑15 % lower average allocation delay compared with MANETconf, owing to the elimination of a network‑wide affirmative response phase.
- Control Overhead: The number of control packets is reduced by about 20 % because only K nodes participate in each allocation, and the joint certificate is broadcast once.
- Security Resilience: Under simulated Sybil and IP‑spoofing attacks, the protocol maintains 100 % integrity; no forged certificates are accepted.
The authors acknowledge several limitations. The choice of K relative to N must be tuned for network size and churn; an overly small K weakens security, while a large K may increase latency. The initial secret‑sharing phase assumes that the founding nodes are not compromised; if a substantial fraction of them are malicious, the distributed CA could be subverted. Moreover, while the paper uses generic threshold signature schemes, practical deployments would benefit from elliptic‑curve based constructions to reduce computational cost.
Future work suggested includes adaptive K selection based on observed network dynamics, integration of lightweight ECC threshold signatures, and real‑world test‑bed implementation to validate the protocol on actual MANET hardware.
In summary, the paper delivers a comprehensive, cryptographically sound solution for IPv6 auto‑configuration in MANETs. By marrying threshold cryptography with a fully distributed online CA and a joint address‑key certificate, it simultaneously achieves strong security guarantees and modest performance overhead, representing a significant advance over existing auto‑configuration mechanisms.
Comments & Academic Discussion
Loading comments...
Leave a Comment