Development of a Window Based Security System for Electronic Data Interchange
The Electronic Data Interchange (EDI) is the exchange of standardized documents between computer systems for business use. The objective of this study is to make Electronic Data Interchange secure to use and to eliminate human intervention in the transfer of data between business partners so that productivity and efficiency can be improved and also promote its usage between two or more trading organizations. This paper provides an overview of EDI by describing the traditional problems of exchanging information in business environments and how the EDI solves those problems and gives benefits to the company that makes use of EDI. This paper also introduces the common EDI Standards and explains how it works, how it is used over the internet and the security measures implemented. The system was executed on both local area network and wide area network after a critical study of the existing EDI methods and also implemented using VB.Net programming language. Finally, an interactive program was developed that handles the transfer of files, with special attention to the security of the items that are being transferred from one computer workstation to another.
💡 Research Summary
The paper titled “Development of a Window Based Security System for Electronic Data Interchange” presents a prototype implementation aimed at securing EDI transactions while reducing human intervention. It begins with a broad overview of EDI, describing how the technology integrates three disciplines—business processes, data processing, and data communications—to replace paper‑based document exchange with automated, standardized electronic messages. The authors outline the traditional problems of manual document handling (errors, delays, high costs) and argue that EDI resolves these issues by providing a structured, machine‑readable format that can be transmitted over networks.
The manuscript then walks the reader through the complete EDI workflow. First, an organization extracts business data from its internal applications and converts it into a standard format (e.g., ANSI X12, EDIFACT) in the “Outbound Translation” step. The resulting file is sent to a pre‑arranged Value‑Added Network (VAN), which acts as an electronic mailbox, routing the message to the appropriate recipient. Upon receipt, the partner performs an “Inbound Translation” to convert the standardized file back into a format usable by its own applications, after which internal processing proceeds. The authors illustrate this data‑processing pipeline with a diagram (Figure 1).
The paper dedicates a substantial portion to describing VANs, their services (mailbox storage, message tracking, protocol translation, inter‑VAN connectivity), and the alternative “Direct Connection” approach where large enterprises bypass VANs and exchange data over dedicated lines or packet‑switched networks. The discussion of security is organized around the classic CIA triad plus non‑repudiation. Confidentiality is achieved through encryption; the authors briefly contrast symmetric‑key and public‑key schemes, noting the operational challenges of key synchronization for symmetric encryption and the growing adoption of public‑key infrastructure (PKI). Authentication is described in terms of passwords and digital certificates, while integrity is ensured by transmitting a hash (or checksum) of the data alongside the payload and verifying it on receipt. Non‑repudiation is addressed via digital signatures, which bind the sender’s identity to the message content.
In addition to the generic security concepts, the authors explain how VANs themselves enforce security: login/password access control, message filtering, optional cryptographic services, and audit capabilities such as traffic accounting and automatic acknowledgments.
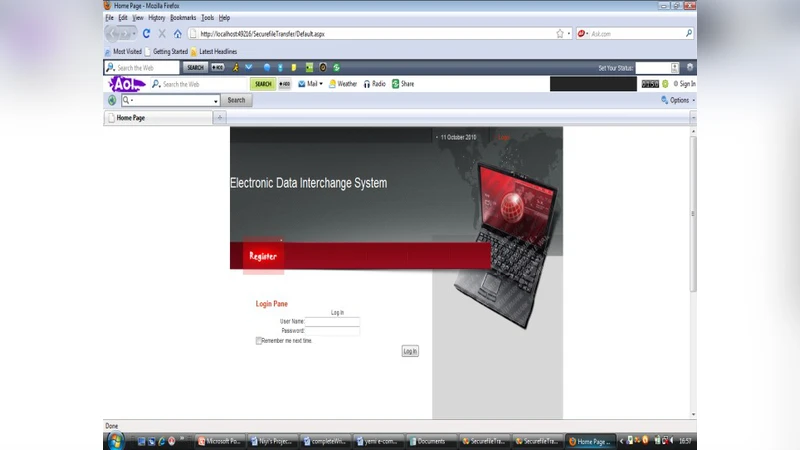
The core contribution of the paper is the design and implementation of a Windows‑based application written in VB.Net that automates the entire EDI exchange process on both local area networks (LAN) and wide area networks (WAN). The application provides a graphical user interface where users select files to transmit, load partner certificates, and initiate secure transfer. Behind the scenes the program performs encryption/decryption, digital signing, and hash verification automatically. Transfer logs, status messages, and audit trails are displayed in real time, allowing users to monitor the integrity and confidentiality of each transaction.
While the prototype demonstrates that a GUI‑driven tool can encapsulate the essential security functions of EDI, the paper lacks rigorous evaluation. No performance benchmarks (throughput, latency), no security analysis (threat model, resistance to replay or man‑in‑the‑middle attacks), and no comparison with existing EDI standards such as AS2, ebXML, or ODETTE are provided. The choice of VB.Net is not justified, and the absence of details about the cryptographic algorithms (e.g., AES‑256, RSA‑2048) and key management procedures raises questions about the practical robustness of the solution. Moreover, the manuscript contains numerous typographical and formatting errors, which detract from its scholarly credibility.
In conclusion, the study offers a useful educational prototype that visualizes the EDI workflow and integrates basic security mechanisms into a Windows application. However, to be viable for real‑world deployment, future work must address scalability (support for multiple trading partners), compliance with modern EDI protocols, comprehensive security testing, and integration with PKI infrastructures. Only then can the system move beyond a proof‑of‑concept to a production‑grade EDI security platform.
Comments & Academic Discussion
Loading comments...
Leave a Comment