Enhanced User Authentication through Trajectory Clustering
Password authentication is the most commonly used technique to authenticate the user validity. However, due to its simplicity, it is vulnerable to pseudo attacks. It can be enhanced using various biometric techniques such as thumb impression, finger movement, eye movement etc. In this paper, we concentrate on the most economic technique, based on the user habitual rhythm pattern i.e. not what they type but how they type is the measure for authenticating the user. We consider the latency between key events as the trajectory, and trajectory clustering is used to obtain the hidden patterns of the user. Obtained pattern can be considered as a cluster of measurements that can be used to differentiate from other users. We evaluated the proposed technique on the data obtained from the 100 users.
💡 Research Summary
The paper addresses the well‑known vulnerability of password‑only authentication by augmenting it with a behavioral biometric: keystroke dynamics. Rather than relying on simple statistical descriptors (means, standard deviations) or conventional clustering methods such as k‑means, the authors model the latency between successive key events as a time‑ordered “trajectory”. They then apply a trajectory‑clustering framework that uses the Hausdorff distance as the dissimilarity measure.
The Hausdorff distance evaluates the worst‑case point‑to‑set distance between two trajectories, making it highly sensitive to even minor variations in typing rhythm. The authors first compute a full pairwise distance matrix for all trajectories belonging to a given user. An initial clustering (Algorithm‑1) groups trajectories whose mutual Hausdorff distance falls below a user‑defined threshold. Within each cluster, the trajectory with the smallest cumulative distance to all other members is selected as the representative trajectory (RepTraj) (Algorithm‑2). The set of RepTraj’s then serves as provisional cluster centroids for a re‑clustering step (Algorithm‑3) that iterates until the representatives stabilize.
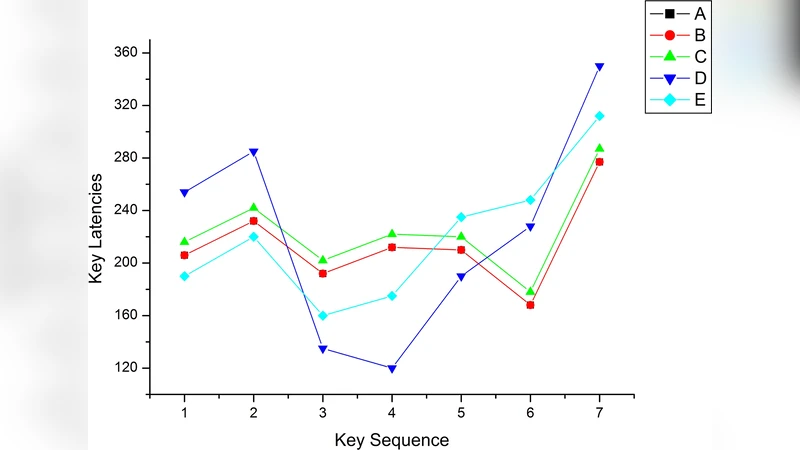
The experimental protocol involved 100 computer‑science students from JNTU Kakinada. Each participant chose a random‑length password and typed it five times in three separate sessions, yielding 15 raw trajectories per user. For each session a RepTraj was generated; the three RepTraj’s were then clustered to produce a final user‑specific representative trajectory (userRepTraj) and an average Hausdorff distance that serves as the user‑specific acceptance threshold (userThreshold). During authentication, the system captures a new trajectory from the login attempt, computes its Hausdorff distance to userRepTraj, and grants access if the distance is ≤ userThreshold.
Performance was measured using False Acceptance Rate (FAR) and False Rejection Rate (FRR). The approach achieved an almost zero FAR, indicating strong resistance to impostor attacks. However, novice users exhibited a noticeably higher FRR, reflecting the fact that their typing patterns are less stable and therefore more likely to exceed the fixed threshold. The authors also note that environments with very few keystrokes (e.g., ATM PIN entry) provide insufficient data for the static trajectory model, limiting applicability in such contexts.
Key contributions include: (1) introducing Hausdorff‑based trajectory clustering as an alternative to k‑means, thereby avoiding the latter’s reliance on spherical clusters and sensitivity to initial seed selection; (2) incorporating three event types—key press, key release, and inferred key‑type pressure—to enrich the feature space; and (3) defining per‑user thresholds derived from intra‑user trajectory variability, which tailors the decision boundary to individual typing habits.
The paper also acknowledges limitations. Computing Hausdorff distances for all trajectory pairs incurs O(N²) time, which may be prohibitive for large‑scale or real‑time deployments without optimization (e.g., pre‑computed distance caches, approximation techniques, or dimensionality reduction). Moreover, the static threshold does not adapt to gradual changes in a user’s typing behavior caused by fatigue, stress, or hardware changes. Future work could explore adaptive threshold updating, online learning of representative trajectories, and the fusion of additional biometric signals such as pressure sensors or touch dynamics to further improve both security and usability.
Comments & Academic Discussion
Loading comments...
Leave a Comment