Grid Information Security Functional Requirement - Fulfilling Information Security of a Smart Grid System
This paper describes the background of smart information infrastructure and the needs for smart grid information security. It introduces the conceptual analysis to the methodology with the application of hermeneutic circle and information security fu…
Authors: Amy Poh Ai Ling, Mukaidono Masao
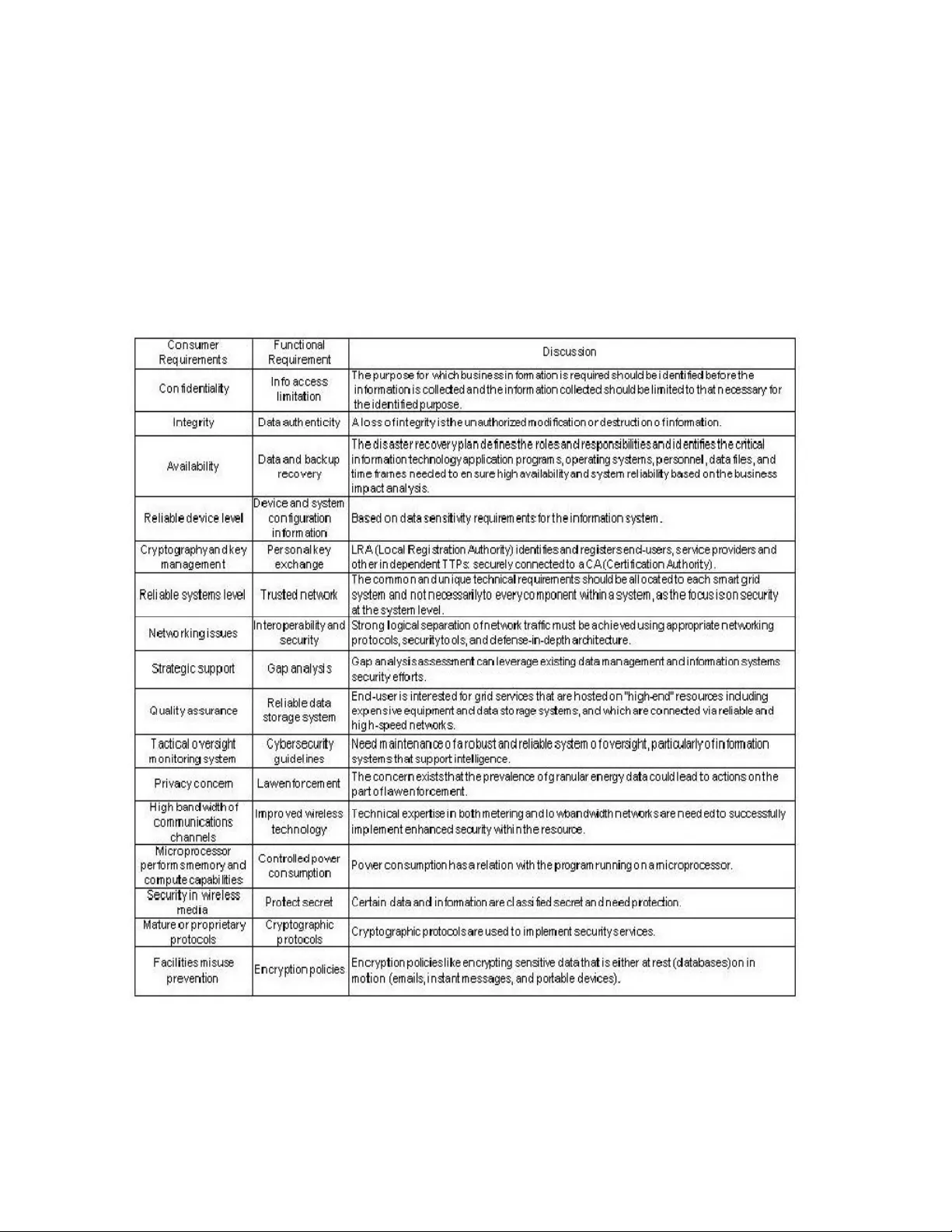
International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 DOI: 10 .5121/ijgca.20 11.2201 1 GRID INFORMATION SECURITY FUNCTIONAL REQUIREMENT FULFILLING INFO RMATION SE CURITY O F A SMA RT GRID SY STEM Am y Poh Ai Lin g 1 and Mukaido no Masa o 2 1 Department of Mathematical Modeling, Anal ysis & Simulation , Graduate School of Advanced Mathematical S ciences, Meiji University, Kawasaki, J apan amypoh@m eiji.ac.j p 2 Department of Computer Science, School of Sci ence and Technolog y, Meiji Universit y , Kawasaki, J apan masao@cs .meiji.ac .jp A BSTRACT This paper de scribes the backg round of smart informa tion infra structure and th e needs for smart grid informatio n security. It intro duces the conc eptual analysis to the meth odology with the applica tion of hermeneu tic circle an d inform ation security fun ctional req uirement id entification . Informa tion secu rity for the grid market co ver matte rs includ es autom ation and communica tions indu stry that a ffects the o peration of electric po wer systems and the fun ctioning of the utilities that mana ge them and its a wareness of this informatio n infrastructure has become critica l to the reliability of the power system. C ommun ity benefits from o f cost savings, flex ibility an d deplo yment along with th e establish ment o f wireless communicatio ns. However, conc ern revo lves ar ound the security protec tions for easily accessible de vices such as the smart meter and the related communicatio ns hardware. On the other hand, the changing po ints between traditiona l versus sma rt grid ne tworking trend and th e informatio n security im portance on the commun ication field reflects the criticality o f grid info rmation security fu nctional requirement identificatio n. The go al of this pa per is to identify the fu nctional requireme nt and relate its significa nce addresses to the consumer requirement of an information security o f a smart grid. Vulne rabilities may bring forth possibility for an attacker to pene trate a network, m ake h eadway adm ission to control software, alter it to load conditions tha t destab ilize th e grid in u npredictable ways. Fo cusing on the g rid information security fu nctiona l requirem ent is stepping ahead in developing consumer trust and satisfaction toward smart grid co mpleteness. K EYWORDS Functio nal Requireme nt, Smart Grid, I nformation Security, Network ing Trend, Consumer Re quirement International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 2 1. INTRODUCTION Information te chnolog y ad vancement paves way to daily conveniences. T oday, we sim ply c an reach someone we know just with a touch on the mobile phone, makes the world bec ome thence small. Distance is no longer a barrier f or comm unication. Likewise, in the nearest future a ll electronic gadgets co uld be controlled via programmed interface software. The c onsumption of electricity at home can be monitored with an access password provided. A culture enc roachment happens through t he interplay of tec hnology and everyday l ife. Traditional distribution ne twork management of power supply and loads has been conc eived as an independent process. However,this traditional approach is changing bi t by bit by an increasing number of distributed channels. T he distribution channel covers t he m eans o f renewable energy resources. Th is wi ll heighten act ive e nergy resourc es like loads, storages and plug-in hybrid vehicles. The emerging of smart g rid pu shes the m arket towards a drastically in crease in the dem and of smart supply of energy fl ow. Grid optimization goes on f or s ystem r eliability, ope rational efficiency and a sset utilization and protection. Smart grid uses t wo-w ay communication systems for better monitoring towards lower energy cons umption. In short, we must ensure that t he integrators consider on security when combining devices system- wide. The satisfaction o f a consum er depends on how strong the information security on the grid can be secured. 2. REVIEW OF LITERATU RE The rising of real incomes and the i ncreasing in abundant of consumer goods have pric ke d demand for g reater consum ption on electronic gadgets in m ost modernized countries. Modeling lifestyle effects on energy demand [1] study that the increase of societal energy consumption influenced by three main i tem s: technical efficiency, lifestyles a nd socio-cultural factors. Technological t ransfer p henom enon is of ten seen as a crucial part contributes to the s olutions of environmental highlights. However, when technological change is seen from the perspective of everyday life, this imag e becomes more complex [2]. 2.1. Grid Information Techn ology Electricity distribution networks create a market place for small-scale power producers and for customers - users of electricity. At t he core of all smart grid definition is advanced metering infrastructure (AMI). T his refers to smart meters and an accompanying co mmunications network that allows two-way communication between the provider of electricity and t he meter. With t his capability, providers have access to real-time i nformation on t he electricity consumption o f each customer. Sm art metering technology will be the foundation of any Smart Grid strategy , as it provides the platform for offering digital- era s erv ices to consumers [3 ]. T o incorporate intermittent energy r esources, a cat egory which r enewable e nergy fall s into, electricity networks will have to become „smarter grid s ‟ with integrated comm unication s ystem s and real time balancing between supply, dem and, and storage [4]. One of the greatest challenges for future electricity grids lay on the de mand side response and creating a system that can shift peak demand, at the same time as being socia lly accept able. T his is a key i ssue as m ajor behav ioural changes are necessary to modify e nergy usage pat terns and t he current demand curve, li kely to be facilitated by suitable user- friendly technology platform s. International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 3 AMI technologies play the r ole of increasing the reliability of the electric power delivery s ystem and bettering cust omer service [5]. These tec hnologies rely on two-w ay communications systems either l ower capacity or speed n arrowband options such as fixed wireless radio frequency (RF) or power line carrier (PLC) or broadband options such as broadband ov er power lines (BPL) or wireless networks. For network operation purposes, more accurate real-time state estimation of the whole network gives i nformation on voltages, loads, l osses and s tressing of com ponents, and a lso makes it possible to optimize, e.g. network topology, voltage control, and load control actions [6]. T he grid it self may be brought o ff more expe ditiously with t he power t o control loads [7] and t he typically hi gher i nformat ion quality, fol lowed by t he consequences of increased data accumulation throughout t he entire system. Gri d technology provides the chance of a simple and transparent access to different i nformation s ources. A dat a grid c an be interpreted as the consolidation o f differen t d ata manag ing systems furnishing the user with data, information and knowledge [8]. 2.2. Needs for Smart Grid In formation Security A number of smart grid information security requirements and regulations are available online [9] [10] [ 11] [12], although those guidelines are a significant step in securing the smart grid, but they do not fully address pote ntial vulnerabilities that can emerge. One of the st rong est arguments made for s ecuring smart meters is that consumers will have ph ysical [13] and potentially logical access to the smart meters. Security is generally described in terms of availability, in tegrity, a nd confidentiality. Cyber system s are vulnerable to worms, virus es, d enial-of- service attacks, malware, phishing, and user errors that com promise integrity and availabil ity [14]. It is important to avoid bari ng a ny potential security risk. As a m atter of f act, grid security technologies have been so far designed and deployed as a middleware layer add-on [15], independently at eac h tier. The need to protect privacy and security of priceless data over the grid is fueling even more need f or common security evaluation criteria. In brief, [16] i nformation security professionals need to be aware t hat the w orkings of the most ba sic IT resource o f electricity supply is changi ng in a manner t hat introduces a far larger and remotely addressabl e attack surface combined wi th the tempting opportunity for mischie f and monetary gain. 3. RESEARCH METHODOLOGY Conceptual analysis was adapted as methodology with the application of hermeneutic circle. Reason b eing he rmeneutic circle is an interpretive [ 17] an d a conceptual-analytical re search method [18]. Thi s ap proach is com monly appl ied by philosophers and t heologians i n re viewing something that is not exp licitly present in it [19]. This study discov ers the assumptions of different i nformation security e fforts where he rmeneutic circle become a natural research methodological choice. International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 4 The concept of this paper’s methodology is exhibite d in Fig ure 1. I t refers t o the idea that one understands of the t ext as a whole is established by reference to the in dividua l parts and one understands of each individual part by reference to the whole [20]. Figure 1. Methodology - Hermeneutic Circle The approach starte d with the construing of adducing and explaining the meaning of Smart Grid and Grid Information Tec hnology . T his is followed by the i nscription of t he need fo r Information Security of a Smart Grid System via literature r eview. Then the f unctional requirement se rves to achieve consumer re quire ment expectation as sumption are dev eloped. The efforts are then lifted with the significance st udy carried ou t. Note that the four main stages fo r this study were supported by three main elements: theory, data and practice that serve as str ong reference for the sources obtained. Inform ation, secur ity an d sm art grid are the m ain k eywords contributed t o the process of literature review to m ake sure the sourcing does not bump- out from the topic set. Meanwhile r esearch is a process of collec ting; an alyz ing and interpreting i nform ation to answer questions, the research process is similar to undertaking a journey. A knowledge base of research methodology plays a crucial role to kick start a smooth study. Figure 2 displays the practical steps undertaken to complete this paper. International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 5 Figure 2. Research Process It started with the identification of the topic followed by formulat ing research problem and extensive literatur e review carefully laid out. Methodology was then developed to direct the path of research process, where analys is and discussion took place. A solid conclusion [21] and future research recommendat ion was writt en to complete this paper. 4. NETWORKING TREND RELATED TO INFORMATION SECURITY Smart grid is already leveraging benefits of networking. It s technologies may even integrate with social networking sites [22] , as well as associat ed security risks. This section examines network security , trust, and privacy concerns with regard to networking sites among consumers. Personal data from profiles may also leak outside the network when search engines index them [23]. With the changes of smart grid and other in the electricity utility industries, new demands on the telecom networks were generated [ 24]. Sm art meter s as electricity transcript ion communicat e International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 6 with residenti al consumer used at least hourly. It transmits at least daily in order to inform more sophisticated time-of-use, real tim e or other billing structure. Dominant current utility architecture involves one-way flow o f e lectricity from a small nu mber of generation facilities to a large number of consumers, data networks form erly served a predominant ly one way flow of information from a sm all number of m ainframe com puters to a large number of dumb t erminals. The networking trends are transforming from its traditional flow to an advance d sm art grid style o f flow, spurring a positive change of networking trends t owards a m ore distributed, digiti zed and multiple source of supply. Sm art G rid Strategy Smart Grid is the nature and co mpatibl e use of alternativ e energ y, it needs to create an open computing system and the establishment of a shared information model, based on the data integration s y stem, o ptimi zes network operation and managem ent [25]. Table 1. Networking Trend Resources can be identifi ed and employed in the most effective manner when the environment is fully connected with suitable mechanisms for sharing information, ensuing great posit ive tran sform ation of electricity service quality and value for both utility provider and end user. As the enabler for the grids, the communi cations network m oulds the base for sm art grid towards a International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 7 qualitative change and a rev italized power utility . The transformati on of network flows was portraying in Table 1. Advanced technologies in physi cal security and storage capability in a network will produce positive smart grid transform ation from its traditional practice. This p ositiv e tr ansformation happened on networking trends, such as info source, traffic fl ow, stan dards, coding, control , autho rity and energy service provider. It aspi res t o assure that households have more proficient and effectiv e contr ol over their energy consumption besides proact ively making a reduction on their energy usage. Constructing smar t grids involves positive transformat ion from traditi onal electricity networks to new technology system by adding sm art sensors, back- end IT systems , s mar t meters and communications networks. All comm unication will be on the grid supported by coding system, open com puting and mass computing system. The po int is, when communicati on is exp osed to open and mass co mput ing, the information security accoun t is considere d being en ormously im portant, this leads to the though t on the crucial of inform ation securi ty functi onal requirement. 5. AWARENESS OF GRID INFORMATION SECURITY FU NCTIONAL REQUIREMENT Smart grid is a “system of systems” [26] where it necessitat ed the evoluti on of technology uniformly across the utilit ies and simpati co with mul titudinous of devi ces. AMI sy stems capture and process data at the meter [27], furnish inform ation to utilities and co nsumer s. It is usually th e case that AMI systems pick-a-back on a variety of wireless systems. While there are other criti cal questions regarding the role that incum bent ‟ s play in deploying technology that will enable more efficient energy markets [28], smart grid transforms the electricity network into the information age with its digital technology [29]. The underpinnin g of situati onal awareness on grid information security is to identify adversaries, estimate i mpact of attacks, evaluate risks, understand situations and make accurate decisions on how to protect the g rid promptly and efficiently. In this paper, situational awareness in grid information security functional requirement is invest igated. A good security system for smar t grids requires it to be thorough. It brings the fact that security capacities must be superimposed such that defense m echanisms hav e sufficient points to detect and mitigate breaches. These capacities should be integral to all segment s of the smart grid sy stem features and com ply with the full set o f grid informati on security functional requirement s. 6. INFORMATION SECURITY FUNCT IONAL REQUIRE MENT IDENTIFICATION 6.1. Identifi cation Process In the process of ident ifying information security functional requirem ent, the significant relationship to consumer requirem ent is taken into considerati on as how it would impact consumer trust and satisfacti on. It refers to the consum er requirem ent devel oped [30]. International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 8 Sixteen functional require ments were discussed with the reference to the sixteen consumer requirement s identified: info access lim itation, data authenticity , data and backup recovery , device and system configuration information, personal key ex change, trusted network, interoperability and security , gap analysis, reliable data storage sy stem , cy ber security gu idelines, law enforcem ent, improved wireless technology, controlled power consumption, protect secret, cryptographic protocols and encrypt ion policies, as in Table 2. Table 2. Inform ation Security Functional Requirement Identificat ion International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 9 1. Info ac cess limitation : Receptiveness is necessitated to alleviate public involvem ent in assessing justifi cations for technologies, syste m s or services, i dentifying purposes of collection, facilitating acce ss and correcti on by the concerned party, a nd se rve in ascertaining the principles observed [31]. In an open system, all form of i nformat ion should be protected b y appropriate controls against unauthorized access, or alteration, disclosure or destruction and against accidental loss o r destruction, and el iminates the need to access customer property. 2. Data authenticity : Security is a consolidative concept. It covers availabili ty, authenticity, confidentiality an d i ntegrity [32]. Sec urity guards a gainst unconventional information modification o r destruction [33] , i nvolves ensuring information non-repudiation and authenticity i s mandatory [34]. Whenever an integrity or authenticity pr oblem is observed, the system must ensure that data is not exploited. 3. Data and backup recovery : The system must always managing, deploying and furbishing up a technology or solution t arget to maxim ize th e b enefits of systems and t echnology which f acilitate to control IT r isk [3 5]. Procedures were dev eloped aiming to render restoration [36], backup, offsite storage and disaster recovery consistent with the entity ‟ s defined system availability and associa ted security policies. 4. Device and system configuration i nformation : Inform ation relating to the i nternal functioning of a com puter system or network [37], i ncluding but not bo unded t o network and device ad dresses, device and s ystem configuration i nformation need an average limits of security pr otect. Taking into account today ‟ s menace en vironment, blended with the heightening interoperability and ope nness, a solid system requires i ncorporat ion of assorted security measures. Important security items would be access control, device and application authentication, layoff and fail ov er fo r extended operation, encryption for secrecy and escape of sens itive data and i nformation [38]. In a configuration system, it i s important to ascertain t hat the devices ar e firm and are ready to def end themselves from at tacked by firmware updates, not e asily swapped out by a ro gue one or highjacked by a spoofed remote device. 5. Personal key exchange : Key m anagement system provides cardinal security s ervices such as f reshness, secrecy, key synchronization, authentication, independence, ratification , and forward and backward secrecy [39][ 40]. Kerckhos ‟ Principle st ated that t he attacker knows everything about the security solution [41] with the exception of the key . 6. Trusted network : Vulnerabilities may bring forth possibility for an attacker to penetrate a network, make headway admission t o control software, hence make an al teration to l oa d conditions to destabilize the grid in unpredictable w ays. The lowest t one of a harmonic series of system-lev el components of a network security admitte d trusted network [42]. Thus, approaches to s ecure ne tworked technolog ies [43] and to protect p rivacy m ust be designed and implemented ahead in the tr ansition to the smart grid. International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 10 7. Interoperability and security : Th e interoperability proffered by IP has enabled converged networks that provide both data a nd voice to become common in businesses [44], and a variety of triple play providers currently offer residential data, voice, and video on converged networks [45]. Interoperability is a primary or essential component of bor derless smart grid networks, it is to be prote cted with solid and strong cy ber security. 8. Gap analysis : Undiscovered inf orm ation security gaps are able to be distinguished and palliated by integrating bot h electronic and physical inform ation components [46][47]. 9. Reliable data storage system : In a ccompaniment with the establishm ent of grid environments [48], various assurances were established virtually. These depict where t he end-user is concerned over grid se rvices that are hosted on hi gh- end resources including high-priced instrum entation and data storag e systems, c onnected via reliable an d hig h- speed networks. 10. Cybersecurity guidelines : Some federal government agencies ha ve developed, and are currently developing more security guidelines and be st practices for smart grid [49]. Testimony a rgues that technology is growing progressively as pot ential in strum ent for terrorist organizations. This extend to t he outgrowth of a new threat in the f orm of cyber terrorists. Cyber terrorists attack te chnological features such as the Internet in order to help foster their cause [ 50]. Hence, the nature of the responses in term of nec essary to preserve the future security of our society becom e prior to action. 11. Law enforc ement : When the publi c sharing of info rmation abo ut a specific l ocation ‟ s energy used [5 1][52] is a lso a distinct possibility, law enf orcement plays a mighty significant role, particularly when the c oncern exists that the prevalence of granular e nergy data could lead to actions o n the part of law enforcem ent. 12. Improved wireless technology : Community benef its e ase of cost savings [53], flexibility and deploy ment along with the es tablishment of wireless communications. However, wi th the existing of wire-line or wireless networks [54], immediate concern revolves around the security pr otections for easily a ccessible devices such as t he meters an d the related communications hardware. A man-in-the-m iddle att ack exploites a wireless communication network armless with proper security pro tocols. 13. Controlled power consumption : Power consumption is affected by t he program [5 5] running on a microprocessor [56] . Low and high- level language optimization techniques appear as an alternative in l ow power consumption analysis [57][58]. 14. Protect secret : Protecting secret [59] has been identifies as one of the eight objectives of Commercial Inform ation Systems Se curity. Some data and information ar e categorized secret and required unique or specific password login access t o be obtained, read or copied where [ 60] access to these areas of the ne twork resources needs authentication o f the user nodes and the associated controls. International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 11 15. Cryptographic protocols : Cryptographic algorithms are ne cessitated to convert plaintext into ciphertext and v ice versa [61]. The conver tion of plaintex t into ciphertext makes it impossible for an attac ker to po ssess plaintext fr om a ci phertext without c ognizing a key. It is a sequence of bits an d serves as a parameter for t ransform ation. In the area aiming to provide secure authentication and communication service negotiation in online presence notification systems [62], C ryptography practice is [63][64] beneficial to be employed. 16. Encryption policies : It is relatively well known that the encryption policies such as encrypting sensitive data that is either at rest in databases or in motion such as portable devices, emails and i nstant messages [65] can help to minimize the probability of insider ‟ s misuse. Technical c ontrol against [66] i nsider attacks ought to be made up out of encryption. Smart grid function al r equirem ents, i nteroperabilit y and c ybersecurity st andards are still evolving, beside s aiming t o pre vent it from cyber- security threats, this set of information security functional requirements also pla y a significant r ole specifically to address secur ity concerns t hat would arise from the t ransform ation to a smart grid system. We s hould understand not on ly the technical but also the legal, policy and social requirements of cyber securi ty. 7. FUTURE RESEARCH DIRECTION The matching of consumer requirement and functional requirement of information security o f the smart grid prevail an interesting sight for future research development. When comes to discover the relationship between information security with customer trust and satisfaction, it is interesting to prove that there is a relationship between consumer requirement and the functional requirem ent of t he information security criteria in a smart grid tha t would impact consumer ‟ s trust and satisfaction towards the e ntire system, as in Table III below. The future work intends t o prove that there is a significant positive relationship between the said elements with the help of fuzzy logic value which would serve to eliminate a mbig uity duri ng data insertion and validation. Cx r epresents customer trust; Sx represents c ustom er satisfaction; Iy represents information security; when the value o f Sx and Cx on the Xs,c increase, the Iy also will increase at a different pace form ula on Yi. International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 12 Table 3. Relationship Graph It takes aim to reveal the significant information security criteria in a smart grid that would impact consumer trust and satisfaction towa rds the entire system . 8. CONCLUSION This paper review previous literature on smart grid information technology and the needs for smart grid information security . Then, the concept herm eneutic circle of the paper m ethodology is presented. T he Hermeneutic Circle is indeed a good methodology applied in th is paper as it gives the entire mapping of this study where the functional requirement could be identified one by one. Networking trend successfully elucidate the significant of information security as in T able 1 that leads to the generation idea of working on the c ollection of da ta regarding inf orm ation security functional requirement identi fication showed detailed in Tabl e 2. Sixteen identified inform ation security functional requirement were dev eloped with the support of facts and references. This set of grid i nformation security functional requirements defined the approach and s erve as a base for t he information security p olicy developers and utilities to r efer as a basic functional re quirem ent t o satisfy consumer t rust and satisfaction. Because a smart grid utilizes digital technology to provide two-way communication between suppliers and consumers ‟ home electronics t hrough the use of smart meters, information se curity protection measures need to be consumer friendly and practicable t o be implemented on all level within a community or organization, making it more reliable, energy- efficient, and better able to serve all needs. This pa per has tutorial contents where s ome related backgrounds were provided, especially for networking community, covering the cyber security r equirement of smart grid information infrastructure. It provides a methodology and some information security functional requirements conceptually a s original contributions. This paper aims to contribute a sight for the readers to have a functional knowledge of the electric power grid and a be tter understanding of cyber security. International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 13 ACKNOWL EDGEM ENTS The authors wish to t hank Program GCOE, Grad uate School of Science and Technolo gy Meiji University and t he Japanese Government Scholarship (MONBUKAGAKUSHO: MEXT) f or the sponsor, Professor Mimura Masayasu and Professor Sugihara K okichi from GCOE Program of Meiji Uni versity for the mentor. T he authors also express gratitude t o Dr. Zainol Mustafa and Dr . Rika Fatimah from Sch ool of Mathematical Sciences National University of Mala ys ia for discussion and ideas. REFERENCES [1] Christop h W eber, Adriaan Per rels, (2000) “Mode lling lifes tyle e ffects on energ y de mand a nd related emissions”, E nergy Polic y 28, pp. 549-56. [2] I nge Røp k, ( 2001) “New technolo gy in ever yday li fe – so cial processes and en vironmental i mpac”, Ecological E conomics 38, pp. 403–42 2. [3] Ryan Hled i, (2009) “How Green Is the S mart G rid?”, The Electricity Journal, Volume 22, Issue 3 , April, pp. 29-41. [4] Pe ter Crossley, Agnes Beviz, (201 0) “Smart ener gy systems: Tr ansitioning re newables o nto the grid”, Rene wable Energy Fo cus, Volume 11 , Issue 5, Sep tember-Octob er, pp. 54-56, 58 -59. [5] James He idell, H arold W are, (2 010) “Is T here a Case for Broad band Utilit y Co mmunications Networks? Valuing a nd Pricing I ncremental Communica tions Capac ity on Ele ctric Uti lity Smart Grid Net works”, The E lectricity Journal, V olume 23, Issue 1, J anuary-Februar y, pp. 21-33 . [6] P ertti Jär ventausta, Sa mi Repo, Antti Rautiaine n, Ja rmo P artanen, ( 2010) “Smart grid po w er system control in d istributed generatio n en vironment”, Annual Reviews in Control, Volume 34, Issue 2 , December, pp. 277-28 6 [7] Matthias W issner, (2010) “ICT, growth and pro ductivity in the G erman e nergy sector – O n the way to a s mart grid?”, Utilities Polic y, availab le at http ://www.sciencedir ect.co m /scie nce? _ob=MI mg &_imageke y=B6VFT-50S2 D6F-1-C&_cd i=6019 &_user=2043 47&_pii =S0957 17871000041 X&_origin=search&_zo ne=rslt_lis t_item&_coverDa te=08/12 /2010&_sk=999 9 99999& w chp=d GLbVzb-zS kzV& md5=1d 826a4 d64e9dd061 0b53b5b71ee4 884&ie=/sdarticle. pdf [8] R. Star k, H. Hayka, D. Langenberg, (20 09) “Ne w p otentials for virtual pro duct creation b y utilizing grid technolo gy”, CIRP An nals - Manu facturing Te chnology, Vo lume 58, Issue 1, Pages 143 -146. [9] T ony Flick, J ustin Mor ehouse, (20 11) “State and Local Securit y Initiatives”, Securin g the S mart Grid , pp. 73-84 . [10] Jean-Philipp e Vasseur, Ada m D unkels, (201 0) “Smart Grid”, Interc onnecting S mart O bjects with IP, pp. 305 -324.9 International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 14 [11] Leonard o Meeus, Marcelo Sagua n, ( 2011) “Innovating grid regulatio n to r egulate grid innovatio n: From the O rkney Isle s to Kriegers Flak via I taly”, Rene wable Energ y, Volu me 3 6, Issue 6 , June 2011 , pp.1761-1765. [12] Tony F lick, Justin Moreho use, (2011) “Federa l Effort to Secure Smart Grids”, Securing the Smar t Grid, p p. 49-72. [13] To ny Flick, Justin Morehouse, (2 011) “Attackin g S mart Meters”, Sec uring the Sma rt Grid, pp. 2 11- 232. [14] Ravi Akella, Han T ang, B ruce M. McMillin, (201 0) “Analysi s of i nformation flow security in cyber – physical systems”, I nternational Journal o f Critical Infrastr ucture P rotection, Volume 3 , Issues 3-4, December 2 010, pp . 157-173. [15] G. Laccetti, G. Schmid, (2007) “A framework mo del for grid security”, Future Ge neration Computer Systems, Vo lume 23, I ssue 5, June 200 7, pp.702-71 3. [16] Simon P err y, (2009 ) “W att matters – smart grid se curity”, Infosec urity, Vo lume 6, Issue 5, Ju ly- August 20 09, pp. 38-40 . [17] Klein, H.K., Myers, M.D ., (1999) “A set of pri nciples for co nducting and e valuating interpretive field studies in in formation s ystems”, MIS Q uarterly, Vol. 2 3 pp.67-94 . [18] Walsha m, G. , (19 96) “The emergence of interpre tivism in I S researc h”, In formation S ystems Research, Vol. 6, pp. 376-94. [19] Mautner, T., (1996) A Dictionar y of Philosop hy, Blackwell, O xford. [20] Ramberg, Bjø rn and Kristin Gj esdal (2005 ) “Hermeneutics”, Sta nford Enc yclopedia of P hilosophy,. [21] Ment, (2003) “Outline/ Research P aper Guideline”, THEA 28 0, 4/9/0 3, available at http://www.kzo o.edu/is/libr ary/ course_ guides/thea_28 0/thea_28 0_paper_guide.p df [22] Tony Flick, Justin Mor ehouse, (2 011) “Social Networking and t he Smart Grid ”, Securing t he Smart Grid, p p. 195-210. [23] Dong-Hee S hin, (201 0) “The e ffects o f trust, sec urity and p rivacy i n social net working: A securi ty- based approach to understand the pattern o f adoption”, Interacti ng with Co mputers, Volume 22, Issue 5, Septe mber 201 0, pp. 428-43 8. [24] Bill Blessi ng, “Smart Grid Networking”, Smart Gr id Strate gy, Burns & Mc Donnell, (2010 ) available athttp://www.b urnsmcd.c om/portal/page/p ortal/Internet/Co ntent_Ad min/Publications%2 0Repo sitory /Others%20 Link%20Repo sitory/WhiteP aper-Smart -Grid-Net w orking -March-201 0-Blessing.pd f International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 15 [25] XiaoHe, (2011) “Future networ k trends: Wisdom and superconducti vity – power, wisdom, and superconducti vity – Electrical Ind ustry”, Article Pro s, P ress Release Jan 2011 , available at http://www.art iclepros.co m/business/C hinese-Marketin g/article-663 253.html [26] J oshua Z. Ro kach, (20 10) “Unlockin g the S mart Grid ”, The Electricit y J ournal, Vo lume 2 3, Issue 8, October 2010, pp. 63 -71. [27] Eric Miller, ( 2009) “Renewables and the s mart grid ”, Renewable E nergy Focus, Vo lume 10 , Issue 2, March-April, p p. 67-69 . [28] Ashley Brown, Raya Salter, (2011 ) “ Can Smart Grid Technolog y Fix the Disco nnect Between Wholesale and Reta il P ricing?”, T he Ele ctricity Journal, Availab le o nline 22 Januar y 201 1 Link:http:// www.sciencedirec t.com/scie nce?_ob =MImg&_imageke y=B6VSS-52 0V41P - 1&_cdi=6 270&_user=2 04347&_pii= S1040 61901000 312X&_origin=searc h&_zone=rsl t_list_item &_coverDate=0 1/22/2 011&_sk=9999 99999&wchp=dG LbVzbzSkzV &md5=d67 27f9710915 36b30c 10cfe 5b aee99a&ie=/sd article.pdf [29] Hung-po Ch ao, (2010 ) “Price- Responsive Demand Manageme nt f or a Smart Gr id World”, The Electricit y Journal, Volu me 23, Issue 1 , January-Februar y 2010 , pp. 7-20. [30] Amy A.L.Poh, M. Mukaido no, (2011 ) “Selection of model in developing Info rmation Security Criteria on Smar t G rid Security S ystem”, Smart Grid Security and Co mmunicatio ns, The 9th International Symposiu m on Par allel and Distrib uted Pr ocessing with Applications ( ISPA 201 1), #108 . [31] Graham Co llie, (1995) “Information Privac y”, Infor mation Ma nagement & Computer Security, Vol. 3 No. 1, pp. 41-45 . [32] C. Cachin et al, ( 2000) “Reference model and use cases, MAFTIA de liverable D1”, M AFTIA Pr oject IST-19 99-11583. [33] FIP S P UB 1 99, ( 2001) “Standards for Securi ty Categor ization o f Federal Infor mation and Information Systems”, Federa l Information P rocessin g Standard s Publicatio n, Feb 20 04, p p. 2, available at ht tp://csrc.nist. gov/publication s/fips/fips19 9/FIPS-PUB-19 9-final.pdf [34] Marco Vieir , Jorge Vieir, Henriq ue Madeir, ( 2008) “To wards Data Securit y in Afford able Data Warehouses”,a vailable at http://solutio ns.criticalsoftwar e.com/upload _prod uct/wp/Towards_Data_Se curity_in_ Affordab le_Da ta_War ehouses.pdf [35] Cushing Anderson, (20 07) “Informatio n Sec urity a nd Availabilit y: T he Impact of T raining on IT Organizational Perfor mance”, White Paper, #20692 , pp. 2, available at http://eval.sy mantec.com/do wnloads/edu/I mpact_of_T raining_on_Or ganizational_P erformance.pd f International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 16 [36] “Trust Service s, P rinciples, Cr iteria and Illustratio ns”, T rust Service s Princip les, Cr iteria and Illustrations for Securit y, Availabilit y, Pro cessing Integrity, Co nfidentiality, and P rivacy, May 2006 , pp.18 -20, available at http:// www.webtr ust.org/principle s-and-criteria/ite m27818.p df [37] “Infor mation Securit y Levels by Infor mation Categor ies”, CMS Infor mation Securit y Levels, September 2 7, 2002 , Version 1.0, available at http:// www.iwar.org.uk/co msec/reso urces/fasp/ssl.pd f [38] Isaac Ghansah et al, (2010 ) “R&D Ide as for S mart Gr id Cyber Security”, Januar y 20, 2010 , pp. 2-3, available at http://coll abora te.nist.gov/twiki-s ggrid/pub/S martGrid/CSCT GRandD/RDId eas- Jan15_ 2010.pdf [39] Menezes, P. V. Oorschot, and S. A. Vanstone, (1997) “handb ook of A pplied Crypto graphy”, CRC Press, Ne w York. [40] Anil Kapil, Sanjeev R an, (2009) “Identit y-Based Key Manage ment in MANETs using Public Key Cryptograph y”, International J ournal o f Security (IJ S), Volume (3 ) : Issue (1). [41] Erik Zenne, ( 2007) “Cr yptography and Key Manage ment Basics”, Cr yptography a nd Ke y Management B asic, DT U, Oct. 23 , pp.15-21. [42] Rahul Banerj ee, (2006) “ Introductio n to the System-level Elements of Networ k Se curity S ystems”, Lecture 7. [43] NISTIR 762 8 Guidelines for S mart Grid Cyber Se curity: Vo l. 1, Smart Gr id C yber Security Strategy, Architecture, and High-Level Require ments, T he Smart Grid Interoper ability Panel – C yber Securit y Working Group, pp . 76, availab le at http://c src.nist.gov /publicatio ns/nistir/ ir762 8/nistir- 7628_vol1 .pdf [44] Andrew K. Wrigh, Paul Kal, Rodrick Siber, (20 10) “Interoperab ility a nd Security for Converged Smart Grid Net w or ks”, Grid-Interop Forum 2010, available at http://www.grid wiseac.o rg/pdfs/forum_p apers10/ wrigth_gi10.pd f [45] “S mart Grid I nteroperab ility P anel - Cyber Security Wo rking Group Standa rds Review”, Phase 1 Report October 7, 201 0, availab le at http://collabor ate.nist.gov/t wiki-sggrid/pub/S martGrid /CSCTG Standards/Sta ndardsRevie wPhase-1Repor t.pdf [46] Ray B ernar, (2007) “Information Lifecycle Security Risk Asse ssment: A too l for closing sec urity gaps”, Co mputers & Sec urity 26, pp. 26–30 [47] “Over view of Stra tegic Suppor t (SSA)”, Sapp hire Strategic Suppo rt Agreement ( SSA), J an (2011), available at ht tp://www.sap phire.net/strate gic-suppo rt-ssa-5/over view-25.html International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 17 [48] Konstanti nos Tserpes, D imosthenis Kyriaz is, Andre as Menychtas, T heodora Varvarigo, (2 008) “A novel m echa nism for provisionin g of hig h-level qua lity of service i nformation in grid environment s”, European J ournal of Oper ational Researc h 191, pp. 1113–113 1. [49] White Paper, ( 2009) Cyber Security For Smart Grid System, pp.9, available at http://www.ae sieap0910 .org/upload /File/PDF/4-Te chnical%20 Sessions/ TS18 /TS1806/TS180 6_FP.pdf [50] Tony F lick, Justin Moreho use, (2011) “Federa l Effort to Secure Smart Grids”, Securing the Smar t Grid, p p. 49-72. [51] S. M. Furnell, M. J. Warren, (1999) “ Computer hacking and cyber terr orism: t he real threats in th e new millenni um?” Computer s & Securi ty, Volume 18 , Issue 1, pp. 28 -34. [52] BA Akyol, H Kirkham, SL Cle ments, MD Hadle, (2010) “A Survey o f Wireles s Communicatio ns for the Electric Power Syste m”, Prep ared for the U. S. Department o f Energy under Contract DE- AC05- 76RL0183 0, January 201 0, available a t http://epic.o rg/privacy/s martgrid/EPIC_Sta tement_ Smart_Grid_ Summit_Cyber security_a nd_Privac y.pdf [53] BA Akyol, H Kirkham , SL Cle ments, MD Hadle, (2 010) “A S urvey of Wirele ss Co mmunications for the Electr ic Po wer S ystem”, Prep ared for the U.S. De partment o f Ener gy under Contra ct DE - AC05-76R L01830, January 2010, available at http://www.pnl.gov/ nationalsecurit y/technical/sec ure_cyber_s ystems/pdf/po wer_grid_ wireless.pdf [54] Jeff McCullou g, (201 0) “LAN co mmunication attack pr evention”, AMI sec urity consid erations, pp.2, available at http:// www.energyax is.com/pdf/WP 42-1007 B.pdf [55] Kunl un Ga et a l, (20 10) “A cyber securi ty solution for inter net of t hings for smart grid”, ava ilable athttp://www.a esieap091 0.org/upload/File/P DF/4Tec hnical%20Sessions/T S46/T S4602/TS460 2_FP. pdf [56] David A. Ortiz, Na yda G. Santiag, (2007 ) “High-Level Op timization for Low Powe r Consumptio n on Microp rocessor-Based Systems”, Circuits and Syste ms. MWSCAS 20 07. 5 0th Midwest Symposiu m on 5-8 Au g. 2007, pp. 1265 – 126 8. [57] V. Dalal and C .P. Rav ikumar. (2001 ) “Software power opti mizations in an embe dded sy stem”, Fourteenth Inter national Con ference on VL SI Design, Jan, pp. 254 – 259 . [58] J. Oliver, O. Mocanu, and C. Fer rer. ( 2003) “Energy awarene ss throu gh soft ware op timization a s a performance e stimate ca se study of the MC68 HC908GP 32 microcontroller, ” 4th I nternational Workshop on Micro processor T est and Verification: Common Challenges and Solution s, May. pp. 111 – 1 16. International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 18 [59] Vasilios K atos, Carl Adams, (200 5) “Modeling cor porate w ireless sec urity and p rivacy”, Journa l of Strategic Infor mation Syste ms 14 , pp. 307–32 1. [60] Okechukwu E. Muo gilima, K ok-Keong Loo, Richard Comle, (20 11) “Wireless mesh network security: A tra ffic engineer ing ma nagement app roach”, J ournal of Network a nd Computer Applications 3 4, pp. 478–491. [61] Denis T r č ek, (2 003) “An i ntegral frame work for infor mation systems securit y manage ment”, Computers & Security Vol 2 2, No 4 , pp 337-36 0. [62] A.C.M. Fo ng, S.C. Hui, C.T. Lau, ( 2001) “T owards an op en p rotocol for secure online presence notification”, Co mputer Sta ndards & Inter faces 23, pp. 311–324 . [63] B. Schneier, (1996) “App lied Cryptograp hy: P rotocols, Algorithms, and So urce Cod e in C. Wile y”, USA,. [64] SSH Communicatio ns Securit y, Cryptograp hic Algorith ms, (200 1) available online at http:rrw ww.ssh.firtechrcr yptor algorith ms.html. [65] K uheli Ro y Sarka, (2 010) “Assessi ng i nsider thre ats to informatio n sec urity usin g tec hnical, behavioural a nd organisationa l measures”, i nformation sec urity technica l repor t, pp. 1-22. [66] Car l Col wil, ( 2009) “Human factors in i nformation securit y: T he insider t hreat e Who can you trust these days? ”, Informatio n security tech nical report 14, pp. 186-19 6. International J ournal of Grid Computin g & Applicatio ns (IJGCA) Vo l.2, No. 2, June 2011 19 Author 1 Amy P oh Ai L ing was a m ember of The Natio nal Univ ersity of Malays ia (UKM) Fellowship stationed in Ibrahim Yaakub R esiden tial College. Upo n completing her Master i n Scie nces (MSc) in Qualit y a nd P roductivity Improve ment under Mathemat ical Science s Depar tment of UKM, she bec ame a Parts Quality Ass urance (Elec tronic) Engi neer in EMCS Son y. C urrently she is attaching with MIM S P h.D. P rogram in Meij i Universit y, Japan w ith MEXT scholarship awarded. The author always has an e nthusiasm for m athematical quality and sa fety studies. Author 2 Mukaidono Masao served as a full-time lecturer at Faculty of Engi neering, Depart ment of Electrical Engineerin g in Meiji University from 1970. Even since t hen, he was pro moted to Assistant Pr ofessor on 1973 and as a Pr ofessor on 197 8. He contributed as a resea rcher in an Elec tronic Tec hnical Laborato ry of the Ministr y of Internat ional Trad e a nd I ndustry ( 1974), Institute o f Mathematical Anal ysis of Kyo to Universit y (1975 ) and as a visiting researc her at Univer sity of Califor nia in Ber keley (197 9). He then became the Directo r of Computer Center (1 986) and Direc tor of Infor mation Cente r (198 8) in Meiji University. At p resent, he is a Pro fessor and De an of the School of Scie nce & Technolo gy, Me iji Univer sity. He is also t he ho nourable Councillor of M eiji University
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment