An Anonymous Authentication and Communication Protocol for Wireless Mesh Networks
Wireless mesh networks (WMNs) have emerged as a key technology for next generation wireless broadband networks showing rapid progress and inspiring numerous compelling applications. A WMN comprises of a set of mesh routers (MRs) and mesh clients (MCs), where MRs are connected to the Internet backbone through the Internet gateways (IGWs). The MCs are wireless devices and communicate among themselves over possibly multi-hop paths with or without the involvement of MRs. User privacy and security have been primary concerns in WMNs due to their peer-to-peer network topology, shared wireless medium, stringent resource constraints, and highly dynamic environment. Moreover, to support real-time applications, WMNs must also be equipped with robust, reliable and efficient communication protocols so as to minimize the end-to-end latency and packet drops. Design of a secure and efficient communication protocol for WMNs, therefore, is of paramount importance. In this paper, we propose a security and privacy protocol that provides security and user anonymity while maintaining communication efficiency in a WMN. The security protocol ensures secure authentication and encryption in access and the backbone networks. The user anonymity, authentication and data privacy is achieved by application of a protocol that is based on Rivest’s ring signature scheme. Simulation results demonstrate that while the protocols have minimal storage and communication overhead, they are robust and provide high level of security and privacy to the users of the network services.
💡 Research Summary
Wireless Mesh Networks (WMNs) have become a promising backbone for next‑generation broadband services, yet their peer‑to‑peer topology, shared wireless medium, limited node resources, and highly dynamic environment expose them to a wide range of security and privacy threats. This paper presents a comprehensive security and privacy framework that simultaneously addresses authentication, confidentiality, and user anonymity for both the access segment (mesh clients to mesh routers) and the backbone segment (mesh routers to Internet gateways).
The access layer adopts the conventional LAN‑style 802.11 authentication process, allowing mesh clients (MCs) to associate with a mesh router (MR) without any additional software. To protect the wireless link, a stream cipher is applied at the data‑link layer, providing real‑time encryption with negligible processing delay.
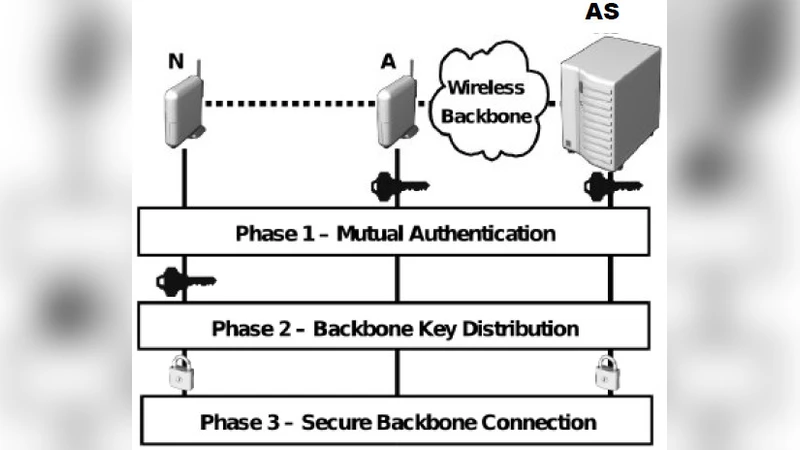
For the backbone, a two‑phase authentication is introduced. When a new MR joins the network, it first performs the same 802.11i mutual authentication as an MC, establishing a secure local channel. Afterwards, the MR engages in a TLS‑based authentication with a central Authentication Server (AS). Each MR holds two certificates issued by the same Certificate Authority: one for the initial association and another for the subsequent backbone authentication. Successful TLS hand‑shake yields a secure tunnel for exchanging cryptographic credentials.
User privacy is achieved through an anonymous authentication scheme built on Rivest’s ring signature. A client can generate a signature that proves membership in a predefined “ring” of users without revealing its exact identity. Verifiers can only confirm that the signature originates from some member of the ring, thereby preserving anonymity while still guaranteeing authentication.
Key management is handled by a server‑initiated key distribution protocol. The AS periodically (per session) broadcasts a key list together with a timestamp (TS_KL). All MRs synchronize their clocks via NTP and use the received key list for the duration of the session. At the end of a session, the old keys are revoked and a fresh key list is generated, preventing long‑term key reuse. This approach minimizes storage overhead (a single key list per MR) and reduces the number of round‑trip messages needed for key refresh.
Simulation experiments evaluate storage and communication overhead, end‑to‑end latency, and packet loss. Compared with existing WMN security solutions, the proposed protocol shows only marginal increase in latency while achieving a high level of confidentiality and anonymity. The ring‑signature based anonymity incurs only a modest computational cost, making it suitable for real‑time applications.
In summary, the paper delivers a unified, low‑overhead security architecture for WMNs that protects data integrity and confidentiality across both access and backbone layers, while simultaneously providing strong user anonymity. Future work is suggested on extending the design to multi‑radio, multi‑channel WMNs and on optimizing the ring‑signature algorithm for even lighter mobile devices.
Comments & Academic Discussion
Loading comments...
Leave a Comment