Direct Sequence Spread Spectrum Steganographic Scheme for IEEE 802.15.4
This work addresses the issues related to network steganography in IEEE 802.15.4 Wireless Personal Area Networks (WPAN). The proposed communication scheme employs illicit Direct Sequence Spread Spectrum code sequences for the transmission of steganographic data. The presented approach is a compromise between minimising the probability of covert channel disclosure and providing robustness against random errors and a high steganographic data rate. The conducted analyses show that it is possible to create a covert channel with a data rate comparable to the raw data rate of IEEE 802.15.4 without much impact on the perceived receiver sensitivity, the Chip Error Rate and the Bit Error Rate.
💡 Research Summary
The paper addresses covert communication in IEEE 802.15.4 wireless personal area networks by exploiting the Direct Sequence Spread Spectrum (DSSS) coding used at the physical layer. Existing steganographic approaches either modify PHY header fields, use energy‑sensing tricks, or tamper with the 16 standard 32‑chip DSSS sequences. While the latter offers the highest bandwidth, it typically degrades the underlying link performance because the altered chips increase the bit error rate (BER) and reduce receiver sensitivity.
The authors propose a balanced method that maximizes the minimum Hamming distance between the legitimate code set and the covert code set, thereby preserving error‑correction capability while still providing a high covert data rate. In IEEE 802.15.4 each 4‑bit symbol is mapped to a 32‑chip pseudo‑random sequence. The standard set was designed with a minimum Hamming distance d_min = 12, average distance ≈ 17.1, and maximum distance 20, ensuring robustness against random noise.
The new scheme selects up to ⌊(d_min‑1)/2⌋ = 5 chips per 32‑chip sequence to flip. Each distinct pattern of flipped chips encodes a covert symbol; with 5 flipped chips there are C(32,5) ≈ 201 376 possible patterns, but the authors restrict the alphabet to a manageable size (e.g., 32 patterns) to keep decoding simple and error‑resilient. The flipped‑chip positions themselves carry the secret payload.
To hide the presence of these modifications, the covert symbols are scrambled using a pseudo‑random permutation generated by a linear feedback shift register (LFSR) seeded with a shared secret key k. The receiver, possessing the same key, reverses the permutation to recover the original covert data. Key rotation is suggested to increase security, though key distribution is not detailed.
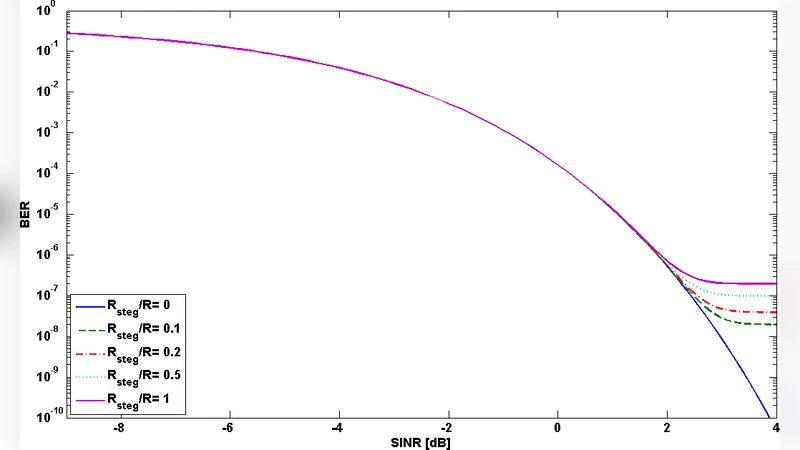
Performance analysis quantifies the impact of the covert channel on the legitimate link. Assuming a constant probability p = 5/32 of a chip being altered, the average Hamming distance between two random codes decreases by Δ\bar d ≈ p·\bar d ≈ 0.93. Using standard coding‑gain formulas, the authors estimate the increase in BER (ΔBER) and the corresponding shift in the probability of symbol misinterpretation (ΔPm). Simulations show that for signal‑to‑noise ratios (SNR) up to 4 dB, the BER increase remains below 10⁻⁶, essentially indistinguishable from normal operation. The effective reduction in receiver sensitivity is bounded by about 15 dB, well within the typical -85 dBm sensitivity requirement for the 2.4 GHz PHY.
Crucially, the covert channel can transmit 4 secret bits per 32‑chip sequence, yielding a covert data rate equal to the raw IEEE 802.15.4 rate of 250 kb/s (R_steg = R). This matches the raw throughput while imposing only negligible degradation on the legitimate traffic, outperforming earlier proposals that either sacrificed link quality for higher covert bandwidth or offered low covert bandwidth to preserve link quality.
The paper concludes that by carefully selecting the number and pattern of flipped chips and by scrambling them with a secret key, a high‑throughput, low‑detectability covert channel can be realized in IEEE 802.15.4 networks. Future work is suggested on robust key‑management protocols, multi‑node coexistence, and real‑world hardware validation.
Comments & Academic Discussion
Loading comments...
Leave a Comment