Is Cloud Computing Steganography-proof?
The paper focuses on characterisation of information hiding possibilities in Cloud Computing. After general introduction to cloud computing and its security we move to brief description of steganography. In particular we introduce classification of steganographic communication scenarios in cloud computing which is based on location of the steganograms receiver. These scenarios as well as the threats that steganographic methods can cause must be taken into account when designing secure cloud computing services.
💡 Research Summary
The paper investigates the feasibility and implications of using steganography—covert information hiding—in cloud computing environments. After a concise overview of cloud computing fundamentals, the authors reference the NIST definition and outline the three primary service models (IaaS, PaaS, SaaS) together with the characteristic properties of on‑demand self‑service, broad network access, resource pooling, rapid elasticity, and measured service. They then enumerate the principal security challenges unique to the cloud: ensuring authorized data access, sharing responsibility between provider and customer, and guaranteeing secure multi‑tenant isolation.
Building on the Cloud Security Alliance’s “Top Threats to Cloud Computing” (seven categories), the paper distinguishes between well‑known threats (abuse, malicious insiders, data loss/leakage, account hijacking, insecure APIs) that can be amplified in a cloud context, and cloud‑specific threats (shared technology issues and unknown risk profiles) that exploit the inherent multi‑tenant, shared‑infrastructure nature of cloud platforms.
The core contribution lies in mapping steganographic communication onto these cloud threat vectors. The authors first describe the essential requirements for a good steganographic carrier: it must be widely used (so its traffic does not appear anomalous) and any modifications introduced by embedding secret data must be invisible to third‑party observers. They argue that modern cloud services—such as Gmail, Azure, Amazon Web Services, and WebEx—are prime candidates because they generate massive, heterogeneous traffic and often employ complex protocols.
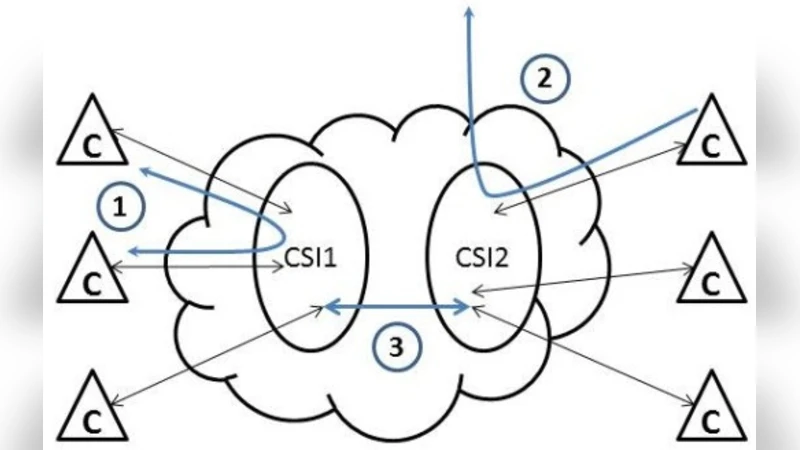
Based on the location of the steganogram receiver (SR), three distinct scenarios are proposed:
-
Same‑instance communication – Both sender (SS) and SR reside within the same virtual machine or cloud instance. Hidden data is transmitted via network steganography (e.g., manipulating protocol fields, timing, or packet ordering). This scenario can directly realize Threats #1‑3 (abuse, insider activity, data leakage).
-
External receiver – SR is located outside the cloud, while the cloud service is used as a covert channel to coordinate attacks (e.g., botnet command‑and‑control). Network steganography again serves as the carrier, leading to the same set of threats (#1‑3).
-
Cross‑instance communication – SR resides in a different cloud instance than SS. Here the covert channel exploits shared physical resources such as CPU caches, memory deduplication, or storage deduplication mechanisms. Prior work on side‑channel leakage (e.g., deduplication attacks, cache‑based covert channels) is cited to illustrate feasibility. This scenario can trigger Threats #1‑3 and additionally Threat #7 (unknown risk profile) because the interaction spans distinct tenants whose relationship may be opaque to the provider.
Figure 1 (referenced in the text) visualizes these three scenarios, emphasizing how the cloud’s “service instance” (CSI) and “cloud client/customers” (C) interact in each case.
In the concluding section, the authors argue that, from a steganographic perspective, cloud platforms are not fundamentally different from traditional carriers such as IP telephony; the novelty lies in enabling secret communication between separate cloud service instances. Consequently, steganography should be treated as a rising threat within cloud security threat modeling. They call for the development of effective steganalysis (detection) techniques that are deeply informed by the specific functionality of each cloud service. However, given the heterogeneity and rapid evolution of cloud offerings, the authors express skepticism about the feasibility of a universal detection solution, advocating instead for service‑specific research and possibly standardization efforts.
Overall, the paper provides a taxonomy of cloud‑based steganographic channels, links them to established cloud threat categories, and highlights the need for dedicated countermeasures in future cloud security architectures.
Comments & Academic Discussion
Loading comments...
Leave a Comment