How Hidden Can Be Even More Hidden?
The paper presents Deep Hiding Techniques (DHTs) that define general techniques that can be applied to every network steganography method to improve its undetectability and make steganogram extraction harder to perform. We define five groups of techniques that can make steganogram less susceptible to detection and extraction. For each of the presented group, examples of the usage are provided based on existing network steganography methods. To authors’ best knowledge presented approach is the first attempt in the state of the art to systematically describe general solutions that can make steganographic communication more hidden and steganogram extraction harder to perform.
💡 Research Summary
The paper introduces a novel meta‑level concept called Deep Hiding Techniques (DHT) that can be applied to any network steganography method to increase its undetectability and make extraction of the hidden payload more difficult. The authors argue that traditional network steganography is constrained by a trade‑off between steganographic bandwidth and detection risk, and that existing methods rarely consider systematic ways to deepen the hiding process. To address this gap, they define five broad categories of DHT, each affecting either the steganogram itself or the carrier.
-
Steganogram Scattering (SGS) – The hidden message is split into multiple fragments and transmitted over separate flows, separate hosts, or a hybrid of both. By using multiple TCP/UDP connections (flows) or multiple physical/virtual devices (hosts), the approach reduces reliance on any single channel and adds resilience against flow blocking or packet loss. The paper discusses ordering mechanisms (explicit position tags, timing‑based ordering, or pre‑assigned flow numbers) required for correct reassembly at the receiver.
-
Steganogram Hopping (SGH) – Within a single overt connection, the steganographic method is periodically switched. The authors illustrate this with SCTP, where three distinct encoding schemes (IP‑address‑based, stream‑based, and chunk‑count‑based) are alternated. Detecting such a connection requires a more detailed statistical analysis of multiple SCTP dimensions, making detection and extraction considerably harder than when a single method is used throughout.
-
Carrier Modifications Camouflage (CMC) – This group focuses on disguising the presence of the steganogram inside the carrier. Techniques include reducing the insertion frequency (lowering effective bandwidth), dynamically adjusting method parameters (e.g., number of packets N and number of TCP flows X in the Cloak method), aligning traffic generation with typical user patterns (time‑of‑day, call length for LACK), and exploiting normal network anomalies (intentional retransmissions in RSTEG, Ethernet frame padding in PadSteg) to hide payloads within expected protocol behavior.
-
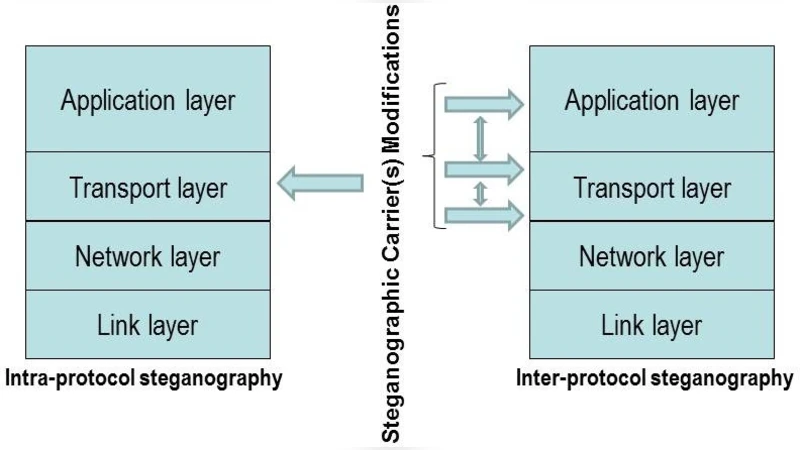
Inter‑Protocol Steganography (IPS) – Instead of modifying a single protocol, IPS exploits relationships between two or more protocols to convey hidden data. The PadSteg example demonstrates how Ethernet frame padding, ARP, TCP, UDP, and ICMP can be combined so that the presence of a steganogram is signaled only when a specific upper‑layer protocol is observed. The concept of “carrier‑protocol hopping” further diversifies the observable patterns, forcing an adversary to monitor multiple protocol layers simultaneously.
-
Multi‑Level Steganography (MLS) – MLS builds a second, lower‑level steganographic channel on top of an existing (upper‑level) one. The upper‑level method carries overt traffic, while the lower‑level method uses the operational characteristics of the upper‑level method (e.g., timing, packet ordering) as its carrier. Consequently, the lower‑level bandwidth is a fraction of the upper‑level bandwidth, but its detection is substantially harder because it is entirely dependent on the upper‑level behavior.
For each DHT category, the authors provide concrete usage scenarios based on known steganographic schemes such as Cloak, LACK, RSTEG, and PadSteg, illustrating how the techniques can be combined with existing methods. A comparative table highlights differences between traditional steganography features and those introduced by DHT, emphasizing improvements in stealth, resilience, and implementation complexity.
In summary, the paper presents DHT as a systematic framework for “deepening” network steganography. By distributing the hidden payload across multiple flows/hosts, periodically changing the encoding method, camouflaging carrier characteristics, leveraging inter‑protocol relationships, and nesting steganographic layers, DHT significantly raises the bar for detection and extraction. The work constitutes the first comprehensive attempt to catalog general, protocol‑agnostic enhancements that can be applied to any network steganographic scheme, offering a valuable reference for researchers aiming to design more robust covert communication systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment