Sending Hidden Data via Google Suggest
Google Suggest is a service incorporated within Google Web Search which was created to help user find the right search phrase by proposing the autocompleting popular phrases while typing. The paper presents a new network steganography method called StegSuggest which utilizes suggestions generated by Google Suggest as a hidden data carrier. The detailed description of the method’s idea is backed up with the analysis of the network traffic generated by the Google Suggest to prove its feasibility. The traffic analysis was also performed to discover the occurrence of two TCP options: Window Scale and Timestamp which StegSuggest uses to operate. Estimation of method steganographic bandwidth proves that it is possible to insert 100 bits of steganogram into every suggestions list sent by Google Suggest service.
💡 Research Summary
The paper introduces StegSuggest, a novel network steganography technique that exploits the Google Suggest service to hide data within normal web traffic. Google Suggest, built on AJAX, sends frequent asynchronous HTTP GET requests as a user types a query and receives a list of popular completions in HTTP 200 responses. The authors captured LAN traffic over several weeks and found that an average user generates about 61 searches per day, each involving roughly seven HTTP requests, providing ample cover traffic for covert communication.
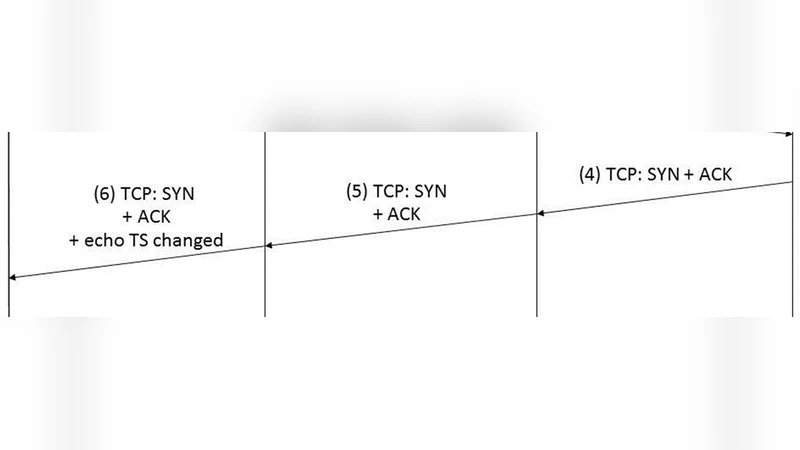
StegSuggest operates on two layers. First, it uses TCP SYN packet options—Window Scale (WS) and Timestamp (TS)—to signal the start and end of a hidden session. Analysis of the captured traffic showed that about 60 % of SYN packets contain WS and 26 % contain TS, with TS always accompanied by WS, making these options a reliable covert signaling channel.
Second, the method embeds secret bits directly into the HTTP response body. The Google Suggest server returns a list of suggestions (typically 10–12 rows). StegSuggest appends an extra word to each row; these “steg‑suggestions” are selected from a codebook derived from the 4,096 most frequent English words (out of a 5,000‑word frequency list). The words are divided into four groups of 1,024 each, and each group encodes 10 bits (2¹⁰ possibilities). For each suggestion row, one word from each group is randomly chosen, representing a 10‑bit chunk of the steganogram. Consequently, a single suggestion list can carry roughly 100 bits of hidden data, yielding a covert bandwidth of several hundred bits per second under typical user activity.
Four communication scenarios are discussed. The most realistic are (a) where both sender and receiver are intermediate network nodes that capture all Google Suggest traffic within a LAN, and (b) where the receiver is an ordinary Google Suggest client unaware of the covert channel. Scenarios involving the Google server itself as a participant are deemed unlikely.
To avoid detection, the authors ensure that inserted words are among the most common in the language, making them blend with occasional odd or humorous suggestions already present in Google’s output. The codebook is pre‑shared, and the random selection of words prevents a fixed mapping that could be learned by statistical analysis. Moreover, because WS and TS options are routinely present in normal TCP handshakes, their use does not raise alarms. Nonetheless, long‑term traffic analysis could potentially reveal anomalous word frequency patterns.
Performance evaluation demonstrates that each suggestion list can embed about 100 bits, translating to a covert channel capacity of several hundred bits per second—significantly higher than many image‑based steganography schemes, which are limited to a few hundred bytes per file. Given Google Suggest’s global popularity, the technique poses a realistic threat for data exfiltration or command‑and‑control communications.
In conclusion, StegSuggest showcases how widely used web services and standard TCP features can be combined to create high‑capacity, low‑detectability steganographic channels. The paper suggests future work on detection mechanisms, dynamic codebook management, and adaptation to encrypted (HTTPS) traffic.
Comments & Academic Discussion
Loading comments...
Leave a Comment