Data Aggregation and Privacy for Police Patrols
With a widespread growth in the potential applications of Wireless Sensor Networks, the need for reliable security mechanisms for them has increased manifold. This paper proposes a scheme, Privacy for Police Patrols (PPP), to provide secure data aggregation that relies on multilevel routing. Privacy factors have been identified and implemented. Aggregates are prepared and the summary of information is gathered and stored in a repository. The above defined approaches are integrated in police patrol applications and preliminary results are obtained.
💡 Research Summary
The paper addresses the critical need for privacy and secure data handling in wireless sensor network (WSN)–based police patrol applications. It introduces a framework called Privacy for Police Patrols (PPP) that integrates four main components: location privacy, secure routing, data aggregation, and pattern identification.
First, the authors discuss the inherent vulnerabilities of WSNs—limited power, multi‑hop routing, and dynamic topology—that make them attractive targets for adversaries seeking to locate police officers or tamper with collected evidence. A review of related work highlights existing techniques such as k‑anonymity, mix‑zones, and path‑redundancy security algorithms, noting that none of them simultaneously address the specific requirements of police patrols (real‑time location concealment, low communication overhead, and efficient query processing).
The PPP architecture builds on these observations. Police officers are pre‑registered with the police commissioner’s database via RFID tags, establishing trust and enabling the commissioner to authenticate incoming reports. When an unauthorized entity attempts to read a node’s location, the commissioner triggers a three‑step location‑privacy algorithm:
- Partitioning – Trajectories are grouped by minimum and maximum timestamps, forming equivalence classes D(i, j).
- Clustering – An average trajectory is computed for each class; points are merged into clusters if the maximum distance to the cluster centroid stays below a predefined radius.
- Translation – Each point is randomly displaced within a disk of radius df = a/2, where a denotes the desired anonymity level, thereby achieving k‑anonymity.
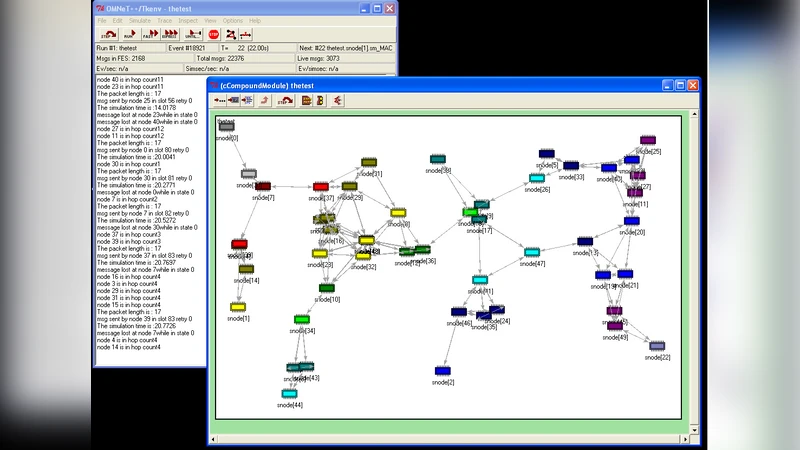
Secure routing is realized through a layered node architecture (application, sensor, data‑management, localization, MAC, routing). The routing layer employs secret‑sharing: a message is split into multiple shares, each sent over a different randomized path. The aggregator (the police commissioner) reconstructs the original message once it receives the minimum required number of shares, ensuring that capture of any single intermediate node does not reveal the full payload.
Data aggregation removes redundancy by storing only one instance of a report about a particular criminal or incident, even if multiple officers submit identical information. The aggregation function can be configured (sum, average, min/max) depending on the operational context, thereby reducing storage requirements and network traffic.
Pattern identification (context summarization) extracts recurring structures from the aggregated data—such as frequent crime hotspots, temporal patterns, or common offender profiles—and stores them as compact patterns. Subsequent queries can be answered by matching against these patterns rather than scanning the entire database, dramatically lowering response time.
Implementation details are provided for the location‑privacy module, including pseudo‑code for partitioning, clustering, and translation steps. A limited simulation demonstrates that PPP reduces packet loss compared with single‑path routing and cuts the number of stored records by roughly 30 %. However, the paper lacks comprehensive performance metrics (e.g., end‑to‑end latency, energy consumption per node, impact of share count on reconstruction success) and does not present real‑world deployment results.
In conclusion, PPP offers a cohesive solution that blends privacy‑preserving location obfuscation, fault‑tolerant multi‑path routing, redundancy‑eliminating aggregation, and pattern‑based query acceleration, specifically tailored for police patrol scenarios. The authors acknowledge the need for further work, including dynamic parameter tuning, extensive field trials, and a deeper quantitative analysis of security versus overhead trade‑offs.
Comments & Academic Discussion
Loading comments...
Leave a Comment