A Review on Elliptic Curve Cryptography for Embedded Systems
Importance of Elliptic Curves in Cryptography was independently proposed by Neal Koblitz and Victor Miller in 1985.Since then, Elliptic curve cryptography or ECC has evolved as a vast field for public key cryptography (PKC) systems. In PKC system, we use separate keys to encode and decode the data. Since one of the keys is distributed publicly in PKC systems, the strength of security depends on large key size. The mathematical problems of prime factorization and discrete logarithm are previously used in PKC systems. ECC has proved to provide same level of security with relatively small key sizes. The research in the field of ECC is mostly focused on its implementation on application specific systems. Such systems have restricted resources like storage, processing speed and domain specific CPU architecture.
💡 Research Summary
The paper presents a comprehensive review of Elliptic Curve Cryptography (ECC) with a focus on its suitability for embedded systems, which are characterized by limited memory, processing power, and energy budgets. It begins by contrasting traditional public‑key cryptosystems based on integer factorisation (RSA) or the discrete logarithm problem (Diffie‑Hellman) with ECC, emphasizing that ECC achieves comparable security with much shorter key lengths (e.g., a 160‑bit ECC key provides roughly the same security as a 1024‑bit RSA key). This reduction in key size translates directly into lower storage requirements and faster arithmetic, making ECC an attractive choice for resource‑constrained devices such as IoT sensors, smart cards, mobile phones, and wearable health monitors.
The authors then review the mathematical foundations required for ECC. Section 2 covers modular arithmetic and finite‑field theory, describing operations in prime fields GF(p) and binary extension fields GF(2^m). It explains why binary fields are often preferred in hardware because their elements can be represented as bit‑polynomials and reduced using irreducible trinomials or pentanomials. Section 3 introduces the Weierstrass equation of an elliptic curve, the discriminant condition, and the geometric interpretation of point addition and point doubling. The algebraic formulas for λ, x₃, and y₃ are given for both distinct points and the tangent case.
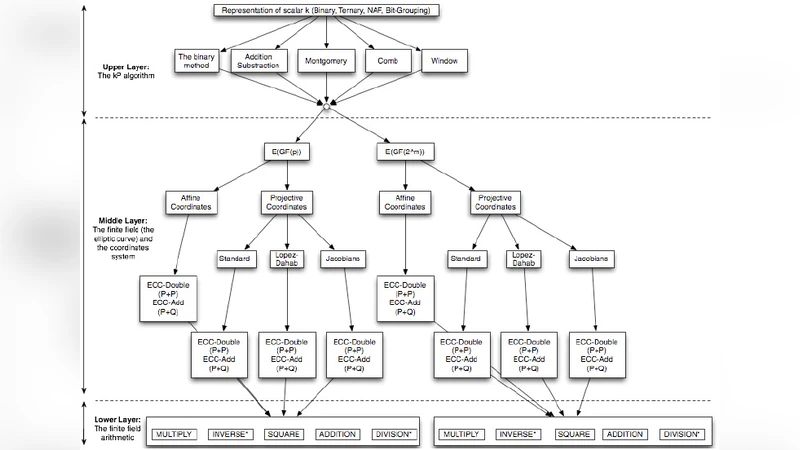
Section 4 explains the security basis of ECC: the Elliptic Curve Discrete Logarithm Problem (ECDLP). The core operation is scalar multiplication Q = k·P, which is performed by repeated point addition and doubling. The paper outlines the hierarchy of ECC arithmetic: scalar multiplication at the top, built from EC‑Add and EC‑Double, which in turn rely on finite‑field addition, subtraction, multiplication, squaring, and inversion. Since field inversion is the most expensive primitive, many implementations replace it with projective or Jacobian coordinates to avoid explicit division.
Section 5 surveys a set of algorithmic techniques that accelerate ECC on constrained platforms. The Karatsuba method reduces the number of polynomial multiplications at the cost of extra additions, which is beneficial when multiplication is significantly slower than addition. The Itoh‑Tsujii algorithm transforms an inversion in an optimal extension field into a subfield inversion followed by a few multiplications, dramatically cutting inversion latency. The de Rooij window method improves on the naïve binary double‑and‑add by processing multiple bits of the scalar at once, reducing the average number of group operations by roughly a factor of four. Montgomery modular multiplication is highlighted for its ability to perform modular reduction without explicit division, often yielding a five‑fold speedup in modular multiplication. The authors stress that the best performance is achieved by carefully combining these techniques with an appropriate coordinate system (affine, projective, Jacobian) and field representation (binary vs. prime).
Section 6 discusses the choice of finite fields and standard curve parameters. It compares prime‑field curves (NIST P‑256, P‑384) with binary‑field curves (NIST B‑163, B‑233) and newer standardized families such as Brainpool and Curve25519. The paper notes that binary curves align well with bit‑serial hardware, while prime curves benefit from fast integer arithmetic on general‑purpose CPUs. Domain parameters (a, b, base point G, order n) are presented, and the importance of using vetted, standardized curves to avoid hidden weaknesses is emphasized.
Section 7 addresses practical design considerations for embedding ECC in real devices. Topics include key‑size selection versus required security level, memory layout for point coordinates, side‑channel resistance (constant‑time implementations, scalar blinding), power‑aware algorithm scheduling, and the trade‑offs between software‑only solutions and hardware accelerators (ASICs, FPGAs). The authors cite several commercial deployments—smart cards using ECDSA for authentication, TLS on embedded web servers, secure bootloaders for microcontrollers, and vehicle‑to‑infrastructure communication using ECDH key exchange—to illustrate that ECC is already mature enough for production use.
In the conclusion, the paper reaffirms that ECC uniquely satisfies the security‑performance balance demanded by modern embedded applications. It calls for further research in three areas: (1) ultra‑lightweight ECC algorithms tailored for ultra‑low‑power microcontrollers, (2) post‑quantum‑resistant alternatives such as supersingular isogeny‑based key exchange, and (3) streamlined protocol stacks that integrate ECC primitives with minimal code footprint. By providing a full spectrum view—from mathematical theory through algorithmic optimization to system‑level design—the review serves as a valuable roadmap for researchers and engineers aiming to secure the next generation of embedded and IoT devices with elliptic curve cryptography.
Comments & Academic Discussion
Loading comments...
Leave a Comment