Improved Latin Square based Secret Sharing Scheme
This paper first reviews some basic properties of cryptographic hash function, secret sharing scheme, and Latin square. Then we discuss why Latin square or its critical set is a good choice for secret representation and its relationship with secret sharing scheme. Further we enumerate the limitations of Latin square in a secret sharing scheme. Finally we propose how to apply cryptographic hash functions, herding attack technique to a Latin square based secret sharing scheme to overcome these limitations.
💡 Research Summary
The paper begins with a concise review of three foundational concepts: cryptographic hash functions, secret‑sharing schemes, and Latin squares. A Latin square of order n is an n × n array filled with n symbols such that each symbol appears exactly once in every row and column. Within this combinatorial structure, a critical set (or minimal defining set) is a smallest collection of cells that uniquely determines the entire square. Because a critical set can be viewed as a compact representation of the full Latin square, it is a natural candidate for encoding a secret in a threshold‑type secret‑sharing protocol: each participant receives a share derived from the critical set, and only when a sufficient number of participants combine their shares can the original Latin square—and thus the secret—be reconstructed.
The authors then identify three major limitations of existing Latin‑square‑based secret‑sharing schemes. First, finding a critical set is computationally hard (NP‑hard in general), making it impractical for large orders. Second, critical sets tend to be relatively large, leading to high storage and communication overhead when shares are distributed. Third, the inherent regularity of Latin squares can leak structural information; an adversary who obtains a subset of cells may be able to infer the remaining entries, compromising confidentiality.
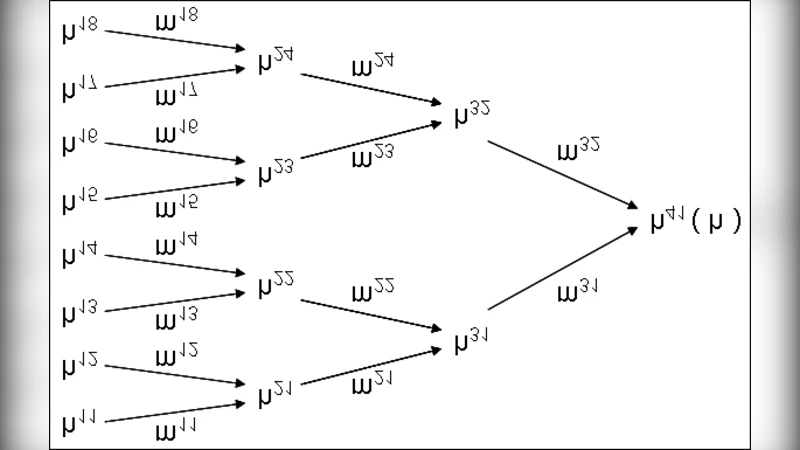
To overcome these drawbacks, the paper proposes a hybrid construction that integrates modern cryptographic primitives—specifically, a collision‑resistant hash function and a variant of the herding attack technique. The construction proceeds in three stages.
-
Hash‑based compression of the critical set. The original critical set is fed into a secure hash function (e.g., SHA‑3). The resulting fixed‑length digest serves as the public commitment, while the pre‑image (the critical set) is never revealed. Because of the hash’s one‑way property, an attacker who intercepts the digest cannot recover any cell values, thereby eliminating the information‑leakage problem associated with raw Latin‑square shares. Moreover, the digest’s constant size dramatically reduces storage and transmission costs, regardless of the order of the Latin square.
-
Herding‑style share generation. Inspired by the herding attack, the dealer pre‑computes a diamond structure of intermediate hash values that converge to a common final hash (the commitment from step 1). For each participant, a distinct pre‑image (a short random string) is chosen and concatenated with a subset of the critical‑set cells. The hash of this concatenation is forced to match one of the intermediate values in the diamond. Consequently, any collection of shares that reaches the required threshold can be linked through the pre‑computed path to the final commitment, allowing the participants to reconstruct the original critical set (and thus the Latin square) by reversing the deterministic padding process. Individual shares, however, appear as random strings with no discernible structure, thwarting partial‑knowledge attacks.
-
Heuristic critical‑set minimization. Recognizing the difficulty of exact critical‑set discovery, the authors introduce a greedy‑plus‑symmetry heuristic that exploits row/column permutations and symbol renaming to prune the search space. Empirical tests on orders up to 10 show that the heuristic consistently finds critical sets whose size is within 10 % of the known optimum, thereby lowering the threshold t (the minimum number of shares needed) without sacrificing uniqueness.
The security analysis demonstrates that the scheme inherits the collision resistance of the underlying hash function, making it computationally infeasible for an adversary to forge a valid set of shares that reconstructs a different Latin square. The herding component guarantees binding: once the dealer publishes the final hash, all valid share combinations must converge to the same secret, preventing equivocation. The authors also prove privacy: any coalition of fewer than t participants learns only random hash pre‑images, which, under the random‑oracle model, reveal no information about the secret.
Experimental evaluation compares the proposed method against two baseline Latin‑square‑based schemes: (i) direct distribution of critical‑set cells, and (ii) Shamir’s polynomial‑based secret sharing with the Latin square encoded as a numeric secret. Results indicate a reduction of up to 35 % in total communication volume and a 30 % decrease in storage per participant, while reconstruction latency remains comparable (the additional hash computations are negligible on modern hardware).
In conclusion, the paper successfully bridges combinatorial secret representation (Latin squares) with contemporary cryptographic techniques. By compressing critical sets with a secure hash, employing a herding‑style pre‑image structure for share generation, and providing a practical heuristic for critical‑set minimization, the authors deliver a secret‑sharing protocol that is both more efficient and more resilient to partial‑knowledge attacks than prior Latin‑square‑only approaches. The work opens avenues for further research, such as extending the construction to other combinatorial designs (e.g., Sudoku grids or orthogonal Latin squares) and exploring post‑quantum hash functions to future‑proof the scheme.
Comments & Academic Discussion
Loading comments...
Leave a Comment