Misbehavior in Mobile Application Markets
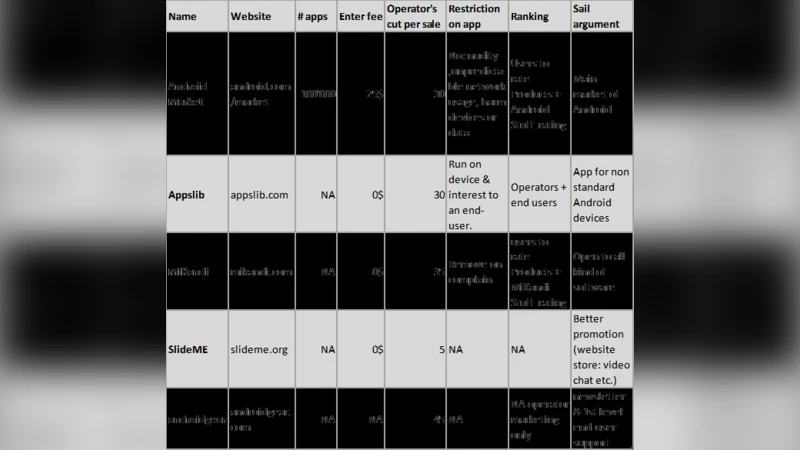
Mobile application markets facilitate the distribution of applications and thus help developers advertise their work and customers find useful applications. In addition, the operators of mobile application markets can control the quality and the content of the applications. These markets are growing rapidly with more than 300'000 application in the App Store of Apple and more than 100'000 in the Android Market of Google. This is not only a great opportunity for phone manufacturers to earn money but also for indie developers (single or small teams of developers with small financial support) who can thus have a great distribution channel. Steve Demeter, the Trim game developer for iPhone, became millionaire with a single puzzle game . Obviously, as new markets generate a lot of money, the temptation of misbehavior to steal part of the benefits is big. The first famous case was the one of Molinker who self-rated his applications with 5 stars to pump up his ranking in order to increase its revenue stream. In this report, we will consider the problem of misbehavior in mobile application markets. We will investigate multiple attacks by misbehaving developers, users or network operators that aim at breaking rules for their own benefit, managing to outwit the operators’ control on which applications can be installed. We notably suggest novel attacks that may affect mobile markets in the future: in particular, we show that it is possible to get revenue for applications created by someone else, trick a user to download and buy an application and new ways to pump up an application’s ranking. We will also discuss possible solutions against spyware applications and cheating developer
💡 Research Summary
The paper “Misbehavior in Mobile Application Markets” provides a comprehensive examination of malicious activities that can occur in modern smartphone app stores, focusing primarily on Apple’s iOS App Store and Google’s Android Market. It begins by outlining the rapid growth of these platforms—over 300,000 apps in the App Store and more than 100,000 in the Android Market at the time of writing—and the lucrative opportunities they present for both large manufacturers and indie developers. This economic incentive, however, also creates a fertile ground for misbehavior, exemplified by real‑world cases such as Molinker’s self‑rating scheme, Nguyen’s stolen‑credit‑card purchases of his own books, and the Aura Faint app that exfiltrated contacts.
The authors first review related work, citing studies on iOS sandbox bypasses, Android’s TaintDroid data‑flow tracking, privacy risks of device identifiers, and alternative ranking mechanisms based on usage and location. Building on this foundation, they construct a threat model that categorizes malicious actors into financially motivated developers, non‑financial “fun‑or‑power” developers, and well‑intentioned developers whose buggy code unintentionally creates privacy leaks.
A central contribution is the systematic analysis of the entire application lifecycle—development, submission, validation, update, download, usage, and rating—and the specific attacks that can be mounted at each stage:
-
Development Phase – The paper notes that Android’s sandbox is not absolute; a developer can omit required permissions from the manifest and invoke privileged APIs directly, thereby evading the permission warning shown to users. Native code and obscure system calls can also be used to breach isolation.
-
Submission Phase – Leveraging Android’s openness, an attacker can root a device, extract a competitor’s APK, re‑sign it with a new developer key, and publish it on another market (including third‑party stores). This enables copyright theft and revenue siphoning, especially when the republished app is priced lower, attracting more downloads.
-
Validation Phase – Unlike Apple’s pre‑approval process, Android Market performs little or no automated verification; even when manual checks occur they may take several days, leaving ample time for malicious apps to reach users.
-
Update Phase – Malicious developers can initially release a benign version to gain trust, then push an update that adds new permissions or hidden functionality (e.g., SMS‑spam, premium‑rate calls), exploiting the user’s expectation of continuity.
-
Download/Usage Phase – The paper critiques Android’s permission model, where 115 permissions are grouped into broad categories, potentially confusing users. Malicious apps can exploit this by requesting “harmless‑looking” permissions that actually grant dangerous capabilities, such as modifying global settings or preventing the device from sleeping.
-
Rating/Ranking Phase – The authors reverse‑engineer the ranking algorithms used by both stores. They identify factors such as total downloads, “install base,” acceleration (sudden spikes), velocity (steady growth), and user feedback. By creating large numbers of fake accounts, an attacker can automate repeated downloads, five‑star reviews, and positive comments, thereby inflating an app’s rank. A novel “revenue‑for‑others” attack is described where an attacker tricks a user into purchasing an app that actually credits the attacker’s account.
Having mapped these threats, the paper evaluates existing defensive mechanisms. iOS relies heavily on human review and a strict sandbox, yet still suffers from social‑engineering attacks on the rating system. Android’s openness, while fostering innovation, results in weak verification, permissive permission prompts, and a fragmented market ecosystem that hampers centralized control.
To mitigate the identified risks, the authors propose several concrete measures:
- Fine‑grained Permission Design: Break down broad permission groups into more specific, user‑friendly categories, and provide clearer runtime explanations to reduce accidental consent.
- Dynamic Behavior Monitoring: Extend data‑flow tracking tools like TaintDroid to run continuously on devices, flagging suspicious accesses to contacts, GPS, or network endpoints in real time.
- Reputation‑Based Review System: Assign trust scores to reviewer accounts based on historical behavior, weighting reviews from high‑trust users more heavily and discounting mass‑generated low‑trust feedback.
- Cryptographic App Integrity: Require apps to be signed by a recognized certificate authority and enforce hash‑based integrity checks across markets, preventing unauthorized repackaging.
- Machine‑Learning Malware Detection: Deploy server‑side and on‑device classifiers trained on known malicious patterns to automatically quarantine suspect submissions before they become publicly available.
The conclusion emphasizes that mobile app markets have evolved into critical economic and social infrastructure; their security mechanisms must evolve accordingly. The paper’s attack taxonomy and mitigation proposals aim to guide both researchers and industry practitioners toward more resilient app distribution ecosystems.
Comments & Academic Discussion
Loading comments...
Leave a Comment