Development of mechanism for enhancing data security in quantum cryptography
Nowadays security in communication is increasingly important to the network communication because many categories of data are required restriction on authorization of access, modify, delete and insert. Quantum cryptography is one of the solutions that use property of polarization to ensure that transmitted data is not tampered. The research paper provides the mechanism that enhances the data security in quantum cryptography during exchange of information. In first phase detailed explanation of Quantum key distribution’s BB84 protocol is given. BB84 protocol is used as the basis for the mechanism. In next phase the proposed mechanism is explained. The proposed mechanism combines BB84 protocol at two levels, from sender to receiver and then from receiver to sender. Moreover, a logic circuit is used to combine the bits hence to reduce the probability of eavesdropping. The key obtained can be used to exchange the information securely further it can help in encryption and decryption of crucial data. Double level BB84 mechanism will help in information reconciliation as well as privacy amplification. In future the proposed mechanism will be very beneficial where unconditional security is required during key and other secret information exchange
💡 Research Summary
The paper addresses the growing need for secure data transmission by proposing an enhancement to quantum key distribution (QKD) based on the BB84 protocol. The authors introduce a “double‑BB84” scheme in which the BB84 protocol is applied twice—first from Alice to Bob and then from Bob back to Alice—combined with a simple logical circuit that processes pairs of bits before they are encoded onto photon polarizations.
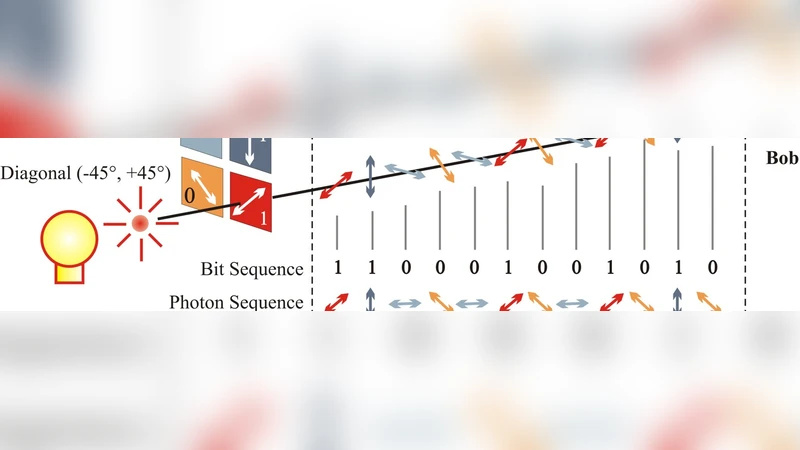
In the first stage, Alice generates a random binary string, groups the bits into pairs, and passes each pair through a logic gate whose truth table swaps the two bits only when they differ (00→00, 01→10, 10→01, 11→11). The transformed pairs are then encoded onto single photons using randomly chosen rectilinear (+) or diagonal (×) bases, as in standard BB84, and sent to Bob. Bob measures each photon with a randomly chosen basis, after which Alice and Bob publicly compare the bases they used. Bits measured in matching bases are kept; the rest are discarded. Bob then applies the inverse of the logic gate to recover the original bit pairs.
The second stage targets the bits that were discarded in the first round. Bob now acts as the sender, re‑encoding the mismatched pairs (or a subset thereof) using BB84 again, while Alice measures with her pre‑agreed bases. After the basis reconciliation, additional matching bits are obtained and combined with the first‑stage key. The authors illustrate the process with a 16‑bit example: the first round yields 8 matching bits, the second round adds 4 more, giving a final 12‑bit secret key (75 % of the original bits).
To evaluate security, the authors perform a probabilistic analysis on a hypothetical 2 880‑bit transmission. In standard BB84, an eavesdropper (Eve) who intercepts photons and measures them in a random basis would, on average, learn 720 bits (50 % of the raw key). In the proposed scheme, because bits are processed in pairs and the logic gate introduces four possible combinations, the probability that Eve’s basis matches both Alice’s and Bob’s choices drops to 1/4, leading to an estimated 90 bits (≈25 %) of information leakage. The paper therefore claims a security improvement from 50 % to 75 % confidentiality.
The authors also discuss information reconciliation and privacy amplification. They argue that the double‑BB84 process inherently provides reconciliation (by discarding mismatched bits) and that standard privacy‑amplification techniques—such as applying a universal hash function to the reconciled key—can be used to further reduce Eve’s knowledge.
While the concept of applying BB84 twice and inserting a lightweight bit‑pair transformation is novel, the paper exhibits several critical shortcomings. First, the logical circuit is trivial and does not address realistic quantum channel imperfections such as photon loss, detector dark counts, or multi‑photon emissions. Second, the security analysis assumes a very simplistic eavesdropping model (random basis measurement) and ignores more sophisticated attacks like intercept‑resend, photon‑number‑splitting, or coherent attacks that exploit the structure of the double‑BB84 exchange. Third, the impact on key generation rate, quantum bit error rate (QBER), and the overhead of the second BB84 round are not quantified; the example with 16 bits is far too small to provide statistically meaningful conclusions. Fourth, no experimental implementation or numerical simulation beyond the toy example is presented, leaving the practical feasibility of synchronizing the logic circuit, basis choices, and inverse operations unverified. Finally, the claim of “unconditional security” is not supported by a rigorous information‑theoretic proof; the security improvement is derived from a basic probability argument rather than a formal composable security framework.
In summary, the paper proposes an interesting double‑BB84 architecture combined with a simple bit‑pair swapping circuit to reduce the amount of information an eavesdropper can obtain. However, the analysis lacks depth, the assumptions are overly optimistic, and the absence of experimental validation limits the contribution to a conceptual proposal. Future work would need to incorporate realistic channel models, detailed error correction and privacy‑amplification design, comprehensive security proofs against general attacks, and experimental demonstration to substantiate the claimed security gains.
Comments & Academic Discussion
Loading comments...
Leave a Comment