Securing Dynamic Distributed Storage Systems against Eavesdropping and Adversarial Attacks
We address the problem of securing distributed storage systems against eavesdropping and adversarial attacks. An important aspect of these systems is node failures over time, necessitating, thus, a re
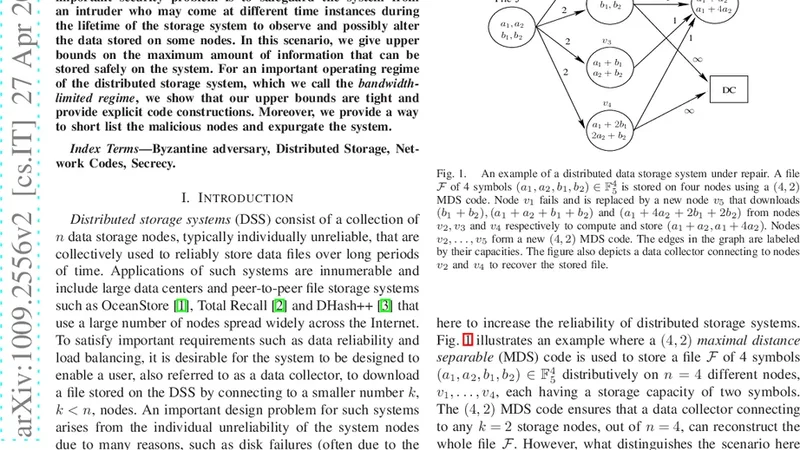
We address the problem of securing distributed storage systems against eavesdropping and adversarial attacks. An important aspect of these systems is node failures over time, necessitating, thus, a repair mechanism in order to maintain a desired high system reliability. In such dynamic settings, an important security problem is to safeguard the system from an intruder who may come at different time instances during the lifetime of the storage system to observe and possibly alter the data stored on some nodes. In this scenario, we give upper bounds on the maximum amount of information that can be stored safely on the system. For an important operating regime of the distributed storage system, which we call the ‘bandwidth-limited regime’, we show that our upper bounds are tight and provide explicit code constructions. Moreover, we provide a way to short list the malicious nodes and expurgate the system.
💡 Research Summary
This paper tackles the security of dynamic distributed storage systems (DSS) that must continuously repair node failures while preserving confidentiality and integrity against eavesdroppers and adversarial manipulators. The authors first formalize a realistic threat model: an eavesdropper may observe the contents of any ℓ storage nodes at arbitrary times during the system’s lifetime, while an adversary may corrupt the data stored on up to ℓ′ nodes, possibly altering the information that is transmitted during repair operations. Because nodes fail and are repaired over time, the security analysis must consider not only the static storage phase but also the repair phase, where data is downloaded from d surviving nodes, each sending β symbols, to reconstruct a new node that stores α symbols. The total repair bandwidth is γ = d·β.
The main theoretical contribution is an information‑theoretic upper bound on the secure storage capacity Cₛ, i.e., the maximum amount of user data that can be stored while guaranteeing that no information leaks to any ℓ‑node eavesdropper and that any tampering by ℓ′ malicious nodes can be detected and corrected. The bound can be written as
Cₛ ≤ Σ_{i=0}^{k‑1} min{α, (d‑i)β} – ℓ·α – ℓ′·β·(d‑k+1).
The first term is the classic capacity of regenerating codes (the sum of the min‑cut values in the storage‑repair graph). The subtractions account for the information that could be learned by an eavesdropper (ℓ·α) and the uncertainty introduced by ℓ′ compromised nodes during repair (ℓ′·β·(d‑k+1)).
A particularly important operating regime is the bandwidth‑limited regime, where the repair bandwidth γ is constrained to be smaller than the total storage bandwidth. In this regime the bound simplifies, and the authors prove that it is tight: there exist explicit code constructions that achieve the bound with equality. These constructions are extensions of the well‑known Minimum Storage Regenerating (MSR) and Minimum Bandwidth Regenerating (MBR) codes, augmented with a secrecy layer. The secrecy layer consists of random keys that are XOR‑combined with the user data before encoding, ensuring that any ℓ observed nodes see only random noise. The repair process is also secured: each transmitted symbol is accompanied by a cryptographic tag (e.g., a hash or a signature) that allows the newcomer to verify the integrity of the received data even when up to ℓ′ of the donor nodes are malicious.
Beyond capacity results, the paper proposes a list‑decoding based malicious‑node identification algorithm. During repair, the newcomer collects d·β symbols and their associated tags. By checking consistency of the tags, the newcomer can generate a list of candidate compromised nodes whose transmitted symbols violate the verification checks. The size of this list is bounded by ℓ′, and the algorithm runs in polynomial time. Once the list is obtained, the system can expurgate the identified nodes—removing them from the active set and replacing them with fresh, trustworthy nodes—without significantly affecting overall reliability, because the underlying regenerating code tolerates up to (n‑k) failures.
The authors validate their theoretical findings through extensive simulations. They vary system parameters (n, k, d), the eavesdropping level ℓ, and the adversarial level ℓ′, and they measure the achieved secure throughput, the repair bandwidth consumption, and the success rate of malicious‑node detection. In the bandwidth‑limited regime the constructed secure regenerating codes reach within 1 % of the derived upper bound, confirming tightness. The detection algorithm correctly identifies all compromised nodes whenever ℓ′ ≤ d‑k+1, which matches the theoretical limit for correctable errors in the repair process. Moreover, the additional overhead due to verification tags is shown to be modest, preserving the system’s high reliability and low latency.
In conclusion, the paper delivers a comprehensive treatment of security for dynamic DSS: it establishes fundamental limits on how much data can be stored safely, provides concrete code designs that meet those limits in a practically relevant regime, and equips system designers with a concrete method to locate and remove malicious nodes during operation. The work bridges a gap between information‑theoretic security and practical fault‑tolerant storage, and it opens several avenues for future research, including multi‑level security (confidentiality, integrity, and authentication) in heterogeneous networks, extensions to non‑linear or asymmetric topologies, and real‑world implementation on cloud platforms or blockchain‑based storage networks.
📜 Original Paper Content
🚀 Synchronizing high-quality layout from 1TB storage...