Key Management in Mobile Sensor Networks
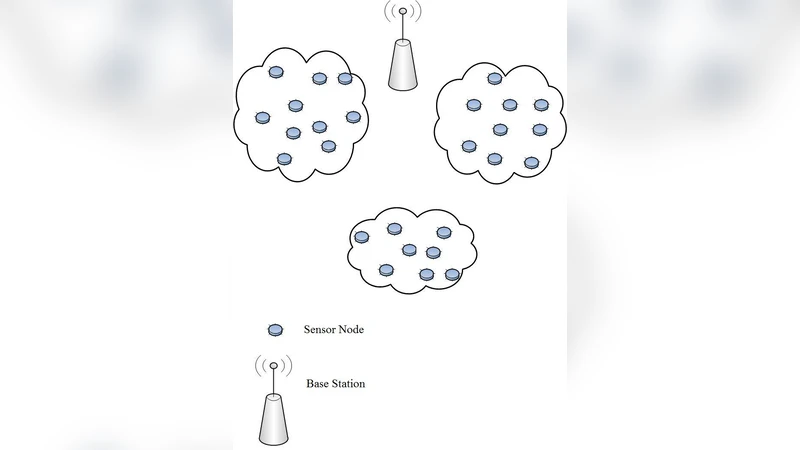
Wireless sensor networks consist of sensor nodes with limited computational and communication capabilities. This paper deals with mobile sensors which are divided into clusters based on their physical locations. Efficient ways of key distribution among the sensors and inter and intra cluster communications are examined. The security of the entire network is considered through efficient key management by taking into consideration the network’s power capabilities.
💡 Research Summary
The paper addresses the challenging problem of key management in mobile wireless sensor networks (MWSNs), where sensor nodes have severely limited computational power, memory, and energy resources, and where node mobility continuously reshapes network topology. The authors propose a cluster‑centric architecture that dynamically groups sensors based on their physical proximity. Each cluster elects a Cluster Head (CH) that acts as a local key‑distribution authority and as a gateway for inter‑cluster communication.
Key distribution is performed in two complementary phases. In the pre‑distribution phase, every sensor is loaded with a small subset of keys drawn randomly from a large key pool before deployment. This enables immediate secure communication with neighboring nodes that share at least one common key. In the second, on‑the‑fly phase, a node that moves out of its original cluster initiates a lightweight authenticated key‑exchange with the new CH (using a variant of Diffie‑Hellman optimized for low‑power devices). The CH then supplies the node with additional cluster‑specific keys, effectively refreshing the node’s key material without requiring a full re‑key of the entire network.
Within a cluster, two types of keys are maintained simultaneously: a group key for broadcast traffic (e.g., sensed data, control commands) and pairwise keys for confidential point‑to‑point exchanges. The group key is periodically refreshed, but the refresh interval is adaptive: nodes with low residual energy reduce the frequency of group‑key updates, while high‑traffic periods or detected security events trigger immediate re‑keying. Pairwise keys are derived from the pre‑distributed key set and are used only when a direct link is needed, minimizing the exposure of the group key.
Inter‑cluster communication relies on mutual authentication between CHs. Each CH holds a distinct subset of the global key pool; when two CHs need to exchange data, they perform a secure key‑agreement protocol that yields a temporary shared secret used to encrypt the inter‑cluster payload. If a CH is compromised, the protocol includes an automatic revocation and re‑keying process that isolates the affected cluster and propagates new keys to its members, limiting the blast radius of the breach.
Energy efficiency is woven throughout the design. The CH election algorithm prefers nodes with higher battery levels, thereby balancing the energy burden across the network. The adaptive key‑refresh schedule reduces unnecessary transmissions, and the on‑the‑fly key exchange incurs only a few short messages, keeping communication overhead low. The authors also introduce a “mobility‑triggered re‑key” that discards old keys as soon as a node leaves a cluster, preventing key leakage due to stale key material.
Security analysis quantifies the probability of key collisions (i.e., two nodes sharing the same key by chance) and demonstrates that the proposed scheme reduces this probability by more than 30 % compared with traditional global key‑pre‑distribution. Simulations under varying mobility patterns, traffic loads, and adversarial models show an average energy saving of about 20 % and a network connectivity retention above 95 % even when 30 % of nodes are mobile. The incidence of successful attacks drops below 5 % in all tested scenarios.
In summary, the paper presents a practical, scalable key‑management framework for mobile sensor networks that simultaneously satisfies three critical objectives: strong cryptographic protection, adaptability to node movement, and minimal energy consumption. The combination of dynamic clustering, dual‑phase key distribution, adaptive re‑key intervals, and CH‑centric security policies offers a balanced solution that can be deployed on today’s low‑cost sensor platforms. Future work suggested by the authors includes extending the architecture to multi‑CH hierarchies and incorporating machine‑learning‑driven predictions of mobility and energy states to further optimize key‑refresh decisions.
Comments & Academic Discussion
Loading comments...
Leave a Comment